Getting the Unified Cloud Experience
Learn how Lenovo Open Cloud (LOC) provides cloud deployment and cloud management services, and...
Adaptiv Delivers SD-WAN to SkySwitch uCaaS Customers
By leveraging Adaptiv Networks' SD-WAN, SkySwitch aims to capitalize on small-to-medium size...
Understanding Kubernetes Security on Docker Enterprise 3.0

This is a guest post by Javier Ramírez, Docker Captain and IT Architect at Hopla Software. You can follow him on Twitter @frjaraur or on Github.
Docker began including Kubernetes with Docker Enterprise 2.0 last year. The recent 3.0 release includes CNCF Certified Kubernetes 1.14, which has many additional security features. In this blog post, I will review Pod Security Policies and Admission Controllers.
What are Kubernetes Pod Security Policies?
Pod Security Policies are rules created in Kubernetes to control security in pods. A pod will only be scheduled on a Kubernetes cluster if it passes these rules. These rules are defined in the “PodSecurityPolicy” resource and allow us to manage host namespace and filesystem usage, as well as privileged pod features. We can use the PodSecurityPolicy resource to make fine-grained security configurations, including:
- Privileged containers.
- Host namespaces (IPC, PID, Network and Ports).
- Host paths and their permissions and volume types.
- User and group for containers process execution and setuid capabilities inside container.
- Change default containers capabilities.
- Behaviour of Linux security modules.
- Allow host kernel configurations using sysctl.
The Docker Universal Control Plane (UCP) 3.2 provides two Pod Security Policies by default – which is helpful Continue reading
When Persistence Is A Virtue, MRAM Is An Alternative To DRAM And SRAM
Magneto-resistive random access memory (MRAM) is one of those technologies that is often talked about as having the potential to change the computer memory landscape. …
When Persistence Is A Virtue, MRAM Is An Alternative To DRAM And SRAM was written by Michael Feldman at The Next Platform.
T-Mobile US Expects Sprint Merger to Close in Early 2020
“We now expect the merger will be permitted to close in early 2020,” CEO John Legere said on an...
CloudEvents Hits 1.0 Release, Gains CNCF Promotion
The eventing project is backed by cloud heavyweights Amazon, Microsoft, and Google.
Google Cloud ‘Strong’ Q3 Revenue Disappoints Wall Street
Company management did not provide any revenue details specific to its could platform, but...
How to Improve MySQL AWS Performance 2X Over Amazon RDS at The Same Cost
AWS is the #1 cloud provider for open-source database hosting, and the go-to cloud for MySQL deployments. As organizations continue to migrate to the cloud, it’s important to get in front of performance issues, such as high latency, low throughput, and replication lag with higher distances between your users and cloud infrastructure. While many AWS users default to their managed database solution, Amazon RDS, there are alternatives available that can improve your MySQL performance on AWS through advanced customization options and unlimited EC2 instance type support. ScaleGrid offers a compelling alternative to hosting MySQL on AWS that offers better performance, more control, and no cloud vendor lock-in and the same price as Amazon RDS. In this post, we compare the performance of MySQL Amazon RDS vs. MySQL Hosting at ScaleGrid on AWS High Performance instances.
TLDR
Sponsored Post: Fauna, Sisu, Educative, PA File Sight, Etleap, PerfOps, Triplebyte, Stream

Who's Hiring?
- Sisu Data is looking for machine learning engineers who are eager to deliver their features end-to-end, from Jupyter notebook to production, and provide actionable insights to businesses based on their first-party, streaming, and structured relational data. Apply here.
- Triplebyte lets exceptional software engineers skip screening steps at hundreds of top tech companies like Apple, Dropbox, Mixpanel, and Instacart. Make your job search O(1), not O(n). Apply here.
- Need excellent people? Advertise your job here!
Cool Products and Services
- Stateful JavaScript Apps. Effortlessly add state to your Javascript apps with FaunaDB. Generous free tier. Try now!
