Spanning The Clouds, Public And Private, With The Kubernetes Stack
Enterprises are looking at a future of multiple clouds and hybrid clouds where they can run not only their new cloud-native applications but also migrate many of their legacy workloads and take advantage of cost savings and the agility that comes with cloud computing. …
Spanning The Clouds, Public And Private, With The Kubernetes Stack was written by Jeffrey Burt at .
Great Lakes Super To Remove Islands Of Compute
It is hard to say for sure, but there is probably as much aggregate computing capacity in the academic supercomputing centers of the world as there are in the big national labs. …
Great Lakes Super To Remove Islands Of Compute was written by Timothy Prickett Morgan at .
Privacy Policy
Effective date: October 19, 2018
HAMY.IO (“us”, “we”, or “our”) operates the https://hamy.io website (hereinafter referred to as the “Service”).
This page informs you regarding our policies concerning the collection, use, and disclosure of personal data when you use our Service and the choices you have associated with that data.
We use your data to provide and improve the Service. By using the Service, you agree to the collection and use of information in accordance with this policy. Unless otherwise defined in this Privacy Policy, the terms used in this Privacy Policy have the same meanings as in our Terms and Conditions, accessible from https://hamy.io
At HAMY.IO, we recognize that privacy of your personal information is important. Here is information on what types of personal information we receive and collect when you use our Service, and how we safeguard your information.
Definitions
- Service: Service is the https://hamy.io website operated by HAMY.IO
- Personal Data: Personal Data means data about a living individual who can be identified from those data (or from those and other information either in our possession or likely to come into our possession).
- Usage Data: Usage Data is data Continue reading
Ericsson Fired 50 People in Corruption Scandal Fallout
 CEO Borje Ekholm said an investigation of the company by the SEC and DOJ started in 2013. The scandal put a damper on otherwise positive third quarter results.
CEO Borje Ekholm said an investigation of the company by the SEC and DOJ started in 2013. The scandal put a damper on otherwise positive third quarter results.
Announcement: Cumulus recognized by both our employees & customers
It’s not every day you get recognized. But to get recognized TWICE in one day? Now that’s a rare experience. We’re thrilled to announce that Cumulus Networks has been recognized with both the FORTUNE 2018 50 Best Small and 100 Medium Size Companies to Work For award, as well as Gartner Customers’ Choice for Data Center Networking.
With recognition like this, we’re taking time to celebrate and appreciate the awesome and talented people we get to work with every day.
Cumulus awarded as a FORTUNE 2018 50 Best Small and 100 Medium Size Companies to Work For
The Fortune award is one of the most prestigious and for good reason — Their rigorous methodology focuses on more than just benefits and office snacks. According to their 2017 methodology statement:
All employees were invited to participate in the survey, which is designed to reveal whether the organization is consistently a great place to work for all its people. Meaning: Do employees trust the people they work for? Are they treated fairly and with respect? Are people proud of their work? Do they enjoy the folks they work with? Are great experiences available to everyone – or does it Continue reading
IPv6 Buzz 011: An IPv6 Address Planning Guide
Today's episode explores the ins and outs of IPv6 address planning, with IPv6 Buzz co-host Tom Coffeen in the guest chair. Tom discusses how to get away from "IPv4 thinking" when planning your v6 transition, and shares his real-world experiences of IPv6 adoption with CDNs and service providers.IPv6 Buzz 011: An IPv6 Address Planning Guide
Today's episode explores the ins and outs of IPv6 address planning, with IPv6 Buzz co-host Tom Coffeen in the guest chair. Tom discusses how to get away from "IPv4 thinking" when planning your v6 transition, and shares his real-world experiences of IPv6 adoption with CDNs and service providers.
The post IPv6 Buzz 011: An IPv6 Address Planning Guide appeared first on Packet Pushers.
DT, Intel, MobiledgeX Lead TIP’s Edge App Developer Project
 The group will produce vendor-neutral APIs and software tools focused on mobile functions running on edge infrastructure.
The group will produce vendor-neutral APIs and software tools focused on mobile functions running on edge infrastructure.
