OpenBSD in 2019
I’ve used OpenBSD on and off since 2.1. More back then than in the last 10 years or so though, so I thought I’d try it again.
What triggered this was me finding a silly bug in GNU cpio that has existed with a “FIXME” comment since at least 1994. I checked OpenBSD to see if it had a related bug, but as expected no it was just fine.
I don’t quite remember why I stopped using OpenBSD for servers, but I do remember filesystem corruption on “unexpected power disconnections” (even with softdep turned on), which I’ve never really seen on Linux.
That and that fewer things “just worked” than with Linux, which matters more when I installed more random things than I do now. I’ve become a lot more minimalist. Probably due to less spare time. Life is better when you don’t run things like PHP (not that OpenBSD doesn’t support PHP, just an example) or your own email server with various antispam tooling, and other things.
This is all experience from running OpenBSD on a server. On my next laptop I intend to try running OpenBSD on the dektop, and will see if that more ad-hoc environment Continue reading
Tales from the Crypt(o team)

Halloween season is upon us. This week we’re sharing a series of blog posts about work being done at Cloudflare involving cryptography, one of the spookiest technologies around. So bookmark this page and come back every day for tricks, treats, and deep technical content.
A long-term mission
Cryptography is one of the most powerful technological tools we have, and Cloudflare has been at the forefront of using cryptography to help build a better Internet. Of course, we haven’t been alone on this journey. Making meaningful changes to the way the Internet works requires time, effort, experimentation, momentum, and willing partners. Cloudflare has been involved with several multi-year efforts to leverage cryptography to help make the Internet better.
Here are some highlights to expect this week:
- We’re renewing Cloudflare’s commitment to privacy-enhancing technologies by sharing some of the recent work being done on Privacy Pass
- We’re helping forge a path to a quantum-safe Internet by sharing some of the results of the Post-quantum Cryptography experiment
- We’re sharing the rust-based software we use to power time.cloudflare.com
- We’re doing a deep dive into the technical details of Encrypted DNS
- We’re announcing support for a new technique we developed with industry partners Continue reading
Path Prepending in BGP
In this article I'd like to look at one particular aspect of the Internet's inter-domain routing framework, namely the role of the Autonomous System (AS) Path in the operation of BGP, and in particular the use of AS Prepending.TCP MD5
TCP_MD5 (RFC 2385) is something that doesn’t come up often. There’s a couple fo reasons for that, good and bad.
I used it with tlssh, but this should explain why I didn’t enable it by default.
What it is
In short it’s a TCP option that adds an MD5-based signature to every TCP packet. It signs the source and destination IP address, and the ports, and the payload. That way the data is both authenticated and integrity protected.
When an endpoint enables TCP MD5, all unsigned packets (including SYN packets) are silently dropped. For a signed connection it’s not even possible for an eavesdropper to reset the connection, since the RST would need to be signed.
It’s used by the BGP protocol to set a password on the connection, instead of sending the password in the handshake. If the password doesn’t match the TCP connection doesn’t even establish.
But outside of BGP it’s essentially not used, which is a shame. If we could enable it for any TCP service it’d add a preshared key and completely replace the silly port knocking. It probably couldn’t replace user passwords, but it could add a layer and greatly reduce attack surface much Continue reading
Cisco Networking Trends Report: ‘Intent-Based Networking Is Coming’
Winter is coming, and according to Cisco's 2020 Global Networking Trends Report released today, so...
Worth Reading: Hard Work
Seth Godin published an interesting article on the value of hard work (and what hard work really is). Go and read it first, then we’ll translate it into networking terms.
Already back? Good, let’s go.
The first worker is a traditional networking technician (it wouldn’t be fair to call him an engineer) – he’s busy configuring VLANs, ACLs, firewall rules… the whole day.
Read more ...Heavy Networking 481: Enhancing Cloud Security With Network Detection And Response From ExtraHop (Sponsored)
ExtraHop is our sponsor for today's Heavy Networking podcast. We dive into Network Detection and Response (NDR) with CTO and co-founder Jesse Rothstein. We explore how to enhance your security posture with NDR, how to use it in the cloud, ExtraHop's ability to take advantage of native cloud traffic mirroring, how ExtraHop deals with encrypted traffic, and more.
