Welcome to Cloudflare Security Week 2021!


Today kicks off Cloudflare's 2021 Security Week. Like all innovation weeks at Cloudflare, we'll be announcing a dizzying number of new products, opening products that have been in beta to general availability, and talking to customers and through use cases on how to use our network to fulfill our mission of helping build a better Internet.
In Cloudflare's early days, I resisted the label of being a "security company." It seemed overly limiting. Instead, we were setting out to fix the underlying "bugs" of the Internet. The Internet was never built for what it's become. We started Cloudflare to fix that. Being more secure was table stakes, but we also wanted to make the Internet faster, more reliable, and more efficient.
But a lot of what we do is about security. Approximately half our products are security related. And that makes sense because some of the Internet's deepest flaws are that it specifically did not engineer in security from the beginning.
Security: The Internet’s Afterthought
John Graham-Cumming, Cloudflare's CTO, gives a terrific talk about how the Internet we all have come to rely on wasn’t designed to have the security we all need. In Tim Berners-Lee's original proposal for Continue reading
Worth Reading: Splitting the Ping
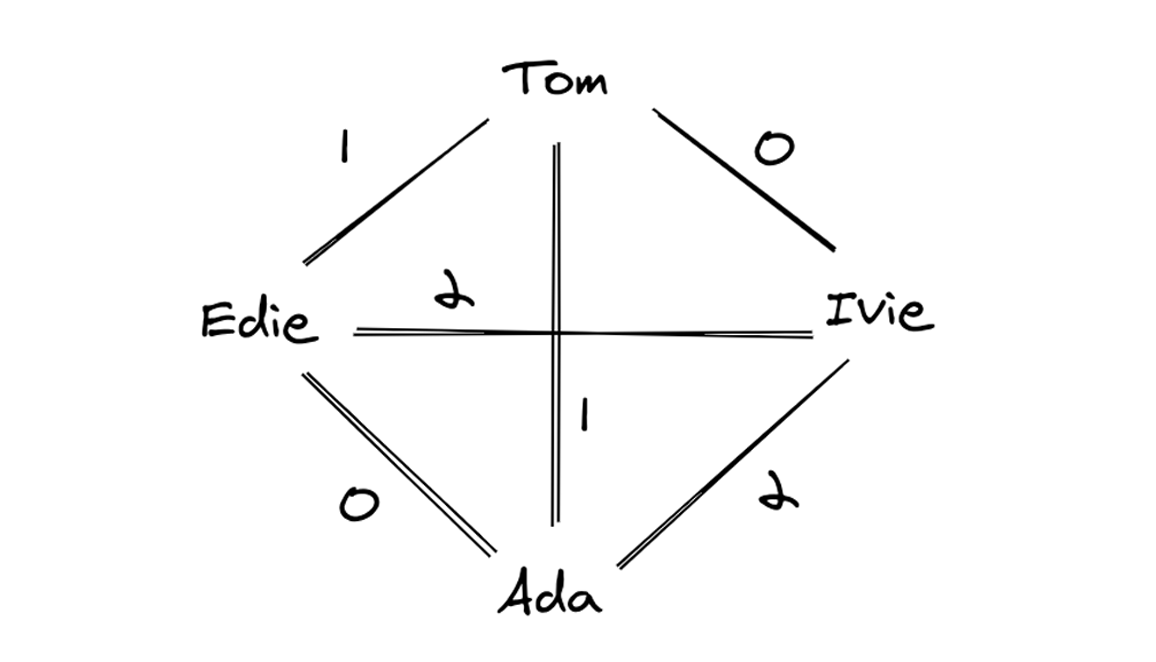
I hope you’re aware that the venerable ping (and most of its variants) measures round-trip-time – how long it takes to get to the destination and back – but is there a way to measure one-way latency or find out asymmetric transit times?
Ben Cox found a way to use ICMP timestamps together with reasonably accurate NTP-derived time to do just that. More details in Splitting the ping (HT: Drew Conry-Murray).
Worth Reading: Splitting the Ping
I hope you’re aware that the venerable ping (and most of its variants) measures round-trip-time – how long it takes to get to the destination and back – but is there a way to measure one-way latency or find out asymmetric transit times?
Ben Cox found a way to use ICMP timestamps together with reasonably accurate NTP-derived time to do just that. More details in Splitting the ping (HT: Drew Conry-Murray).
Basics First and Basics Last

This week I found my tech life colliding with my normal life in an unintended and somewhat enlightening way. I went to a store to pick up something that was out of stock and while I was there making small talk the person behind the counter asked me what I did for a living. I mentioned technology and he said that he was going to college for a degree in MIS, which just happens to be the thing I have my degree in. We chatted about that for a few more minutes before he asked me something I get asked all the time.