McAfee Uncovers New Security Threat Linked to China
 McAfee also added new products to its Mvision enterprise security portfolio including endpoint detection and response and an integrated data loss prevention policy engine across endpoints, networks, and the cloud.
McAfee also added new products to its Mvision enterprise security portfolio including endpoint detection and response and an integrated data loss prevention policy engine across endpoints, networks, and the cloud.
Encrypt that SNI: Firefox edition
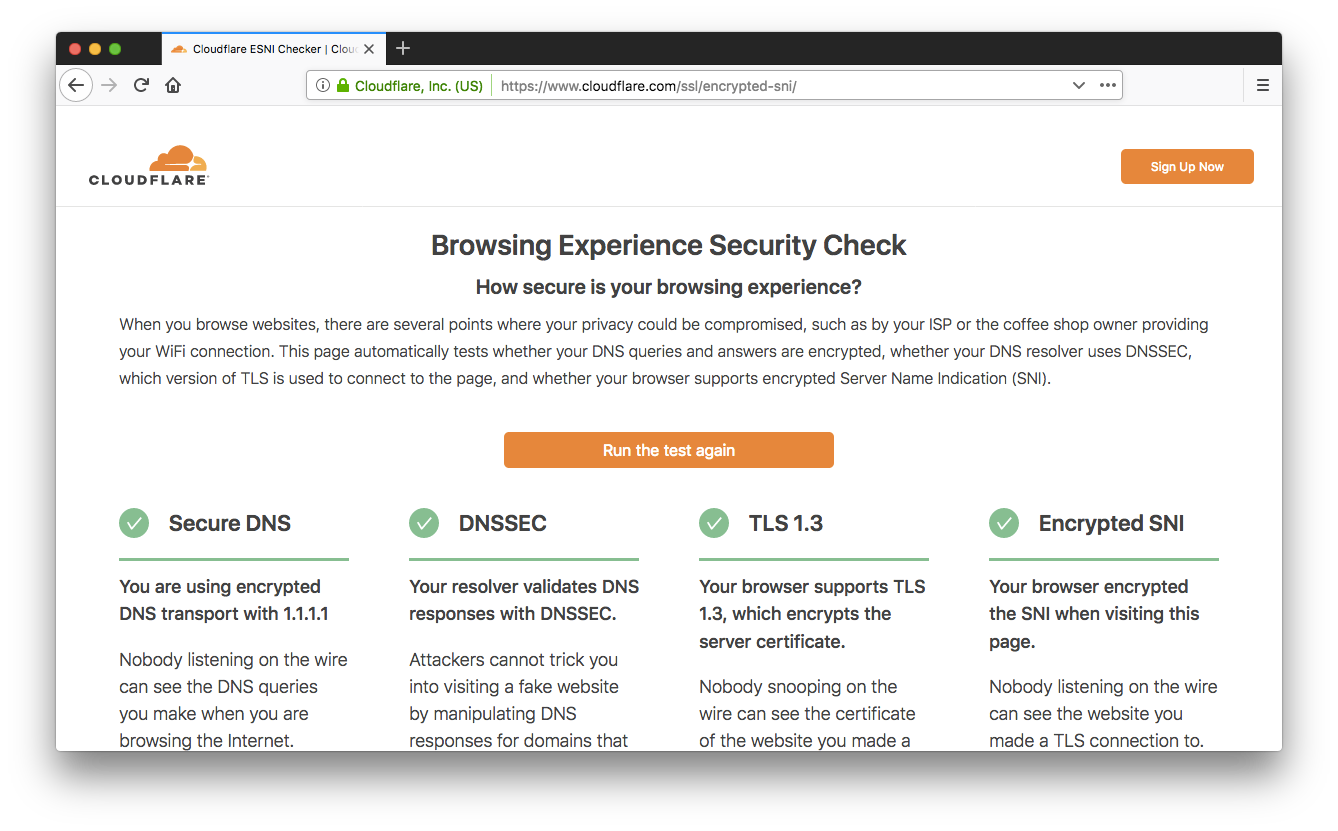
A couple of weeks ago we announced support for the encrypted Server Name Indication (SNI) TLS extension (ESNI for short). As promised, our friends at Mozilla landed support for ESNI in Firefox Nightly, so you can now browse Cloudflare websites without leaking the plaintext SNI TLS extension to on-path observers (ISPs, coffee-shop owners, firewalls, …). Today we'll show you how to enable it and how to get full marks on our Browsing Experience Security Check.

