CenturyLink Expands Edge Services With Network Storage
“We think of the whole AWS Outposts initiative as very complementary to everything we’re...
Automating Scale-Out IP Fabrics with the Adaptive Cloud Fabric’s New Layer 2 Features
Pluribus customers have been building and automating scalable data center network infrastructure for years using the uniquely powerful architecture of...Enea’s Roland Steiner Discusses Mobile Vendors, UDM, and Why the SaaS Model is Just Better
Roland Steiner’s role as senior VP at Enea has put him at the crest of the 5G wave and for User...
Rural Development Special Interest Group Organizes Internet Connectivity Tag 2019

In November, the Internet Society Rural Development Special Interest Group (RD SIG) organized an event called the Internet Connectivity Tag 2019 in Bangalore, India to deliberate on emerging technologies for the Internet of Things (IoT) and security, and what this means for rural development in India.
RD SIG invited a number of distinguished speakers to the event, many of whom are Chapter members. Adarsh B.U., for instance, is the president of RD SIG, a member of the Bangalore Chapter, and the program chair of the Hyderabad Chapter, which is currently being established. B.U. has been recognized as one of the top eight IoT thought leaders for his contribution towards the advancement of IoT in India. At the event, he organized an interactive, hands-on session with Contiki OS and Cooja Simulator.
Leading up to the event, RD SIG issued a call for fellowship applications from which over 300 expressions of interest were received. Out of the applicants, seven fellows from different parts of India were selected to participate in the event.
Highlights from the event included a presentation by Abhijan Bhattacharyya on IPv6 in the context of 5G for digital convergence. In his talk, he looked at the Continue reading
Disaster Recover and Failure Domains
One of the responses to my Disaster Recovery Faking blog post focused on failure domains:
What is the difference between supporting L2 stretched between two pods in your DC (which everyone does for seamless vMotion), and having a 30ms link between these two pods because they happen to be in different buildings?
I hope you agree that a single broadcast domain is a single failure domain. If not, let agree to disagree and move on - my life is too short to argue about obvious stuff.
Read more ...Thinking about color
Color is my day-long obsession, joy and torment - Claude Monet

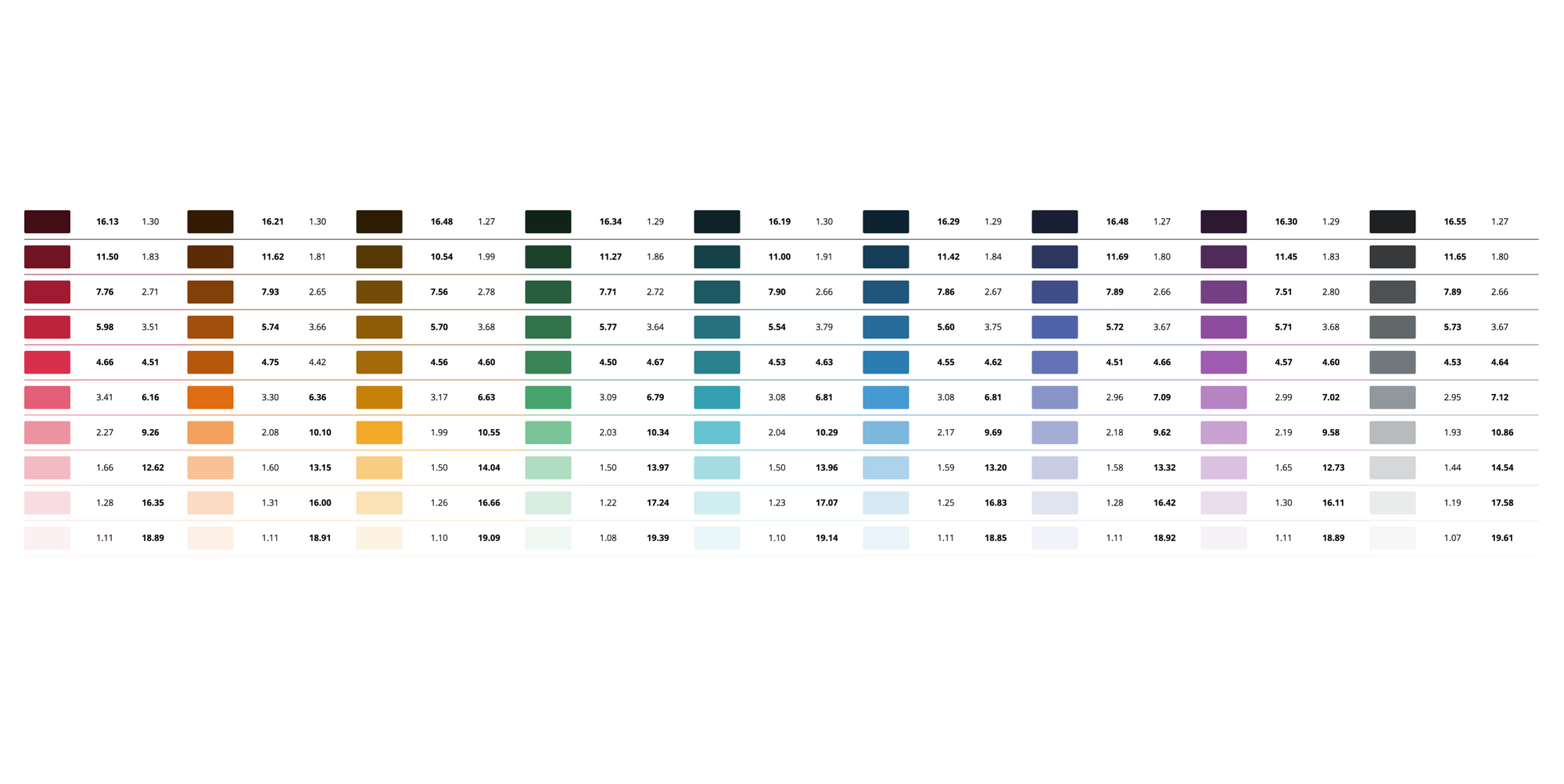
Over the last two years we’ve tried to improve our usage of color at Cloudflare. There were a number of forcing functions that made this work a priority. As a small team of designers and engineers we had inherited a bunch of design work that was a mix of values built by multiple teams. As a result it was difficult and unnecessarily time consuming to add new colors when building new components.
We also wanted to improve our accessibility. While we were doing pretty well, we had room for improvement, largely around how we used green. As our UI is increasingly centered around visualizations of large data sets we wanted to push the boundaries of making our analytics as visually accessible as possible.
Cloudflare had also undergone a rebrand around 2016. While our marketing site had rolled out an updated set of visuals, our product ui as well as a number of existing web properties were still using various versions of our old palette.
Our product palette wasn’t well balanced by itself. Many colors had been chosen one or two Continue reading
Amazon Detective, McAfee Hunt Down the Baddies
McAfee also teased a yet-to-be-released microsegmentation technology to secure contianer runtimes...
AWS Head Bemoans ‘Political Interference’ in JEDI Contract
“If you do a truly objective and detailed apples-to-apples comparison of the platforms, you...
Verizon Beats the Edge Drum With AWS
“We’ve been engaged in quiet or stealth mode with AWS the past 18 months,” Verizon's Bill...
Business Considerations in Implementing an SD-Branch
SD-branch can be molded to a business's needs; however, it's important to consider the roadblocks...