Deploying security.txt: how Cloudflare’s security team builds on Workers
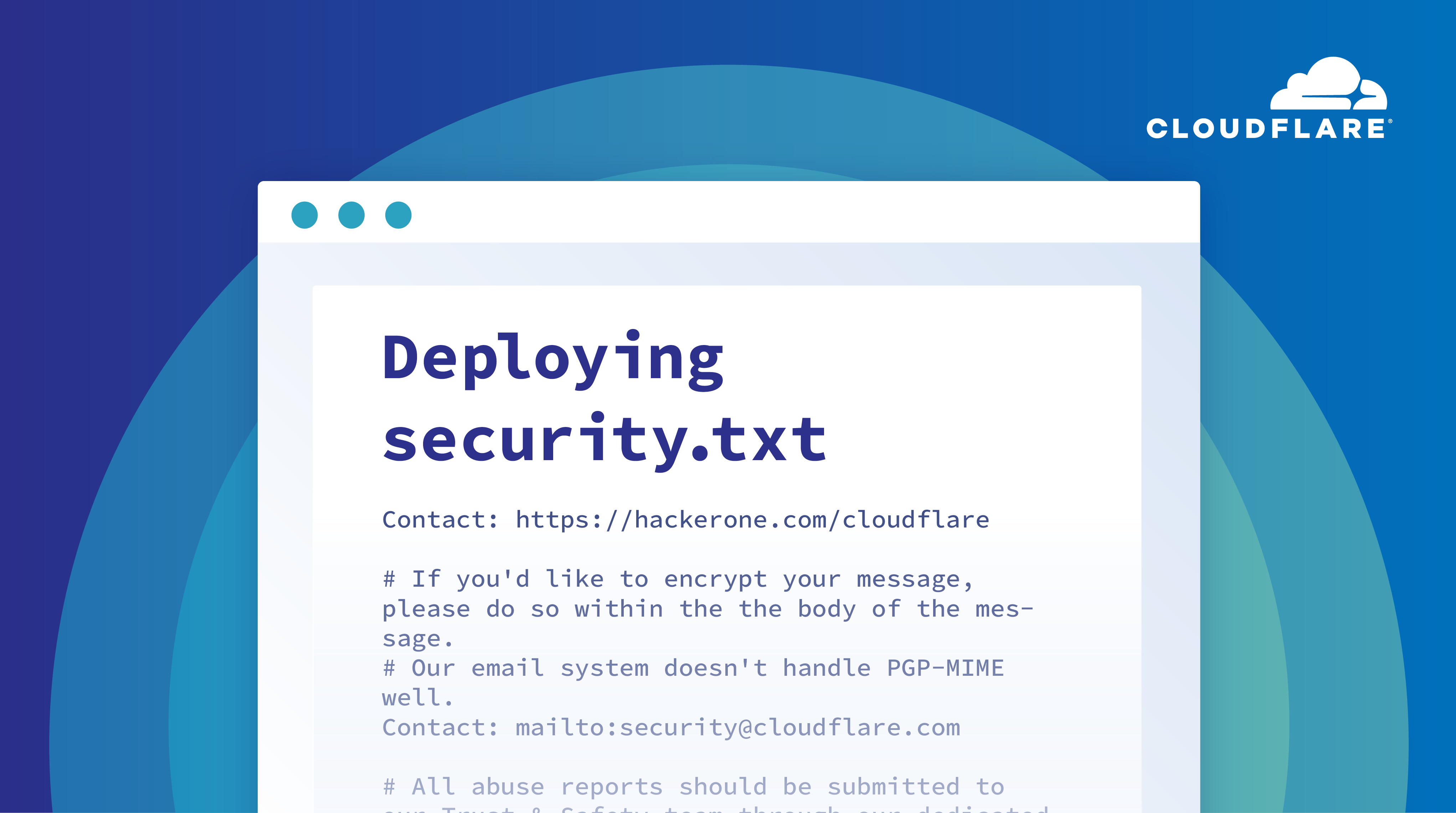
When the security team at Cloudflare takes on new projects, we approach them with the goal of achieving the “builder first mindset” whereby we design, develop, and deploy solutions just as any standard engineering team would. Additionally, we aim to dogfood our products wherever possible. Cloudflare as a security platform offers a lot of functionality that is vitally important to us, including, but not limited to, our WAF, Workers platform, and Cloudflare Access. We get a lot of value out of using Cloudflare to secure Cloudflare. Not only does this allow us to test the security of our products; it provides us an avenue of direct feedback to help improve the roadmaps for engineering projects.
One specific product that we get a lot of use out of is our serverless platform, Cloudflare Workers. With it, we can have incredible flexibility in the types of applications that we are able to build and deploy to our edge. An added bonus here is that our team does not have to manage a single server that our code runs on.
