Red Hat Shields IBM’s Woeful Q3
That boost was felt in IBM’s Cloud and Cognitive Software business were most of Red Hat’s...
Locked Up By Lock-In
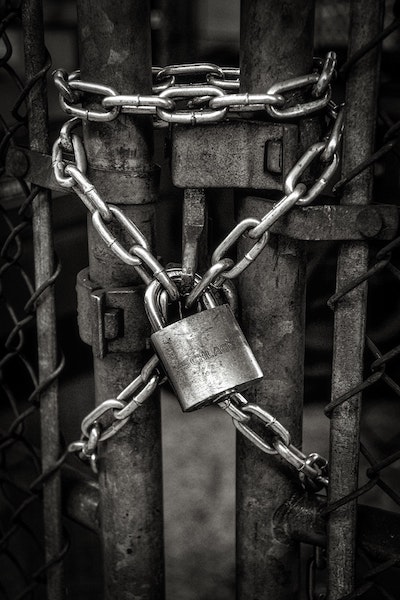
When you start evaluating a solution, you are going to get a laundry list of features and functionality that you are supposed to use as criteria for selection. Some are important, like the ones that give you the feature set you need to get your job done. Others are less important for the majority of use cases. One thing tends to stand out for me though.
Since the dawn of platforms, I believe the first piece of comparison marketing has been “avoids lock-in”. You know you’ve seen it too. For those that may not be completely familiar with the term, “lock-in” describes a platform where all the components need to come from the same manufacturer or group of manufacturers in order to work properly. An example would be if a networking solution required you to purchase routers, switches, access points, and firewalls from a single vendor in order to work properly.
Chain of Fools
Lock in is the greatest asset a platform company has. The more devices they can sell you the more money they can get from you at every turn. That’s what they want. So they’re going to do everything they can to keep you in their ecosystem. Continue reading
Weekly Wrap: AWS Makes It Rain, Extends Credits to Open Source Projects
SDxCentral Weekly Wrap for Oct. 18, 2019: Many have questioned AWS' open source moves; Ericsson...
Usage-based billing with NetFlow and sFlow
The post Usage-based billing with NetFlow and sFlow appeared first on Noction.
You Cannot Have a Public Cloud without Networking
Listening to (some) industry evangelists you would believe that there’s no future in being a networking engineer. After all, all workloads will move into the cloud, and all clients will connect through a universal 5G network… but even if that utopia eventually comes true, you can’t get away from the laws of physics (and the need networking infrastructure).
TL&DR: our new online course will help you master the shiny new world. You can register right now or keep reading ;)
Read more ...Delta Lake Project Raises Linux Foundation Flag
Databricks takes aim at the swamp monsters lurking in data lakes, announcing Delta Lake will fly...
Verizon Picks Lanner to Built Next-Gen uCPEs
The revamped uCPE line is being targeted at SMB deployments and is designed to integrate with...
Ericsson Bribery Settlement Bogs Down Q3 Earnings
"We are ashamed of our historical performance, but we confront the issues head on and we’re now...
SDN for Physical and Virtual Networks in Space- and Cost-Constrained Environments
Part Three of a Five-Part Series on Software-Defined Data Centers in a Multi-Cloud World In my last post, The “Easy...Segment Routing (SR): An Overview
Network operators are facing some fierce new challenges with the emergence of IoT and 5G, along...
IPv6 Buzz 037: Understanding And Working With IPv6 Special Addresses
Today's IPv6 Buzz dives into IPv6 special addresses--what they are, how they're used in production, potential issues, and more.
The post IPv6 Buzz 037: Understanding And Working With IPv6 Special Addresses appeared first on Packet Pushers.