Intel CEO Bestows Optimism Despite Pandemic Perils
Perhaps the most interesting thing about the letter was what wasn’t said. There was not one...
Tech Bytes: Using HashiCorp’s Terraform Cloud For Collaboration And Governance (Sponsored)
Terraform Cloud, from HashiCorp, is a SaaS-based service that provides governance, auditing, and collaboration for your infrastructure-as-code initiatives. Our guest to walk us through Terraform Cloud is Rosemary Wang, Developer Advocate at HashiCorp.
The post Tech Bytes: Using HashiCorp’s Terraform Cloud For Collaboration And Governance (Sponsored) appeared first on Packet Pushers.
Tech Bytes: Using HashiCorp’s Terraform Cloud For Collaboration And Governance (Sponsored)
Terraform Cloud, from HashiCorp, is a SaaS-based service that provides governance, auditing, and collaboration for your infrastructure-as-code initiatives. Our guest to walk us through Terraform Cloud is Rosemary Wang, Developer Advocate at HashiCorp.T-Mobile US Closes Sprint Merger
The combination of the nation's third- and fourth-largest operators is the biggest shakeup to hit...
KDDI, SoftBank Target 5G at Rural Japan
They will share base stations used to transmit the 5G signals in rural areas and collaborate on the...
Day Two Cloud 042: AWS Networking Part 1: Performance
Today on Day Two Cloud, Ned Bellavance and Ethan Banks answer listener questions about AWS Networking. They get into the nitty gritty on core AWS networking concepts including placement groups for EC2 instances, Elastic Network Adapters, network and application load balancing, Route 53, and more.Day Two Cloud 042: AWS Networking Part 1: Performance
Today on Day Two Cloud, Ned Bellavance and Ethan Banks answer listener questions about AWS Networking. They get into the nitty gritty on core AWS networking concepts including placement groups for EC2 instances, Elastic Network Adapters, network and application load balancing, Route 53, and more.
The post Day Two Cloud 042: AWS Networking Part 1: Performance appeared first on Packet Pushers.
SDxCentral’s Top 10 Articles — March 2020
Cisco Networking lessons learned during COVID-19; AT&T slashed more jobs; Microsoft topped...
Comcast’s Jeff Lewis: ‘Job No. 1 Is Customer Experience’
Jeff Lewis sat down to share his thoughts on ActiveCore products, the benefits for customers, and...
SD-WAN and Technical Debt

Back during Networking Field Day 22, I was having a fun conversation with Phil Gervasi (@Network_Phil) and Carl Fugate (@CarlFugate) about SD-WAN and innovation. I mentioned that it was fascinating to see how SD-WAN companies kept innovating but that bigger, more established companies that had bought into SD-WAN seemed to be having issues catching up. As our conversation continued I realized that technical debt plays a huge role in startup culture in all factors, not just with SD-WAN. But we’ll use SD-WAN as an example here to focus our discussion.
Any Color You Want In Black
Big companies have investments in supply chains. They have products that are designed in a certain way because it’s the least expensive way to develop the project or it involves using technology developed by the company that gives them a competitive advantage. Think about something like the Cisco Nexus 9000-series switches that launched with Cisco ACI. Every one of them came with the Insieme ASIC that was built to accelerate the policy component of ACI. Whether or not you wanted to use ACI or Insieme in your deployment, you were getting the ASIC in the switch.
Policies like this Continue reading
Python String-Mutable Data Type
We all know that there are two types of Data types in Python ,i.e Mutable and other is immutable. In simple words, Mutable object can be change after its created whereas immutable object can’t
String,tuple,int,float,bool is example of immutable whereas list,dict and set are example of mutable data type.
Lets take an example of string data type :
We have string S=’Sujil’ and we need to change char ‘j’ to ‘n’ to make S=’Sunil’
>>> S ='Sunil'
>>> S ='Sujil'
>>> S=[2] = 'n'
File "<input>", line 1
SyntaxError: can't assign to literal
We will get the SyntaxError , means we cannot change the defined string as string is Mutable data type .
Is there any way to change the Mutable data type string S=’Sujil’ to S=’Sunil’.
Yes , we can so the same . There is 3 way to do as below , choose the best way for urself.
Way 1:
>>> S ='Sujil'
>>> S
'Sujil'
>>> S = S[:2]+'n' +S[3:]
>>> S
'Sunil'
>>> type(S)
<class 'str'>
Way 2:
>>> S = 'Sujil'
>>> S
'Sujil'
>>> type(S)
<class 'str'>
>>> S =S.replace('j','n')
>>> S
'Sunil'
Way 3:
>>> S = 'Sujil'
>>> type(S)
<class 'str'>
>>> Continue readingDisinformation: The Invisible Sword Dividing Society

