Tech Bytes: Doing Better Than ‘Good’ Or ‘Bad’ For UX Metrics (Sponsored)
On today's Tech Bytes podcast, sponsored by AppNeta, we talk about getting real-time monitoring in place so that you can clearly define your performance benchmarks, accurately measure them from the end-user perspective, and have a strategy to make sure those benchmarks are met. Our guests are John Tewfik, Director of Global Alliances; and Seth Differ, Senior Manager, Solutions Consulting.Tech Bytes: Doing Better Than ‘Good’ Or ‘Bad’ For UX Metrics (Sponsored)
On today's Tech Bytes podcast, sponsored by AppNeta, we talk about getting real-time monitoring in place so that you can clearly define your performance benchmarks, accurately measure them from the end-user perspective, and have a strategy to make sure those benchmarks are met. Our guests are John Tewfik, Director of Global Alliances; and Seth Differ, Senior Manager, Solutions Consulting.
The post Tech Bytes: Doing Better Than ‘Good’ Or ‘Bad’ For UX Metrics (Sponsored) appeared first on Packet Pushers.
Focus is a Virtue
The modern world craves our attention—but only in short bursts. To give your attention to any one thing for too long is failing, it seems, because you might miss out on something else of interest. We have entered the long tail of the attention economy, grounded in finding every smaller slices of time in which the user’s attention can be captured and used.
The problem is obvious for anyone with eyes to see. What is the solution? The good news is there are solutions. The bad news is these solutions are swimming upstream against the major commercial interests of our day, so it’s going to Continue reading
Topology
Real-time network and system metrics as a service describes how to use data captured from the network shown above to explore the functionality of sFlow-RT real-time analytics software. This article builds on the previous article to show how knowledge of network topology can be used to enhance analytics, see Topology for documentation.
First, follow the instructions in the previous example and start an instance of sFlow-RT using the captured sFlow.
curl -O https://raw.githubusercontent.com/sflow-rt/fabric-view/master/demo/topology.jsonThen, download the topology file for the example.
curl -X PUT -H "Content-Type: application/json" -d @topology.json \Install the topology using the sFlow-RT REST API.
http://localhost:8008/topology/json
curl http://localhost:8008/topology/jsonRetrieve the topology.
{
"version": 0,
"links": {
"L1": {
"node2": "spine1",
"node1": "leaf1",
"port1": "swp1s0",
"port2": "swp49"
},
"L2": {
"node2": "spine1",
"node1": "leaf1",
"port1": "swp1s1",
"port2": "swp50"
},
"L3": {
"node2": "spine2",
"node1": "leaf1",
"port1": "swp1s2",
"port2": "swp51"
},
"L4": {
"node2": "spine2",
"node1": "leaf1",
"port1": "swp1s3",
"port2": "swp52"
},
"L5": {
"node2": "spine2",
"node1": "leaf2",
"port1": "swp1s0",
"port2": "swp49"
},
"L6": {
"node2": "spine2",
"node1": "leaf2",
"port1": "swp1s1",
"port2": "swp50"
},
"L7": {
"node2": "spine1",
"node1": "leaf2",
"port1": "swp1s2",
"port2": "swp51"
},
"L8": {
"node2": "spine1",
"node1": "leaf2",
"port1": "swp1s3",
"port2": Continue reading
Network Break 317: Citrix Bets The House On SaaS Collaboration; AWS Forks Elasticsearch
Today's Network Break examines Citrix's multi-billion bet on a SaaS collaboration acquisition, a fight over the Elasticsearch project where everyone gets a black eye, Red Hat's sop to everyone angry about CentOS, a pair of dangerous Cisco SD-WAN bugs, and more IT news.Network Break 317: Citrix Bets The House On SaaS Collaboration; AWS Forks Elasticsearch
Today's Network Break examines Citrix's multi-billion bet on a SaaS collaboration acquisition, a fight over the Elasticsearch project where everyone gets a black eye, Red Hat's sop to everyone angry about CentOS, a pair of dangerous Cisco SD-WAN bugs, and more IT news.
The post Network Break 317: Citrix Bets The House On SaaS Collaboration; AWS Forks Elasticsearch appeared first on Packet Pushers.
How We Ran a Successful Remote Internship Program in 2020
And how we are planning to do it again in 2021…


On March 5, I sat in a small conference room with a few key contributors in creating and hiring for the Cloudflare summer intern program. With the possibility of office shutdowns looming, the group discussed what an internship would look like without in-person mentorship. How would the managers cope? How would the interns cope? Would it even be worthwhile? After a few minutes of discussions, we settled on ‘absolutely’. A remote summer internship at Cloudflare would be worthwhile for students, mentors, buddies, and managers alike. After all, Cloudflare is an Internet company and we were ready to trust the Internet with a whole lot more than we had anticipated.