Here comes the night
The first step is to download and install the very latest Firefox Nightly build, or, if you have Nightly already installed, make sure it’s up to date.
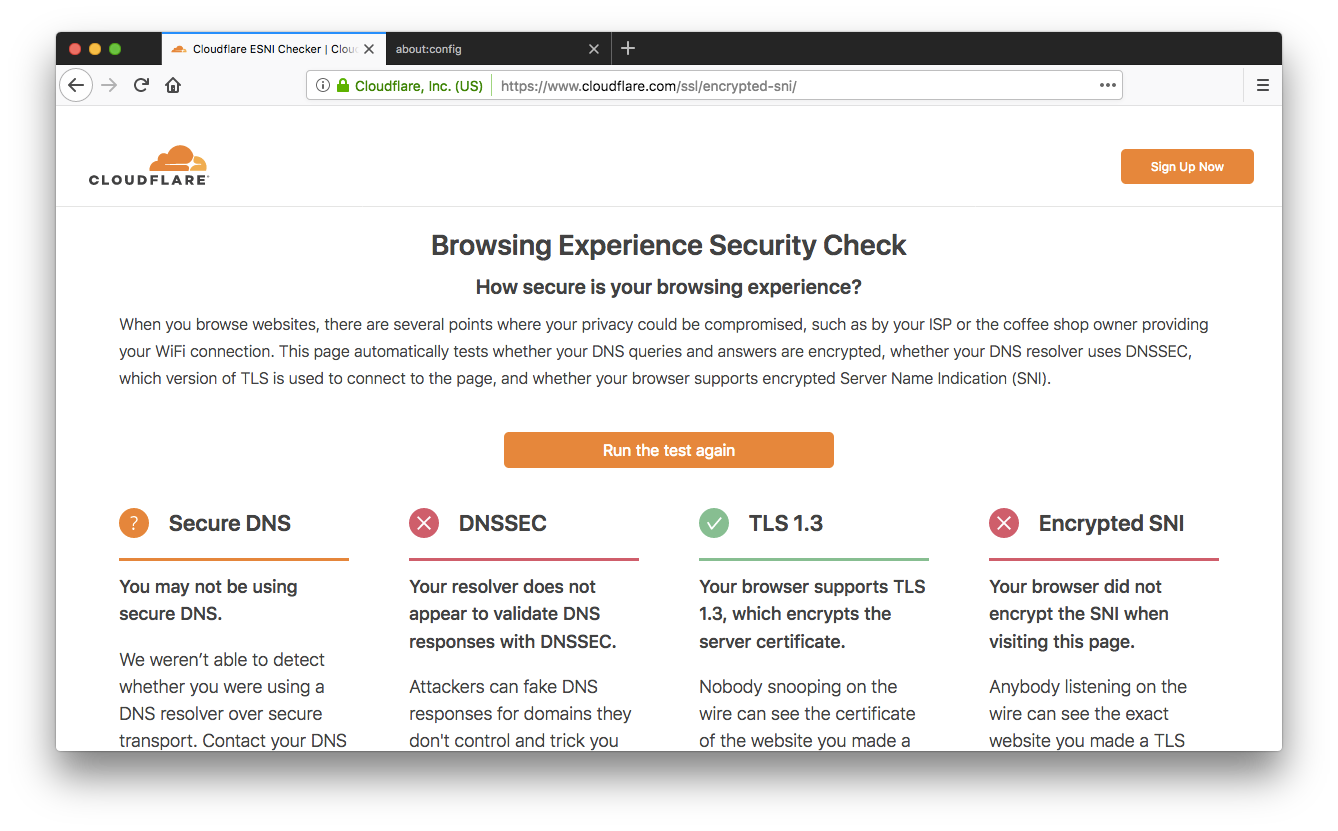
When we announced our support for ESNI we also created a test page you can point your browser to https://encryptedsni.com which checks whether your browser / DNS configuration is providing a more secure browsing experience by using secure DNS transport, DNSSEC validation, TLS 1.3 & ESNI itself when it connects to our test page. Before you make any changes to your Firefox configuration, you might well see a result something like this:
So, room for improvement! Next, head to the about:config page and look for the network.security.esni.enabled Continue reading
AIOps the next big thing for Enterprise IT?