Supermarkets have finally restocked their toilet paper in Hong Kong after weeks of panic buying when a rumor about toilet paper shortage due to closure of factories in China went viral. The toilet paper shortage did happen, but it was because of panic buying, not because of factory closure in China. How did the rumor spread? Was disinformation one of the culprits?
On February 25th, the Internet Society Hong Kong Chapter organized a Hong Kong Internet Governance Forum Roundtable on disinformation. On the panel was Eric Wishart, News Management Member at Agence France-Presse (AFP); Masato Kajimoto from the Journalism and Media Studies Centre of the University of Hong Kong; George Chen, Head of Public Policy (Hong Kong, Taiwan and Mongolia) at Facebook; and Charles Mok, a local Legislative Councillor.
Did someone spread “disinformation” about toilet paper shortage?
While a lot of people think that the rumor on toilet paper shortage is a piece of disinformation or fake news, Masato reminded us that it actually is not. Disinformation is information that is deliberately created to deceive people, which is different from “misleading information.” In the case of panic buying toilet paper, some people made an opinion about toilet paper production Continue reading
Tips to prevent Zoom Bombing, Security and Conference Hygience

Zoom Meeting IDs are sequential ten digit numbers. People are randomly creating IDs and dropping into Zoom conferences often using abusive language, displaying pornagraphic images or worse. Yes, Zoom has poor security posture generally. The design approach appears makes it easy to use as possible while compromising security. Compared to other conferencing platforms, it does […]
The post Tips to prevent Zoom Bombing, Security and Conference Hygience appeared first on EtherealMind.
Announcing the Beta for WARP for macOS and Windows


Last April 1 we announced WARP — an option within the 1.1.1.1 iOS and Android app to secure and speed up Internet connections. Today, millions of users have secured their mobile Internet connections with WARP.
While WARP started as an option within the 1.1.1.1 app, it's really a technology that can benefit any device connected to the Internet. In fact, one of the most common requests we've gotten over the last year is support for WARP for macOS and Windows. Today we're announcing exactly that: the start of the WARP beta for macOS and Windows.
What's The Same: Fast, Secure, and Free
We always wanted to build a WARP client for macOS and Windows. We started with mobile because it was the hardest challenge. And it turned out to be a lot harder than we anticipated. While we announced the beta of 1.1.1.1 with WARP on April 1, 2019 it took us until late September before we were able to open it up to general availability. We don't expect the wait for macOS and Windows WARP to be nearly as long.
The WARP client for macOS and Windows relies on the Continue reading
Introducing 1.1.1.1 for Families

Two years ago today we announced 1.1.1.1, a secure, fast, privacy-first DNS resolver free for anyone to use. In those two years, 1.1.1.1 has grown beyond our wildest imagination. Today, we process more than 200 billion DNS requests per day making us the second largest public DNS resolver in the world behind only Google.

Yesterday, we announced the results of the 1.1.1.1 privacy examination. Cloudflare's business has never involved selling user data or targeted advertising, so it was easy for us to commit to strong privacy protections for 1.1.1.1. We've also led the way supporting encrypted DNS technologies including DNS over TLS and DNS over HTTPS. It is long past time to stop transmitting DNS in plaintext and we're excited that we see more and more encrypted DNS traffic every day.
1.1.1.1 for Families

Since launching 1.1.1.1, the number one request we have received is to provide a version of the product that automatically filters out bad sites. While 1.1.1.1 can safeguard user privacy and optimize efficiency, it is designed for direct, fast DNS resolution, not for blocking or Continue reading
DC. Part 17. Emulating a hyper-scale datacentre with Microsoft Azure SONiC as Docker containers (SONiC-P4).
Hello my friend,
In the previous article from the networking series we have started the discussion about SONiC (Software for Open Networking in Clouds), which is a network infrastructure behind Microsoft Azure cloud. Today we continue this discussion from slightly different angle: we will emulate the whole data centre infrastructure end-to-end with leafs, spines and servers.
Network automation training – boost your career
Don’t wait to be kicked out of IT business. Join our network automation training to secure your job in future. Come to NetDevOps side.
How does the training differ from this blog post series? Here you get the basics and learn some programming concepts in general, whereas in the training you get comprehensive set of knowledge with the detailed examples how to use Python for the network and IT automation. You need both.
Thanks
Big thanks to a colleague of mine, Michael Salo, who shared with me useful insights on namespaces networking in Linux.
Brief description
Previously we’ve run the SONiC on the Mellanox SN2010 switch, which was provided to me by the Mellanox team to do some reviews. I’ve returned it back, so I started looking for the opportunities to run the Microsoft Azure Continue reading
Cloudflare now supports security keys with Web Authentication (WebAuthn)!