The post Heavy Networking 481: Enhancing Cloud Security With Network Detection And Response From ExtraHop (Sponsored) appeared first on Packet Pushers.
Slow Service Provider Sales Muddle Juniper’s Q3 Earnings
Growth within the company's enterprise, security and software businesses wasn't enough to offset...
Cloud Wars: Amazon, Microsoft Report Declining Cloud Growth
Cloud giants Amazon and Microsoft reported declining quarterly cloud growth this week. Still, both...
Verizon Touts 5G Scenarios Amid ‘Worrisome Signs’
Verizon announced a collaborative effort with SAP to deliver edge computing and real-time analytics...
The End of SD-WAN’s Party In China

As I was listening to Network Break Episode 257 from my friends at Packet Pushers, I heard Greg and Drew talking about a new development in China that could be the end of SD-WAN’s big influence there.
China has a new policy in place, according to Axios, that enforces a stricter cybersecurity stance for companies. Companies doing business in China or with offices in China must now allow Chinese officials to get into their networks to check for security issues as well as verifying the supply chain for network security.
In essence, this is saying that Chinese officials can have access to your networks at any time to check for security threats. But the subtext is a little less clear. Do they get to control the CPE as well? What about security constructs like VPNs? This article seems to indicate that as of January 1, 2020, there will be no intra-company VPNs authorized by any companies in China, whether Chinese or foreign businesses in China.
Tunnel Collapse
I talked with a company doing some SD-WAN rollouts globally in China all the way back in 2018. One of the things that was brought up in that interview was that Continue reading
So, what exactly is NFA?
The post So, what exactly is NFA? appeared first on Noction.
Nominations Now Open for 2020 Internet Society Board of Trustees Elections

The Internet Society Nominations Committee is now inviting nominations for candidates to serve on the Board of Trustees.
The Board provides strategic direction, inspiration, and oversight to advance the Internet Society’s mission of preserving the open, globally-connected, trustworthy and secure Internet for everyone.
In 2020 Chapters will elect two (2) Trustees; Organization Members will elect one (1) Trustee; and the IETF will appoint one (1) Trustee. The term of office is 3 years, beginning in August 2020 and ending mid-year 2023.
The Internet Society is a global non-profit organization that champions the open Internet for everyone. With offices in Washington, DC, USA and Geneva, Switzerland, as well as regional bureaus throughout the world, it is dedicated to ensuring the open development, evolution, and use of the Internet for the benefit of people globally. ISOC is also the organizational home of the Internet Engineering Task Force (IETF) and other Internet-related bodies who together play a critical role in ensuring that the Internet develops in a stable and open manner. ISOC has more than 100 Organization Members, over 130 Chapters and Special Interest Groups, and more than 60,000 individual members that play a role in driving the mission and work of the Continue reading
Noction Flow Analyzer is now in Open Beta
The post Noction Flow Analyzer is now in Open Beta appeared first on Noction.
Weekly Wrap: Ex-Cisco Execs Launch Pensando, Target Amazon
SDxCentral Weekly Wrap for Oct. 25, 2019: Pensando wants to democratize the cloud; Amazon continues...
Sprint Rouses IoT Offensive as CEO Skips MWC LA Keynote
Sprint fired up its Curiosity IoT platform with new services and plans to jointly invest in...