 Out of everything I think will be big in 2019, AIOps is near the top of the list. My current prediction is Artificial Intelligence (AI) making big moves in the enterprise IT Infrastructure and Operations market. AI-based technology is a hot topic in the media these days, everyone is exploring its benefits in a wide range of markets. From self-driving cars and industrial automation to advertising and fraud prevention. It’s no surprise that 2018 was predicted to be a dominating year for AI in IT. While I believe 2018 was a key year for AI getting it’s foot in the door of IT Ops, the reality is lagging behind the hype. In IT we hear a lot about machine learning, and big data, but with the reality of how this data is organized in most enterprises, the onus is still on us to get that data laid out in an organized structure to extract the potential that AI promises.
Out of everything I think will be big in 2019, AIOps is near the top of the list. My current prediction is Artificial Intelligence (AI) making big moves in the enterprise IT Infrastructure and Operations market. AI-based technology is a hot topic in the media these days, everyone is exploring its benefits in a wide range of markets. From self-driving cars and industrial automation to advertising and fraud prevention. It’s no surprise that 2018 was predicted to be a dominating year for AI in IT. While I believe 2018 was a key year for AI getting it’s foot in the door of IT Ops, the reality is lagging behind the hype. In IT we hear a lot about machine learning, and big data, but with the reality of how this data is organized in most enterprises, the onus is still on us to get that data laid out in an organized structure to extract the potential that AI promises.
But how does all of this relate to IT Infrastructure and Operations? AIOps is the combination of AI and IT Operations. And while the IT community hears the AI related buzzwords, not many of us know where or how it can Continue reading
Human Connection Frames Success of 2018 Indigenous Connectivity Summit

The Internet is an incredible tool that can help amplify voices that may not otherwise be heard. But when it comes to making sure everyone can have access to this tool, we can’t downplay the power of human connections to overcome connectivity challenges.
One of the things that stood out for me most at the 2018 Indigenous Connectivity Summit (ICS) last week in Inuvik, NT was getting a first-hand view of what happens when Indigenous voices are at the forefront of Internet solutions.
Nearly 140 people joined us in the Arctic Circle for a two-day series of panels and presentations focused on finding solutions to improve connectivity in rural and remote Indigenous communities, with a special focus on northern connectivity challenges. The livestream was viewed over 850 times.
It was inspiring to hear speakers shed light on the ways they innovated to bring Internet to underserved Indigenous communities on their own terms through Community Networks throughout North America and abroad.
I think some of the most important successes, however, came when ICS participants were able to interact during breaks, round-table discussions, on the bus trip to Tuktoyaktuk, at the community feast, and even on the flights to and from the Continue reading
Deep Learning Is Coming Of Age
In the early days of artificial intelligence, Hans Moravec asserted what became known as Moravec’s paradox: “It is comparatively easy to make computers exhibit adult-level performance on intelligence tests or playing checkers, and difficult or impossible to give them the skills of a one-year-old when it comes to perception and mobility.”
This assertion is now unraveling primarily due to the ascent of deep learning. …
Deep Learning Is Coming Of Age was written by Timothy Prickett Morgan at .
Ciena Inflates Software Control to Reduce Network Complexity
 The company is expanding the reach of its SOAS software to boost IP capabilities and integrating Layer 3 expertise from its Packet Design acquisition.
The company is expanding the reach of its SOAS software to boost IP capabilities and integrating Layer 3 expertise from its Packet Design acquisition.