- Grokking the System Design Interview is a popular course on Educative.io (taken by 20,000+ people) that's widely considered the best System Design interview resource on the Internet. It goes deep into real-world examples, offering detailed explanations and useful pointers on how to improve your approach. There's also a no questions asked 30-day return policy. Try a free preview today.
- PA File Sight - Actively protect servers from ransomware, audit file access to see who is deleting files, reading files or moving files, and detect file copy activity from the server. Historical audit reports Continue reading
Full Stack Journey 035: Testing And Validation For Infrastructure As Code
Today's episode of Full Stack Journey focuses on the benefits of testing and validation for Infrastructure-as-Code (IaC). We discuss types of testing, available tools, and why IaC has value even for smaller shops. My guest is Gareth Rushgrove.Full Stack Journey 035: Testing And Validation For Infrastructure As Code
Today's episode of Full Stack Journey focuses on the benefits of testing and validation for Infrastructure-as-Code (IaC). We discuss types of testing, available tools, and why IaC has value even for smaller shops. My guest is Gareth Rushgrove.
The post Full Stack Journey 035: Testing And Validation For Infrastructure As Code appeared first on Packet Pushers.
Programmatically Creating Kubernetes Manifests
A while ago I came across a utility named jk, which purported to be able to create structured text files—in JSON, YAML, or HCL—using JavaScript (or TypeScript that has been transpiled into JavaScript). One of the use cases was creating Kubernetes manifests. The GitHub repository for jk describes it as “a data templating tool”, and that’s accurate for simple use cases. In more complex use cases, the use of a general-purpose programming language like JavaScript in jk reveals that the tool has the potential to be much more than just a data templating tool—if you have the JavaScript expertise to unlock that potential.
The basic idea behind jk is that you could write some relatively simple JavaScript, and jk will take that JavaScript and use it to create some type of structured data output. I’ll focus on Kubernetes manifests here, but as you read keep in mind you could use this for other purposes as well. (I explore a couple other use cases at the end of this post.)
Here’s a very simple example:
const service = new api.core.v1.Service('appService', {
metadata: {
namespace: 'appName',
labels: {
app: 'appName',
team: 'blue',
},
},
spec: {
selector: Continue readingReining In And Optimizing Cloud Spending
The fundamental advantage of using cloud services to deliver IT resources needed to support daily business operations is the flexibility they allow: on demand applications and instant infrastructure that can be ordered, provisioned, and delivered in minutes without the delays often involved in submitting equivalent requests to internal IT departments or waiting for suitable on-premise architecture to be implemented and configured. …
Reining In And Optimizing Cloud Spending was written by Timothy Prickett Morgan at The Next Platform.
DNS Encryption Explained


The Domain Name System (DNS) is the address book of the Internet. When you visit cloudflare.com or any other site, your browser will ask a DNS resolver for the IP address where the website can be found. Unfortunately, these DNS queries and answers are typically unprotected. Encrypting DNS would improve user privacy and security. In this post, we will look at two mechanisms for encrypting DNS, known as DNS over TLS (DoT) and DNS over HTTPS (DoH), and explain how they work.
Applications that want to resolve a domain name to an IP address typically use DNS. This is usually not done explicitly by the programmer who wrote the application. Instead, the programmer writes something such as fetch("https://example.com/news") and expects a software library to handle the translation of “example.com” to an IP address.