“What is the one thing I need to make sure I pay attention to in my courses?”
It’s simple enough, right? You’ve done this before and you have the benefit of hindsight. What is the one thing that is most important to know and not screw up? The possible answers floating through my head were all about programming or analytical methods or even the dreaded infrastructure class I slept through and then made a career out of. But what I said was the most boring and most critical answer one could give.
“You need to know Continue reading
Moving k8s communication to gRPC
Over the past year and a half, Cloudflare has been hard at work moving our back-end services running in our non-edge locations from bare metal solutions and Mesos Marathon to a more unified approach using Kubernetes(K8s). We chose Kubernetes because it allowed us to split up our monolithic application into many different microservices with granular control of communication.
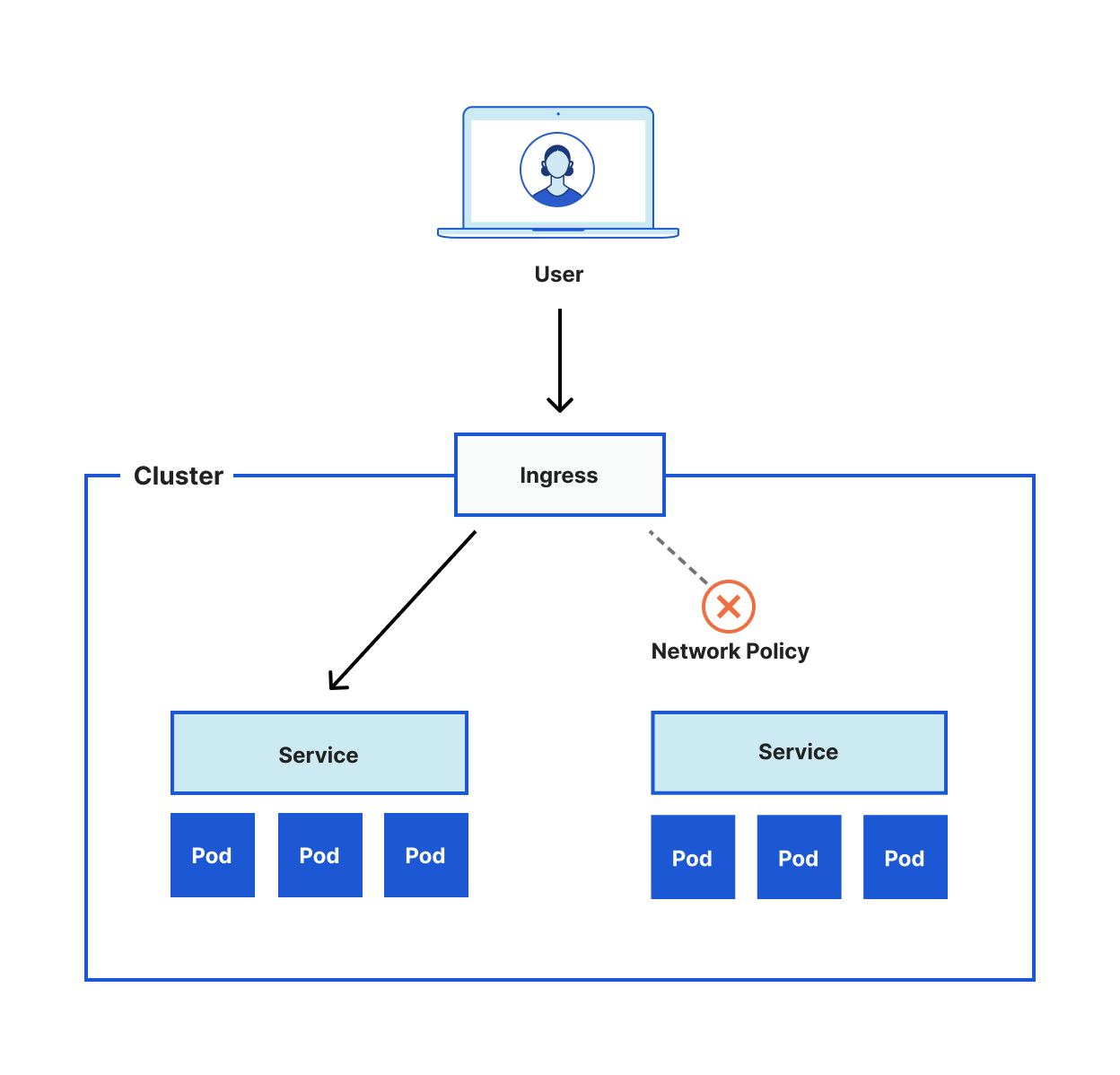
For example, a ReplicaSet in Kubernetes can provide high availability by ensuring that the correct number of pods are always available. A Pod in Kubernetes is similar to a container in Docker. Both are responsible for running the actual application. These pods can then be exposed through a Kubernetes Service to abstract away the number of replicas by providing a single endpoint that load balances to the pods behind it. The services can then be exposed to the Internet via an Ingress. Lastly, a network policy can protect against unwanted communication by ensuring the correct policies are applied to the application. These policies can include L3 or L4 rules.
