How To Access Devices with Unsupported SSL Ciphers
With the HeartBleed bug effectively killing off SSLv3 and vulnerabilities in cipher block chaining ruling out another whole swathe of SSL ciphers, network engineers may have found themselves trying to connect to a device and either getting no response (Safari), or getting a response like this (Chrome):
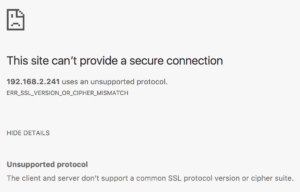
Or this (Firefox):

Once upon a time, it was possible to go into settings and enable the old, insecure ciphers again, but in more recent updates, those ciphers no longer exist within the code and are thus inaccessible. So what to do? My answer was to try a proxy.
Charles Proxy
The first proxy I looked at seemed promising. Although not free, Charles Proxy offers a 30 day free trial, and that seemed like a good thing to try. It’s limited additionally by only running for 30 minutes at a time before it has to be reloaded, but for my testing purposes that was not a problem.
During installation I declined to give Charles Proxy permission to configure the system proxy settings. Instead, I manually updated just my Firefox browser to use the proxy which was now listening on port 127.0.0.1:8888. Since I was making an SSL connection, I also Continue reading
The Super Secret Cloudflare Master Plan, or why we acquired Neumob

We announced today that Cloudflare has acquired Neumob. Neumob’s team built exceptional technology to speed up mobile apps, reduce errors on challenging mobile networks, and increase conversions. Cloudflare will integrate the Neumob technology with our global network to give Neumob truly global reach.
It’s tempting to think of the Neumob acquisition as a point product added to the Cloudflare portfolio. But it actually represents a key part of a long term “Super Secret Cloudflare Master Plan”.
 CC BY 2.0 image by Neil Rickards
CC BY 2.0 image by Neil Rickards
Over the last few years Cloudflare has been building a large network of data centers across the world to help fulfill our mission of helping to build a better Internet. These data centers all run an identical software stack that implements Cloudflare’s cache, DNS, DDoS, WAF, load balancing, rate limiting, etc.
We’re now at 118 data centers in 58 countries and are continuing to expand with a goal of being as close to end users as possible worldwide.
The data centers are tied together by secure connections which are optimized using our Argo smart routing capability. Our Quicksilver technology enables us to update and modify the settings and software running across this vast network in seconds.
Deploy360 at IETF 100, Day 3: SIDR, TLS & Crypto
This week is IETF 100 in Singapore, and we’re bringing you daily blog posts highlighting some of the topics that Deploy360 is interested in. After the focus on IPv6 & IoT during the first couple of days, we’re switching tack today with a focus on routing and crypto matters.
We’re having to wait until after lunch, but then there’s a choice of UTA, SIDROPS or ROLL at 13.30 SGT/UTC+8.
UTA will be focusing on resolving the final IESG comments on the use of TLS for email submission and access which outlines current recommendations for using TLS to provide confidentiality of email traffic between a mail user agent and a mail access server. Next up for discussion are the open issues on a draft related to Strict Transport Security (STS) for mail (SMTP) transfer agents and mail user agents, before consideration of a draft on an option to require TLS for SMTP.
NOTE: If you are unable to attend IETF 100 in person, there are multiple ways to participate remotely.
Over in SIDROPS, there will be a review of the status of BGP Origin Validation deployment in RENATA: the Columbia National Research and Education Network. This represents the first wide-scale deployment Continue reading
Nifty and Nerdy: 10 Holiday Gifts for IT Pros
Stuck on what to get your favorite tech-loving geek? Here are some ideas.
Your online freedoms are under threat – 2017 Freedom on the Net Report
As more people get online everyday, Internet Freedom is facing a global decline for the 7th year in a row.
Today, Freedom House released their 2017 Freedom on the Net report, one of the most comprehensive assessments of countries’ performance regarding online freedoms. The Internet Society is one of the supporters of this report. We think it brings solid and needed evidence-based data in an area that fundamentally impacts user trust.
Looking across 65 countries, the report highlights several worrying trends, including:
- manipulation of social media in democratic processes
- restrictions of virtual private networks (VPNs)
- censoring of mobile connectivity
- attacks against netizens and online journalists
Elections prove to be particular tension points for online freedoms (see also Freedom House’s new Internet Freedom Election Monitor). Beyond the reported trend towards more sophisticated government attempts to control online discussions, the other side of the coin is an increase in restrictions to Internet access, whether through shutting down networks entirely, or blocking specific communication platforms and services.
These Internet shutdowns are at the risk of becoming the new normal. In addition to their impact on freedom of expression and peaceful assembly, shutdowns generate severe economic costs, affecting entire economies [1] and Continue reading
Another Reason to Run Linux on Your Data Center Switches
Arista’s OpenFlow implementation doesn’t support TLS encryption. Usually that’s not a big deal, as there aren’t that many customers using OpenFlow anyway, and those that do hopefully do it over a well-protected management network.
However, lack of OpenFlow TLS encryption might become an RFP showstopper… not because the customer would really need it but because the customer is in CYA mode (we don’t know what this feature is or why we’d use it, but it might be handy in a decade, so we must have it now) or because someone wants to eliminate certain vendors based on some obscure missing feature.
Read more ...Cloud Managed Wireless Solution : Cisco Meraki MR52
What is the purpose to deploy and how much time it takes to configure Cisco Meraki MR52 ?
Well if you have the requirement to have the wireless network with various SSIDs you should go with the site surveys and on the basis of it you should go with the suitable model of the wireless WLCs. If I talk about the Cisco Meraki cloud managed MR52, It is simple to deploy and self configured via cloud. So you need not to require any resource for the configuration of the Meraki MR52 at the remote sites.
What is the throughput of the Cisco Meraki MR52 ?
Well Cisco Meraki MR52 is a high performance box and will provides Continue reading
Cloud Managed Wireless Systems : Cisco Meraki MR52
What is the purpose to deploy and how much time it takes to configure Cisco Meraki MR52 ?
Well if you have the requirement to have the wireless network with various SSIDs you should go with the site surveys and on the basis of it you should go with the suitable model of the wireless WLCs. If I talk about the Cisco Meraki cloud managed MR52, It is simple to deploy and self configured via cloud. So you need not to require any resource for the configuration of the Meraki MR52 at the remote sites.
 |
| Fig 1.1- Cisco Meraki MR25 Wireless Systems |
What is the throughput of the Cisco Meraki MR52 ?
Well Cisco Meraki Continue reading
Ex-Googlers Launch LightStep, Extending APM Beyond Applications
 The company's first product monitors whatever matters most to an enterprise.
The company's first product monitors whatever matters most to an enterprise.
Juniper Builds Turn-Key Telco Cloud with Contrail, Red Hat OpenStack
 It migrated Contrail Cloud from Ubuntu OpenStack.
It migrated Contrail Cloud from Ubuntu OpenStack.