Arrcus Joins the 400G Ethernet Switch Party
 The white box OS startup, which is taking on data center big dogs Cisco and Arista, launched its hardware-agnostic operating system last July.
The white box OS startup, which is taking on data center big dogs Cisco and Arista, launched its hardware-agnostic operating system last July.
 The white box OS startup, which is taking on data center big dogs Cisco and Arista, launched its hardware-agnostic operating system last July.
The white box OS startup, which is taking on data center big dogs Cisco and Arista, launched its hardware-agnostic operating system last July.
 One analyst puts the eight-year cloud deal France’s largest bank “around or somewhat above $2 billion.”
One analyst puts the eight-year cloud deal France’s largest bank “around or somewhat above $2 billion.”
Mark Kosters joins Donald and I to talk about the history of the whois system.
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
 StackRox updated its container security platform with additional visibility, profiling, and network management features.
StackRox updated its container security platform with additional visibility, profiling, and network management features.
Welcome to the first episode of Day Two Cloud, a new podcast that punctures the marketing hype and digs into the real work required to make the public cloud work for you. My guest Tim Warner walks us through a real-world application migration to Azure and shares lessons learned on scale, automation, and cost control.
The post Day Two Cloud 001: Building A Business On Azure appeared first on Packet Pushers.
 The two operators agreed to a non-binding agreement and plan to build their own 5G networks in some cities.
The two operators agreed to a non-binding agreement and plan to build their own 5G networks in some cities.
A basic, layered approach to DNS security can dramatically reduce the chances of DNS and BGP-related compromise. Here are three essential, preventative measures that organizations should implement.

Check your domain registration and protect those logins
The post Emergency Directive 19-01, DNS 2FA suggested appeared first on EtherealMind.
 The vendor added new capabilities to its data backup platform that prevent, detect, and respond to ransomware attacks.
The vendor added new capabilities to its data backup platform that prevent, detect, and respond to ransomware attacks.
 The application monitoring company, owned by Cisco, debuted several new products that will help enterprises navigate the complexity of modern environments.
The application monitoring company, owned by Cisco, debuted several new products that will help enterprises navigate the complexity of modern environments.
I’d like to share something with you. Something I learned (the hard way) in my life. Beware the tangled web you weave. There is a price to pay. I didn’t see this when I was in my 20s and 30s. ... Read More ›
The post Oh What a Tangled Web We Weave…… appeared first on Networking with FISH.

Why would a cloud company make its own electricity ?
The post Response: Google putting 1.6 million solar panels in Tennessee and Alabama appeared first on EtherealMind.
Measured adoption of 5G via practical use-cases such as fixed wireless will enable enterprises to get the experience and taste of what it is to come.

As of December 22, 2018, parts of the US Government have “shut down” because of a lapse in appropriation. The shutdown has caused the furlough of employees across the government and has affected federal contracts. An unexpected side-effect of this shutdown has been the expiration of TLS certificates on some .gov websites. This side-effect has emphasized a common issue on the Internet: the usage of expired certificates and their erosion of trust.
For an entity to provide a secure website, it needs a valid TLS certificate attached to the website server. These TLS certificates have both start dates and expiry dates. Normally certificates are renewed prior to their expiration. However, if there’s no one to execute this process, then websites serve expired certificates--a poor security practice.
This means that people looking for government information or resources may encounter alarming error messages when visiting important .gov websites:
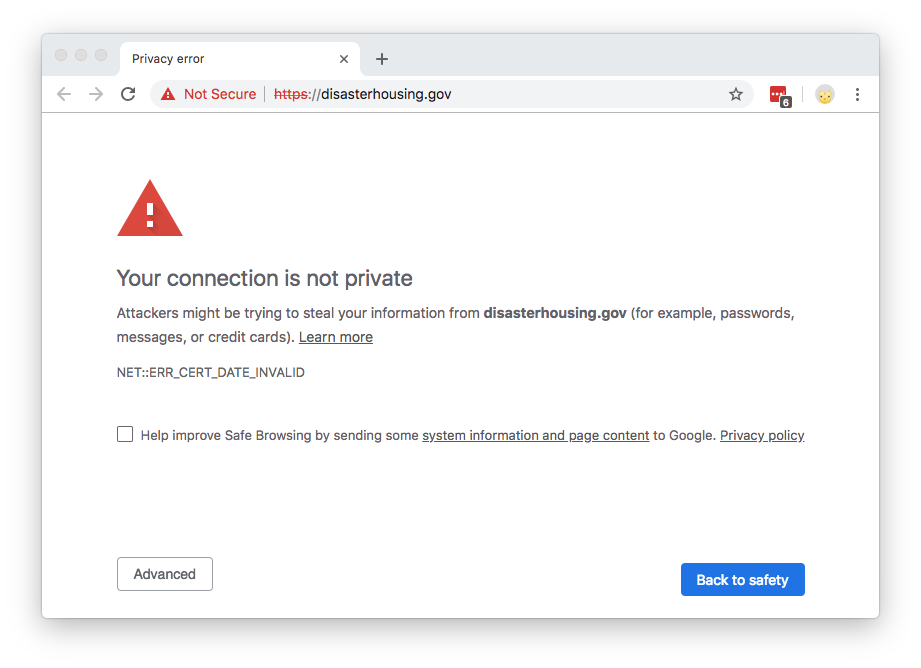
The content of the website hasn’t changed; it’s just the cryptographic exchange that’s invalid (an expired certificate can’t be validated). These expired certificates present a trust problem. Certificate errors often dissuade people from accessing a website, and imply that the site is not to be trusted. Browsers purposefully make it difficult to continue to Continue reading