Public keys are not enough for SSH security
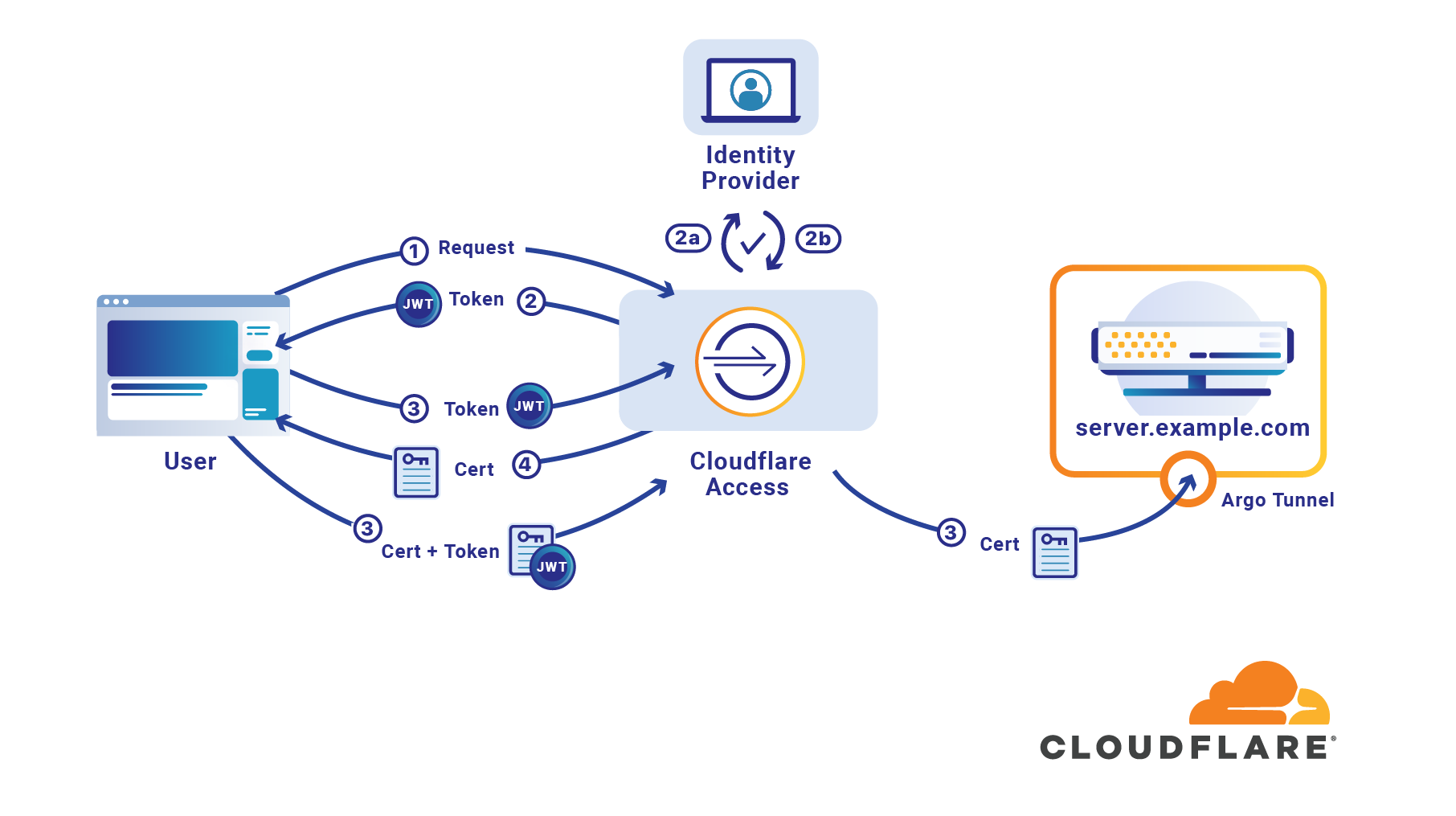
If your organization uses SSH public keys, it’s entirely possible you have already mislaid one. There is a file sitting in a backup or on a former employee’s computer which grants the holder access to your infrastructure. If you share SSH keys between employees it’s likely only a few keys are enough to give an attacker access to your entire system. If you don’t share them, it’s likely your team has generated so many keys you long lost track of at least one.
If an attacker can breach a single one of your client devices it’s likely there is a known_hosts file which lists every target which can be trivially reached with the keys the machine already contains. If someone is able to compromise a team member’s laptop, they could use keys on the device that lack password protection to reach sensitive destinations.
Should that happen, how would you respond and revoke the lost SSH key? Do you have an accounting of the keys which have been generated? Do you rotate SSH keys? How do you manage that across an entire organization so consumed with serving customers that security has to be effortless to be adopted?
Cloudflare Access launched support Continue reading