Cloudflare’s approach to handling BMC vulnerabilities


In recent years, management interfaces on servers like a Baseboard Management Controller (BMC) have been the target of cyber attacks including ransomware, implants, and disruptive operations. Common BMC vulnerabilities like Pantsdown and USBAnywhere, combined with infrequent firmware updates, have left servers vulnerable.
We were recently informed from a trusted vendor of new, critical vulnerabilities in popular BMC software that we use in our fleet. Below is a summary of what was discovered, how we mitigated the impact, and how we look to prevent these types of vulnerabilities from having an impact on Cloudflare and our customers.
Background
A baseboard management controller is a small, specialized processor used for remote monitoring and management of a host system. This processor has multiple connections to the host system, giving it the ability to monitor hardware, update BIOS firmware, power cycle the host, and many more things.
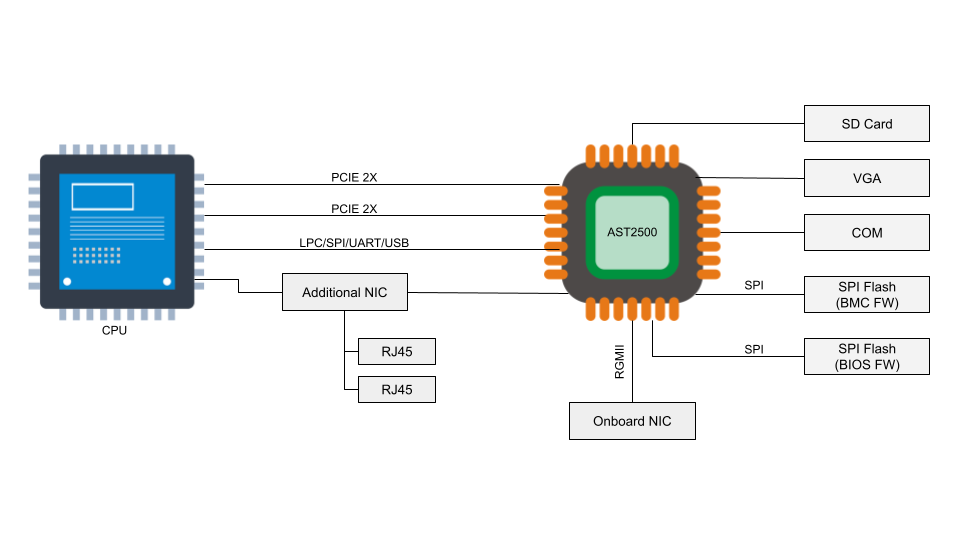
Access to the BMC can be local or, in some cases, remote. With remote vectors open, there is potential for malware to be installed on the BMC from the local host via PCI Express or the Low Pin Count (LPC) interface. With compromised software on the BMC, malware or spyware could maintain persistence on the server.
How we treat content as a product

At Cloudflare, we talk a lot about how to help build a better Internet. On the Product Content Experience (PCX) team, we treat content like a product that represents and fulfills this mission. Our vision is to create world-class content that anticipates user needs and helps build accessible Cloudflare products. We believe we can impact the Cloudflare product experience and make it as wonderful as possible by intentionally designing, packaging, and testing the content.
What is “content like a product”?
I like taking on projects. A singular goal is met, and I clearly know I’m successful because the meaning of “done” is normally very clear. For example, I volunteer some of my time editing academic papers about technology. My role as an editor is temporary and there is a defined beginning and end to the work. I send my feedback and my task is largely complete.
“Content like a product” is when you shift your mindset from completing projects to maintaining a product, taking into consideration the user and their feedback. Product content at Cloudflare is an iterative, living, breathing thing. Inspired by the success of teams that adopt an agile mindset, along with some strategic functions you might find Continue reading
Kubernetes Unpacked 001: Prerequisites For Kubernetes Success
Welcome to the inaugural episode of Kubernetes Unpacked, a new podcast in the Packet Pushers Community Channel. The goal of this podcast is to help IT professionals understand Kubernetes: how it works; how and why it's used; how to deploy, operate, and manage the platform on premises and in the cloud; Kubernetes networking and security concepts; and more.
The post Kubernetes Unpacked 001: Prerequisites For Kubernetes Success appeared first on Packet Pushers.
Kubernetes Unpacked 001: Prerequisites For Kubernetes Success
Welcome to the inaugural episode of Kubernetes Unpacked, a new podcast in the Packet Pushers Community Channel. The goal of this podcast is to help IT professionals understand Kubernetes: how it works; how and why it's used; how to deploy, operate, and manage the platform on premises and in the cloud; Kubernetes networking and security concepts; and more.Worth Reading: Resolverless DNS
Every network engineer should be familiar with the DNS basics – after all, all network failures are caused by DNS… unless it’s BGP.