Behind the scenes, the software library is responsible for discovering and connecting to the external recursive DNS resolver and speaking the DNS protocol (see the figure below) in order to resolve the name requested by the application. The choice of the external DNS resolver and whether any privacy and security is provided at all is outside the control of the application. It depends on Continue reading
The Invisible Internet

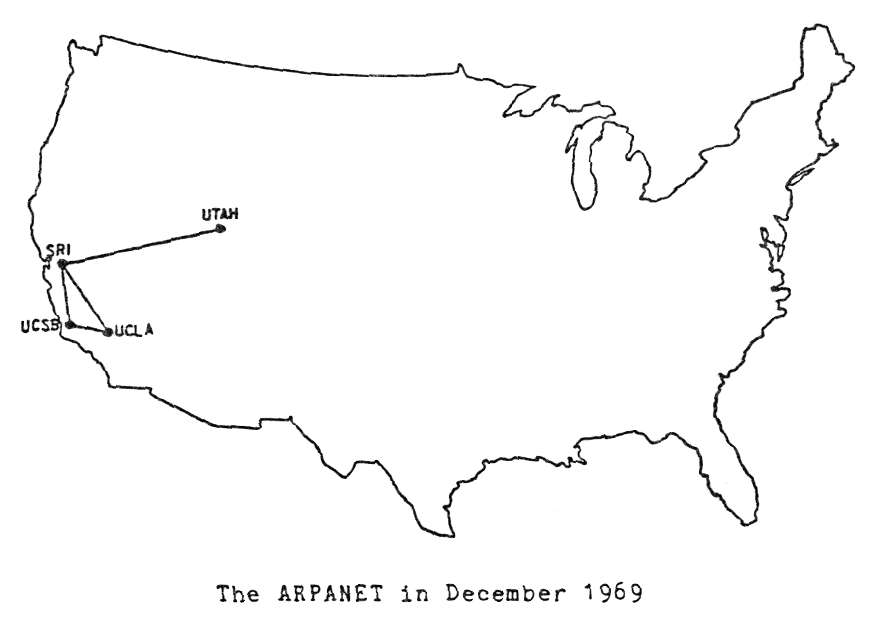
Editor’s Note: Fifty years ago today, on October 29th, 1969, a team at UCLA started to transmit five letters to the Stanford Research Institute: LOGIN. It’s an event that we take for granted now – communicating over a network – but it was historic. It was the first message sent over the ARPANET, one of the precursors to the Internet. UCLA computer science professor Leonard Kleinrock and his team sent that first message. In this anniversary guest post, Professor Kleinrock shares his vision for what the Internet might become.
On July 3, 1969, four months before the first message of the Internet was sent, I was quoted in a UCLA press release in which I articulated my vision of what the Internet would become. Much of that vision has been realized (including one item I totally missed, namely, that social networking would become so dominant). But there was a critical component of that vision which has not yet been realized. I call that the invisible Internet. What I mean is that the Internet will be invisible in the sense that electricity is invisible – electricity has the extremely simple interface of a socket in the wall from which something called Continue reading
Saved: TCP Is the Most Expensive Part of Your Data Center
Years ago Dan Hughes wrote a great blog post explaining how expensive TCP is. His web site is long gone, but I managed to grab the blog post before it disappeared and he kindly allowed me to republish it.
If you ask a CIO which part of their infrastructure costs them the most, I’m sure they’ll mention power, cooling, server hardware, support costs, getting the right people and all the usual answers. I’d argue one the the biggest costs is TCP, or more accurately badly implemented TCP.