Today, we’re launching support for the security.txt initiative through Workers to help give security researchers a common location to learn about how Continue reading
OMG: What Is Layer-2
Found this “gem” describing the differences between layer-2 and layer-3 on an unnamed $vendor web site.
Layer 2 is mainly concerned with the local delivery of data frames between network devices on the same network or local area network (LAN).
So far so good…
CEX (Code EXpress) 08. Conditionals and wishes.
Hello my friend,
In the previous blogpost we’ve started the discussion about the instructions, which yo need to know in order to create a Python’s code. Namely, we you have learned how to create and use for loops for the Python’s lists and dictionaries. Today you will learn how to create conditionals.
Network automation training – boost your career
Don’t wait to be kicked out of IT business. Join our network automation training to secure your job in future. Come to NetDevOps side.
How does the training differ from this blog post series? Here you get the basics and learn some programming concepts in general, whereas in the training you get comprehensive set of knowledge with the detailed examples how to use Python for the network and IT automation. You need both.
What are we going to do today?
Together with the the loops, the conditionals create a basis of almost each and every script. You would use them, when you need to make a decision about an action you code should execute, when there are multiple actions available and they are dependent in some facts. Therefore, you will learn:
- How to create a conditional instruction using if .. elif .. else .. Continue reading
ipSpace.net Blog Now Runs on Hugo
Years ago I figured out that I’d eventually have to migrate my blog from Blogger to something more independent, and based on my previous experience with Wordpress I wasn’t exactly enthusiastic to go down that path.
In 2015 I’ve seen Scott Lowe going from Wordpress to Jekyll and then to Hugo, and decided it might make sense to recreate ipSpace.net blog with a tool that generates static web pages… but never found the time to do it.
MUST READ: Meaningful Availability
Defining service availability using the famous X nines (and all the hacks like “planned downtime doesn’t count”) is pretty useless in a highly distributed system where the only thing that really matters is the user experience, not ping response times. One should ask what precisely should we be measuring, and how could we make sure we can act on the measurements
More details in a concise analysis of the Meaningful Availability paper by the one-and-only The Morning Paper.
MUST READ: Meaningful Availability
Defining service availability using the famous X nines (and all the hacks like “planned downtime doesn’t count”) is pretty useless in a highly distributed system where the only thing that really matters is the user experience, not ping response times. One should ask what precisely should we be measuring, and how could we make sure we can act on the measurements
More details in a concise analysis of the Meaningful Availability paper by the one-and-only The Morning Paper.
Adding the Fallback Pool to the Load Balancing UI and other significant UI enhancements


The Cloudflare Load Balancer was introduced over three years ago to provide our customers with a powerful, easy to use tool to intelligently route traffic to their origins across the world. During the initial design process, one of the questions we had to answer was ‘where do we send traffic if all pools are down?’ We did not think it made sense just to drop the traffic, so we used the concept of a ‘fallback pool’ to send traffic to a ‘pool of last resort’ in the case that no pools were detected as available. While this may still result in an error, it gave an eyeball request a chance at being served successfully in case the pool was still up.
As a brief reminder, a load balancer helps route traffic across your origin servers to ensure your overall infrastructure stays healthy and available. Load Balancers are made up of pools, which can be thought of as collections of servers in a particular location.
Over the past three years, we’ve made many updates to the dashboard. The new designs now support the fallback pool addition to the dashboard UI. The use of a fallback pool is incredibly helpful in Continue reading
Juniper MX Upgrades Causing Overheating
Juniper changed the way they do temperature management on MX240 and MX480 chassis devices, somewhere between 15.1 and 17.3. The net result is that your chassis might run hotter after you upgrade, which can lead to the system shutting down some optics. Probably not what you want. Luckily there’s a few hidden commands you can use to change this behavior
“Optics will be disabled…”
Post upgrade, you might see higher temperatures reported by show chassis fpc. This system was reporting temperatures in the low 30s, now it reports 50:
1
2
3
4
5
6
7
8
9
lindsayh@MX240> show chassis fpc
Temp CPU Utilization (%) CPU Utilization (%) Memory Utilization (%)
Slot State (C) Total Interrupt 1min 5min 15min DRAM (MB) Heap Buffer
0 Empty
1 Online 50 22 1 22 22 22 2048 38 21
2 Empty
{master}
lindsayh@MX240>
On its own, that’s OK, until you start seeing log messages like this:
1
FPC 1 temperature over 50 degrees C; non-high-temperature tolerant optics will be disabled in 58 seconds if condition persists
Yeah that’s not good, especially when it carries out the threat, and Continue reading
Juniper MX Upgrades Causing Overheating
Juniper changed the way they do temperature management on MX240 and MX480 chassis devices, somewhere between 15.1 and 17.3. The net result is that your chassis might run hotter after you upgrade, which can lead to the system shutting down some optics. Probably not what you want. Luckily there’s a few hidden commands you can use to change this behavior
“Optics will be disabled…”
Post upgrade, you might see higher temperatures reported by show chassis fpc. This system was reporting temperatures in the low 30s, now it reports 50:
1
2
3
4
5
6
7
8
9
lindsayh@MX240> show chassis fpc
Temp CPU Utilization (%) CPU Utilization (%) Memory Utilization (%)
Slot State (C) Total Interrupt 1min 5min 15min DRAM (MB) Heap Buffer
0 Empty
1 Online 50 22 1 22 22 22 2048 38 21
2 Empty
{master}
lindsayh@MX240>
On its own, that’s OK, until you start seeing log messages like this:
1
FPC 1 temperature over 50 degrees C; non-high-temperature tolerant optics will be disabled in 58 seconds if condition persists
Yeah that’s not good, especially when it carries out the threat, and Continue reading
Cloud Foundry Foundation Adopts KubeCF Runtime
The adoption is another block in CFF's path-building toward Kubernetes.