We’re excited to announce that Cloudflare now supports security keys as a two factor authentication (2FA) method for all users. Cloudflare customers now have the ability to use security keys on WebAuthn-supported browsers to log into their user accounts. We strongly suggest users configure multiple security keys and 2FA methods on their account in order to access their apps from various devices and browsers. If you want to get started with security keys, visit your account's 2FA settings.
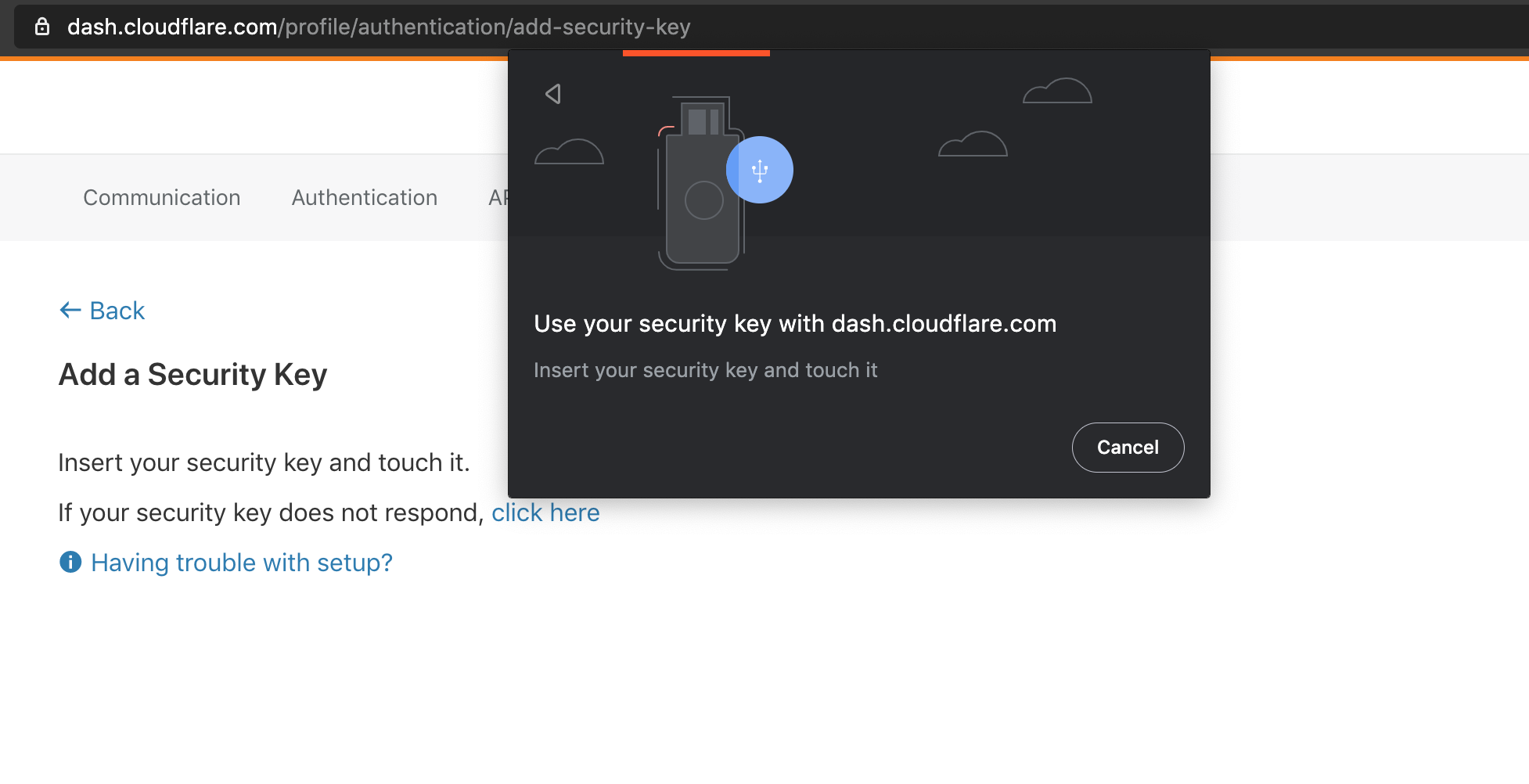
What is WebAuthn?
WebAuthn is a standardized protocol for authentication online using public key cryptography. It is part of the FIDO2 Project and is backwards compatible with FIDO U2F. Depending on your device and browser, you can use hardware security keys (like YubiKeys) or built-in biometric support (like Apple Touch ID) to authenticate to your Cloudflare user account as a second factor. WebAuthn support is rapidly increasing among browsers and devices, and we’re proud to join the growing list of services that offer this feature.
To use WebAuthn, a user registers their security key, or “authenticator”, to a supporting application, or “relying party” (in this case Cloudflare). The authenticator then generates and securely stores a public/private keypair on the device. The keypair Continue reading
Vendor Marketing: Theory and Reality
Every time I’m complaining about the stupidities $vendors are trying to sell us, someone from vendorland saddles a high horse and starts telling me how I got it all wrong, for example:
It is a duty of a pre-sales, consultant, vendor representative to inform the customer about the risk.
When you stop laughing (and it’s not an April Fools’ joke), here’s how the reality of that process looks like (straight from one of my readers):
I remember when the VM guys and their managers were telling me (like they had discovered the solutions to all of ours problems) about “with VXLAN we can move a machine from one country to another, and keep having service with the same IP” … while looking at me with the “I’m so smart” face… and me thinking shit… I’m doomed :) … I don’t even want to start explaining … but in the long run I had to anyway.