Read more ...50 Years of The Internet. Work in Progress to a Better Internet
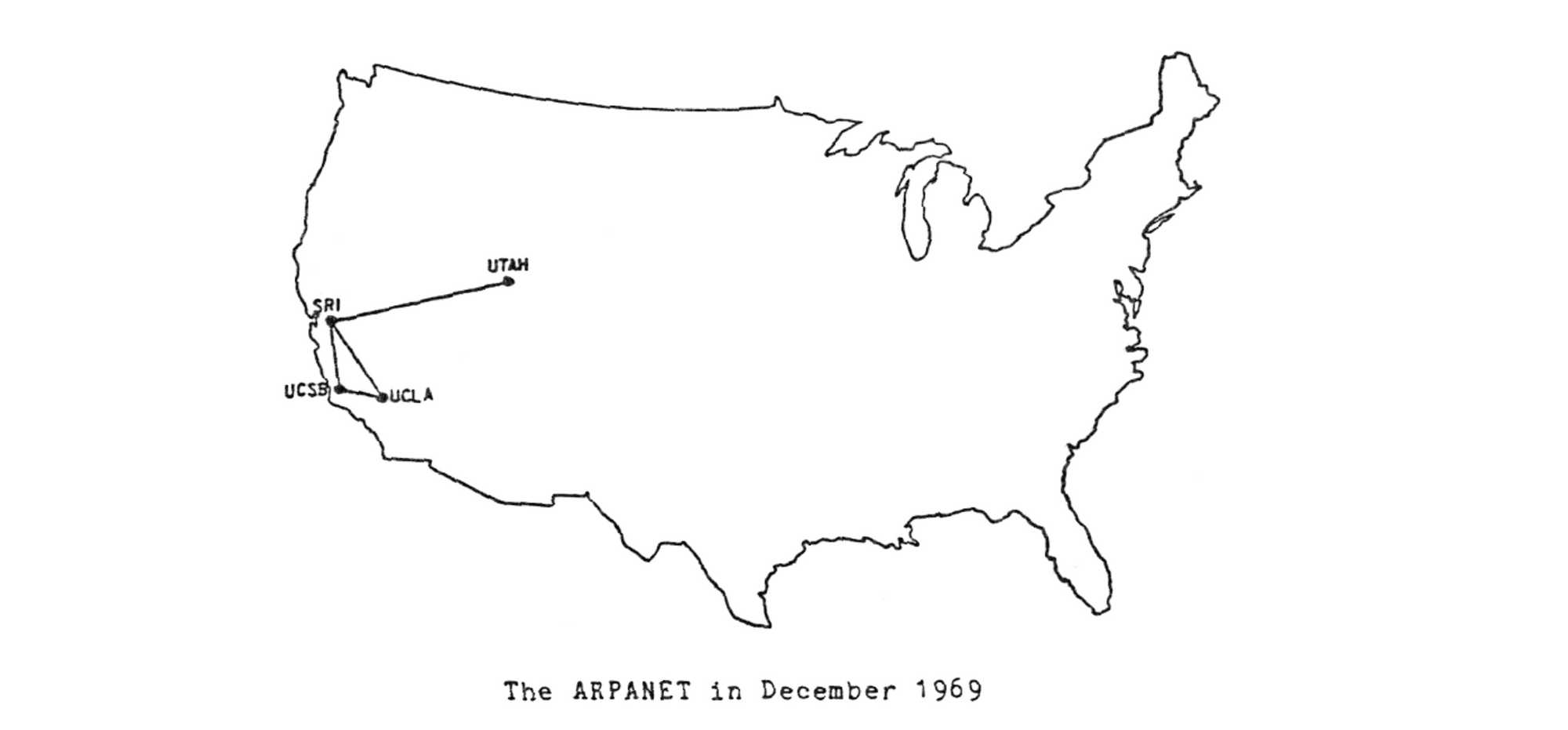
It was fifty years ago when the very first network packet took flight from the Los Angeles campus at UCLA to the Stanford Research Institute (SRI) building in Palo Alto. Those two California sites had kicked-off the world of packet networking, of the Arpanet, and of the modern Internet as we use and know it today. Yet by the time the third packet had been transmitted that evening, the receiving computer at SRI had crashed. The “L” and “O” from the word “LOGIN” had been transmitted successfully in their packets; but that “G”, wrapped in its own packet, caused the death of that nascent packet network setup. Even today, software crashes, that’s a solid fact; but this historic crash, is exactly that — historic.
So much has happened since that day (October 29’th to be exact) in 1969, in fact it’s an understatement to say “so much has happened”! It’s unclear that one blog article would ever be able to capture the full history of packets from then to now. Here at Cloudflare we say we are helping build a “better Internet”, so it would make perfect sense for us to Continue reading