Daily Roundup: AWS Pledges $20M to COVID-19 Testing
AWS pledged $20 million to COVID-19 testing; Microsoft topped cloud rankings; and Cisco donated...
Heavy Networking 507: Build And Run A Multi-Cloud Network Architecture With Aviatrix (Sponsored)
Cloud networking is a challenge, to say the least. And when you've got deployments running in different public clouds, your challenges multiply. On today's Heavy Networking, sponsor Aviatrix joins us to discuss their cloud networking architecture, which provides a consistent operational environment on top of cloud-native constructs. Our guests are Hammad Alam and Shahzad Ali, both Principal Cloud Solutions Architects at Aviatrix.Heavy Networking 507: Build And Run A Multi-Cloud Network Architecture With Aviatrix (Sponsored)
Cloud networking is a challenge, to say the least. And when you've got deployments running in different public clouds, your challenges multiply. On today's Heavy Networking, sponsor Aviatrix joins us to discuss their cloud networking architecture, which provides a consistent operational environment on top of cloud-native constructs. Our guests are Hammad Alam and Shahzad Ali, both Principal Cloud Solutions Architects at Aviatrix.
The post Heavy Networking 507: Build And Run A Multi-Cloud Network Architecture With Aviatrix (Sponsored) appeared first on Packet Pushers.
Fast Friday Thoughts on Where We Are
It’s been a crazy week. I know the curse is “May you live in interesting times,” but I’m more than ready for things to be less interesting for a while. It’s going to take some time to adjust to things. From a networking perspective, I have a few things that have sprung up.
- Video conferencing is now a big thing. Strangely, Cisco couldn’t make video the new phone. But when people are stuck at home now we need to do video again? I get that people have a need to see each other face-to-face. But having worked from home for almost seven years at this point I can tell you video isn’t a necessity. It’s a nice option, but you can get a lot accomplished with video calls and regular emails.
- Along side this is the fact that the push to put more video out there is causing applications to reach their breaking points. Zoom, which is fairing the best out of all of them so far, had some issues on Thursday morning. Tripling the amount of traffic that’s going out and making it very sensitive to delay and jitter is going expose a lot of flaws in the system.
- Continue reading
AWS Pledges $20M to COVID-19 Testing as Cloud Giants, Chipmakers Fight Virus With HPC
While the AWS initiative will initially focus on COVID-19, AWS says it “will also consider other...
Enea Taps Ampere for Arm-based Edge uCPE
The equipment provides an environment on which to run virtual network functions like those for...
Microsoft Skins AWS in Forrester Cloud Ranking
The report lauded those two giants for their extensive services and support, which continues to...
Cisco Donates OpenRoaming as WiFi Standard
OpenRoaming, which has been developed and managed by Cisco for two years, is built on standards and...
Invitation: Virtual Happy Hour The Second – TONIGHT 30 Mar 2020 2100BST/1600EST/1300PST

An open videoconference to be nice to each other, blow the Corona blues away.
The post Invitation: Virtual Happy Hour The Second – TONIGHT 30 Mar 2020 2100BST/1600EST/1300PST appeared first on EtherealMind.
The Serverlist: Workers Secrets, Serverless Supremacy, and more!

Check out our thirteenth edition of The Serverlist below. Get the latest scoop on the serverless space, get your hands dirty with new developer tutorials, engage in conversations with other serverless developers, and find upcoming meetups and conferences to attend.
Sign up below to have The Serverlist sent directly to your mailbox.