The May 2022 ISP Column by Geoff Huston is an excellent place to brush up on your DNS basics and learn about new ideas, including a clever one to push DNS entries that will be needed in the future to a web client through a DNS-over-HTTPS session.
Worth Reading: Resolverless DNS
Every network engineer should be familiar with the DNS basics – after all, all network failures are caused by DNS… unless it’s BGP.
The May 2022 ISP Column by Geoff Huston is an excellent place to brush up on your DNS basics and learn about new ideas, including a clever one to push DNS entries that will be needed in the future to a web client through a DNS-over-HTTPS session.
Datacenter Becomes Nvidia’s Largest Business
Something that we have been waiting for a decade and a half to see has just happened: The datacenter is now the biggest business at Nvidia. …
Datacenter Becomes Nvidia’s Largest Business was written by Timothy Prickett Morgan at The Next Platform.
Why Core or Backbone is used in Networking?
Why Core or Backbone is used in Networking?. Before we start explaining this question, let’s note that these two terms are used interchangeably. Usually, Service Providers use Backbone, and Enterprise Networks use Core terminology but they are the same thing.
Why Network Core is Necessary?
The Key Characteristics of the Core, the Backbone part of the networks are:
- High-Speed Connectivity. Today it is 100s of Gigabit networks and is usually used as a bundle to increase the capacity.
- Bringing Internet Gateway, Access, Aggregation, and Datacenter networks together. It connects many different parts of the network, and glues together.
- Redundancy and High Availability are so important. Redundant physical circuits and devices are very common.
- Failure impact is so high in this module, compared to other modules
- Full Mesh or Partial Mesh deployment is seen mostly as these type of topologies provides the most amount of redundancy and the direct path between the different locations.
- Commonly known in the Operator community as Backbone or ‘P Layer
Redundancy in this module is very important.
Most of the Core Network deployments in ISP networks are based on Full Mesh or Partial Mesh.
The reason for having full mesh physical connectivity in the Core network Continue reading
Multicast BIER – Bit Indexed Explicit Replication
Multicast BIER – RFC8279
Bit Index Explicit Replication – BIER is an architecture that provides optimal multicast forwarding through a “BIER domain” without requiring intermediate routers to maintain any multicast-related per-flow state. BIER also does not require any explicit tree-building protocol for its operation.
So, it removes the need for PIM, MLDP, P2MP LSPs RSVP, etc.
A multicast data packet enters a BIER domain at a “Bit-Forwarding Ingress Router” (BFIR), and leaves the BIER domain at one or more “Bit-Forwarding Egress Routers” (BFERs).
The BFIR router adds a BIER header to the packet.
The BIER header contains a bit-string in which each bit represents exactly one BFER to forward the packet to.
The set of BFERs to which the multicast packet needs to be forwarded is expressed by setting the bits that correspond to those routers in the BIER header.
Multicast BIER Advantages
The obvious advantage of BIER is that there is no per-flow multicast state in the core of the network and there is no tree building protocol that sets up trees on-demand based on users joining a multicast flow.
In that sense, BIER is potentially applicable to many services where Multicast is used.
Many Service Providers currently investigating Continue reading
Navigating NSX Module in PowerCLI 12.6
With the release of PowerCLI 12.6, a new module VMware.Sdk.Nsx.Policy was added to provide PowerShell binding for NSX Policy Manager APIs. This new module is auto generated from the NSX Policy API spec exposing all the features related to policy objects in NSX. The module also exposes cmdlets to Create/Edit/Delete NSX objects. This blog explains the use of PowerCLI NSX module, goes through all the different ways new cmdlets can be found and shows how to view documentation on the cmdlets with examples.
Navigating the new cmdlets
Along with the cmdlets to connect, disconnect and modify the NSX objects, there are a few helper cmdlets that make looking up new relevant cmdlets very easy.
The first one is Get-NsxOperation. This is a new feature in VMware.Sdk.Nsx.Policy and is ideal with you need to find the PowerCLI command that corresponds to an API operation and vice versa. You can also narrow down the search result using Where-Object and Select-Object filters.
Example:
Get-NsxOperation -Method GET -Path '/infra/segments'
Since the cmdlets by default returns all paths that start with /infra/segments you can also limit the search to exact match with client-side filter:
Get-NsxOperation -Method get Continue reading