Protecting Project Galileo websites from HTTP attacks
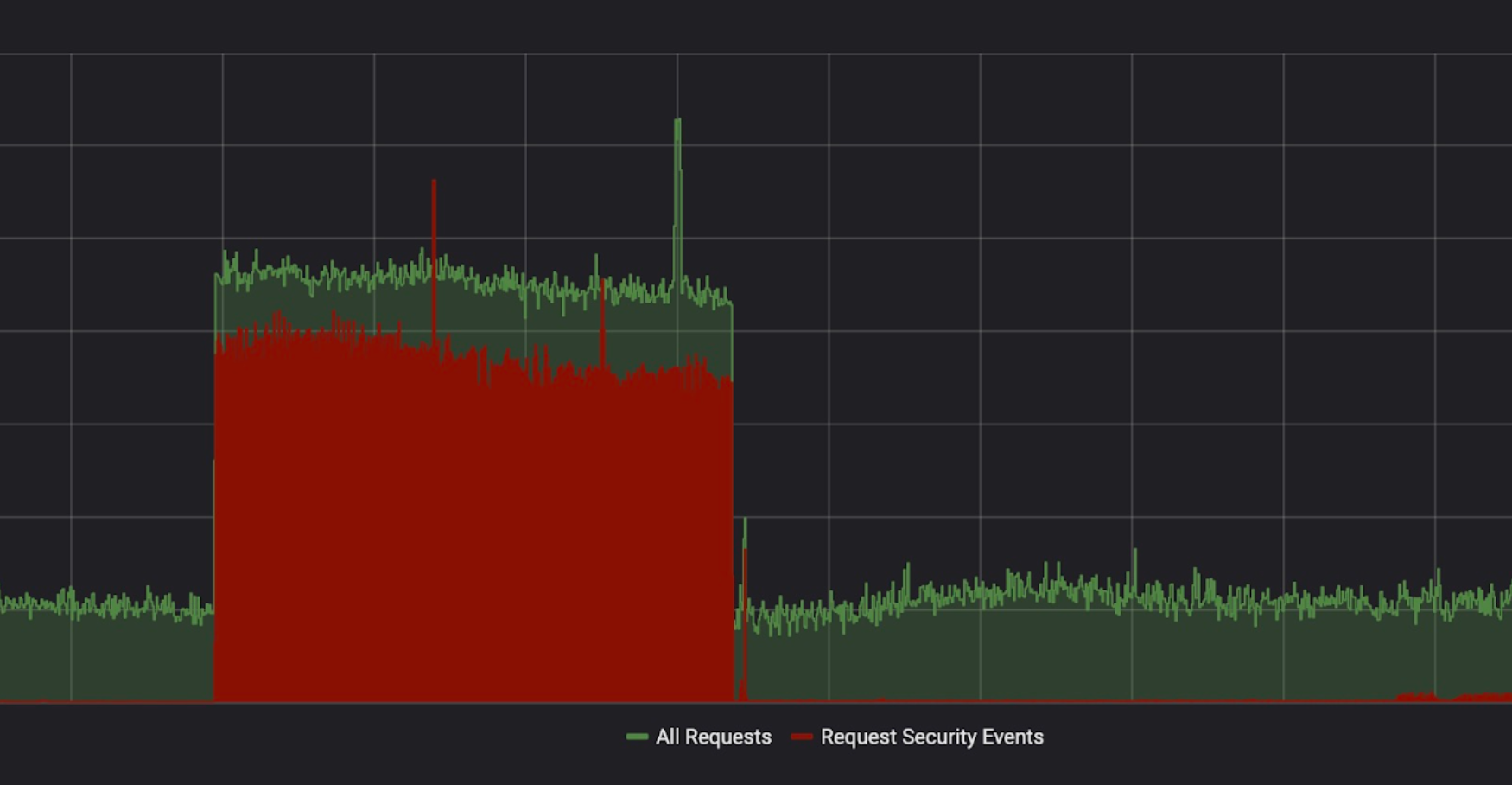
Yesterday, we celebrated the fifth anniversary of Project Galileo. More than 550 websites are part of this program, and they have something in common: each and every one of them has been subject to attacks in the last month. In this blog post, we will look at the security events we observed between the 23 April 2019 and 23 May 2019.
Project Galileo sites are protected by the Cloudflare Firewall and Advanced DDoS Protection which contain a number of features that can be used to detect and mitigate different types of attack and suspicious traffic. The following table shows how each of these features contributed to the protection of sites on Project Galileo.
|
Firewall Feature |
Requests Mitigated |
Distinct originating IPs |
Sites Affected (approx.) |
|
78.7M |
396.5K |
~ 30 |
|
|
41.7M |
1.8M |
~ 520 |
|
|
24.0M |
386.9K |
~ 200 |
|
|
9.4M |
32.2K |
~ 500 |
|
|
4.5M |
163.8K |
~ 200 |
|
|
2.3M |
1.3K |
~ 15 |
|
|
2.0M |
686.7K |
~ 40 |
|
|
1.6M |
360 |
1 |
|
|
623.5K |
6.6K |
~ 15 |
|
|
9.7K |
2.8K |

 In this episode, you’ll hear from Andre Kindness, Principal Analyst, Forrester Research; Jeff...
In this episode, you’ll hear from Andre Kindness, Principal Analyst, Forrester Research; Jeff... Cisco is pushing network operators to view 5G as an opportunity to design their networks around the...
Cisco is pushing network operators to view 5G as an opportunity to design their networks around the... The Spain-based telecom giant plans to offer the service through a virtual network function...
The Spain-based telecom giant plans to offer the service through a virtual network function... The endpoint security company, founded by former McAfee executives, sold 18 million shares priced...
The endpoint security company, founded by former McAfee executives, sold 18 million shares priced... The company's Crosswalk open source framework "codifies" AWS best practices into a single platform.
The company's Crosswalk open source framework "codifies" AWS best practices into a single platform.