TeliaSonera & Ericsson to Deploy 5G by 2018
 TeliaSonera was the first to deploy 4G.
TeliaSonera was the first to deploy 4G.
 TeliaSonera was the first to deploy 4G.
TeliaSonera was the first to deploy 4G.
On Wednesday, we announced that GV (formerly Google Ventures) has invested in Plexxi. GV’s investment will help us continue to scale our networking product offerings, meet the needs of the emerging cloud builder community and drive adoption of software-defined architecture in data centers. CEO Rich Napolitano’s recent blog post calls attention to the need for transformation of IT being led by Cloud Builders and Cloud Architects. This investment will help us stay at the forefront of this transformation.
This investment follows Plexxi being named to the Dell Founders 50 list and the release of our newest software suite and Switch 3 hardware program in late 2015. We are committed to constant innovation and proud that GV shares our vision to provide a network that meets today’s dynamic business requirements.
Below please find a few of our top picks for our favorite news articles of the week. For a full list of coverage of the investment, visit here.
ZDNet: Google’s venture capital arm GV invests in networking startup Plexxi
By Natalie Gagliordi
Networking startup Plexxi says it has received a funding investment from GV, Google’s venture capital arm formerly known as Google Ventures. Plexxi did not disclose the specific size of Continue reading
Frustrated with a dilapidated installation of Freeradius 1.x in our lab, and conscious that it is unsupported any more, I decided to install a new Freeradius server.
Ubuntu 14.04.3 LTS is the platform I am installing it on, and this is a relatively fresh installation of Ubuntu server. It needs to serve access-requests from a Redback and a Juniper router in our lab for both PPP and DHCP clients.
Install freeradius using ‘apt-get install freeradius’. This pulls down Freeradius 2.1 as can be seen below:
Setting up freeradius (2.1.12+dfsg-1.2ubuntu8.1)
Edit the /etc/freeradius/clients.conf file to permit all hosts on the lab network (192.168.3.0/24) to be ‘clients’ of my new Freeradius server – as long as they use a shared secret when authenticating. To do this, include the following section:
client 192.168.3.0/24 {
secret = testing123
shortname = labnet-3
}
Copy /etc/freeradius/users to /etc/freeradius/users.originalfile so that we have a backup in case everything goes wrong.
Edit the /etc/freeradius/users file and create a new user:
andrew Cleartext-Password := "password"
Reply-Message = "Hello %{User-Name}"
Save the users file.
Test this locally Continue reading
Hey, it's HighScalability time:
The proponents of microsegmentation solutions would love you to believe that it takes no more than somewhat-stateful packet filters sitting in front of the VMs to get rid of traditional subnets. As I explained in my IPv6 Microsegmentation talk (links below), you need more if you want to have machines from multiple security domains sitting in the same subnet – from RA guard to DHCPv6 and ND inspection.
Read more ...Companies cite security and ROI concerns as barriers to IOT deployment, study shows.
In this video, Tony Fortunato covers packet analysis and key protocol considerations.
Please join us in congratulating the following iPexpert students who have passed their CCIE lab!
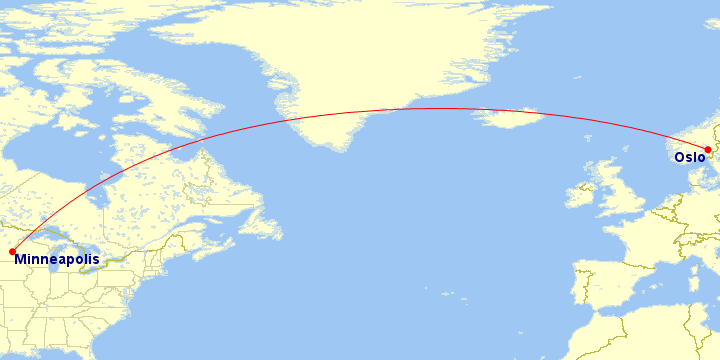
Four thousand miles (6,400 kilometers) separate CloudFlare’s latest two data centers: Oslo (#75) and Minneapolis (#76).
In Oslo, we have now built our third data center in Scandinavia. This joins our existing facilities in Stockholm and Copenhagen. With a data center in Norway, we recognize an important country that stands above others with a staggering 95.05% of the population having Internet connectivity. This Internet penetration rate is the fourth best in the world. For reference, the Internet penetration rate in the US is 84%, the UK is 90% and Egypt, where we deployed our last data center it is only 50%
At 59.9500° N, Oslo is also the “northernmost” CloudFlare data center on our network map.
Oslo, according to the Norwegian Sagas is over 1,000 years old. CloudFlare has built itself into a facility just a handful of years old and while we respect all the wonderful history and tradition associated with Norway, we hope the locals appreciate our 21st century choice.
Norway has a very important position within the history of the Internet (well the ARPANET actually). In June 1973, the Royal Radar Establishment in Norway became one of the first international connections to Continue reading