The months leading up to the summer were a blur, all I remember is that we did a lot of planning, interviewing and hiring. And I mean, a lot. On April 2, Matthew Prince announced that Cloudflare would be doubling the size of our 2020 intern class in response to other companies cutting their intern programs all together. Due to these cuts, many talented students lost their opportunities for the summer. We knew we couldn’t hire them all so we Continue reading
Closing in on Equity: Truist EPIC Grant Seeks to Expand Potential in Communities through Broadband Access

The image was shared around the world. Two little girls hunched over their laptops on a concrete sidewalk, accessing the free WiFi at a fast-food restaurant in order to complete their schoolwork. It was a bleak reminder of the stark digital divide in the United States, where millions are excluded from the benefits of affordable, reliable broadband service. In urban, suburban, and rural areas alike, 42 million Americans – 12% of the population – are on the wrong side of this divide, exacerbating inequalities in access to education, employment, and healthcare.
Conquering this digital divide calls for meaningful solutions, vision, and commitment. Truist has stepped up to the plate with an innovative new grant program that puts the power of connection in the hands of the people who stand to benefit from it. For the over 15 million Americans across the Southeast United States who lack adequate Internet access, broadband coverage cannot wait.
In partnership with Truist, the Internet Society is proud to announce the launch of the Truist EPIC Grant. The program is aimed at funding community-backed broadband – solutions that can help alleviate socioeconomic disparities exacerbated by lack of access.
The Truist EPIC Grant offers eligible Continue reading
New Webinar: Network Automation Concepts
There’s one more thing I feel needs to be done before I go for that coffee break: a webinar focusing on network automation concepts (as opposed to replacing Excel with YAML and Ansible or Becoming a Python Coder). Here’s a rough list of concepts I think should be in there:
- Data models and data stores
- Data model transformations
- Single source of truth
- Abstraction layers
- Idempotency
New Webinar: Network Automation Concepts
There’s one more thing I feel needs to be done before I go for that coffee break: a webinar focusing on network automation concepts (as opposed to replacing Excel with YAML and Ansible or Becoming a Python Coder). Here’s a rough list of concepts I think should be in there:
- Data models and data stores
- Data model transformations
- Single source of truth
- Abstraction layers
- Idempotency
Elixir Using Mix To Create A Package
Elixir is a functional programming language with a syntax inspired by Ruby that runs on the Erlang virtual machine. In this post I will cover the process of creating an Elixir package with Mix and publishing it to Hex.pm which is the package repository for Elixir progect....Learning Elixir
Why and how i'm learning Elixir.Demystifying Private Cellular for the Enterprise
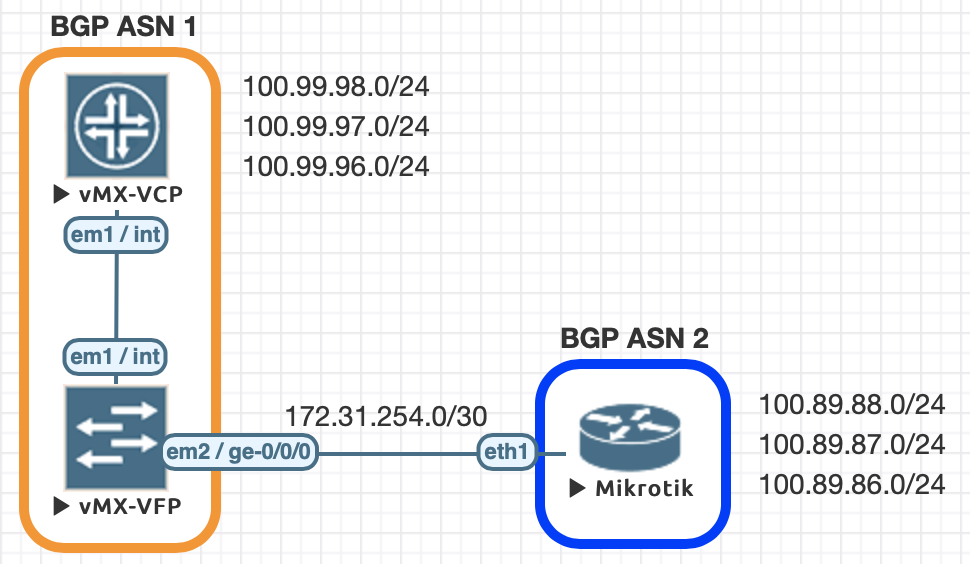
Understanding some of the key technical differences between new private LTE/5G technology and Wi-Fi is an essential step for enterprises to maximize their investments in both.Juniper to MikroTik – BGP commands
About the Juniper to MikroTik series
In the world of network engineering, learning a new syntax for a NOS can be daunting if you need a specific config quickly. Juniper is a popular option for service providers/data centers and is widely deployed across the world.
This is a continuation of the Rosetta stone for network operating systems series. We’ll be working through several protocols over series of posts to help you quickly move between different environments.
While many commands have almost the exact same information, others are as close as possible. Since there isn’t always an exact match, sometimes you may have to run two or three commands to get the information needed.
Using EVE-NG for testing
We conducted all of this testing utilizing EVE-NG and the topology seen below.
| Juniper Command | MikroTik Command |
|---|---|
| show bgp summary | routing bgp peer print brief |
| show bgp neighbor | routing bgp peer print status |
| show route advertising-protocol bgp 172.31.254.2 | routing bgp advertisements print peer=peer_name |
| show route receive-protocol bgp 172.31.254.2 | ip route print where received-from=peer_name |
| show route protocol bgp | ip route print where bgp=yes |
| clear bgp neighbor 172.31.254.2 soft-inbound | Continue reading |