The diagram below shows a simple example of this setup.
Though Kubernetes does an excellent job at providing the tools for communication and traffic management, it does not help the developer decide the Continue reading
Random Employee Chats at Cloudflare
Due to the COVID-19 pandemic, most Cloudflare offices closed in March 2020, and employees began working from home. Having online meetings presented its own challenges, but preserving the benefits of casual encounters in physical offices was something we struggled with. Those informal interactions, like teams talking next to the coffee machine, help form the social glue that holds companies together.
In an attempt to recreate that experience, David Wragg, an engineer at Cloudflare, introduced “Random Engineer Chats” (We’re calling them “Random Employee Chats” here since this can be applied to any team). The idea is that participants are randomly paired, and the pairs then schedule a 30-minute video call. There’s no fixed agenda for these conversations, but the participants might learn what is going on in other teams, gain new perspectives on their own work by discussing it, or meet new people.
The first iteration of Random Employee Chats used a shared spreadsheet to coordinate the process. People would sign up by adding themselves to the spreadsheet, and once a week, David would randomly form pairs from the list and send out emails with the results. Then, each pair would schedule a call at their convenience. This process was the Continue reading
Automate Leaf and Spine Deployment – Part5
The 5th post in the ‘Automate Leaf and Spine Deployment’ series goes through the deployment of the services that run on top of the fabric. These services are grouped into 3 categories, tenant, interface and routing. Services are configured only on the leaf and border switches, the spines have no need for them as they just route the VXLAN encapsulated packets with no knowledge or care of what is within them.
5 Ways to Save Costs on Microsoft Azure
To ensure costs remain at the desired level, organizations need to manage resource consumption. Azure offers a wide range of tools to help.Heavy Networking 568: Effective Technical Communication
Today's Heavy Networking explores how to communicate complex, nuanced technical topics to non-technical people. We examine how to balance finicky details with broader outcomes, discuss the value of editing and review, share writing tips, and more.
The post Heavy Networking 568: Effective Technical Communication appeared first on Packet Pushers.
Heavy Networking 568: Effective Technical Communication
Today's Heavy Networking explores how to communicate complex, nuanced technical topics to non-technical people. We examine how to balance finicky details with broader outcomes, discuss the value of editing and review, share writing tips, and more.HDMI Dummy Plug Success with VNC!
Spoiler alert, but I am pleased to report back that my experiment with adding an HDMI dummy plug to my Dell laptop has fixed my issues with VNC.
As I theorized in my post “VNC Cannot Currently Show the Desktop” and have since confirmed, when the laptop lid is closed, the laptop disconnects the monitor and Windows runs truly “headless”. Unfortunately VNC uses DirectX Desktop Duplication to grab a copy of what would be on the screen, and if there’s no screen there’s nothing for VNC to grab an duplicate copy of, so VNC is left doing a lot of hard work grabbing screen images using CPU rather than using the far more efficient DirectX shortcuts.

My proposed solution to this was to order an HDMI Dummy Plug, a little HDMI connector which pretends to be an HDMI monitor so that the laptop believes it has an active monitor connected. My other hope was that by having a fake external monitor for VNC to mirror, I might also be able to set it up with a higher resolution than the laptop’s own internal 1920×1080 screen, which might allow me to have a higher resolution remote session using VNC. Continue reading
Cloud Networking With Alkira – A Packet Pushers Livestream Event
Join the Packet Pushers for our inaugural Livestream with cloud networking company Alkira on April 22nd. In this live, online event we’ll take a deep dive into Alkira’s Network Cloud platform, which lets you deploy and manage single and multi-cloud networks. The Packet Pushers will host the event, and interview Alkira executives and customers. We’ll […]
The post Cloud Networking With Alkira – A Packet Pushers Livestream Event appeared first on Packet Pushers.
Cloudflare and WordPress.com partner to Help Build a Better Internet


Cloudflare’s mission is to help build a better Internet. We’ve been at it since 2009 and we’re making progress — with approximately 25 million Internet properties being secured and accelerated by our platform.
When we look at other companies that not only have the scale to impact the Internet, but who are also on a similar mission, it’s hard to ignore Automattic, maintainers of the ubiquitous open-source WordPress software and owner of one the web’s largest WordPress hosting platforms WordPress.com, where up to 409 million people read 20 billion pages every month.1
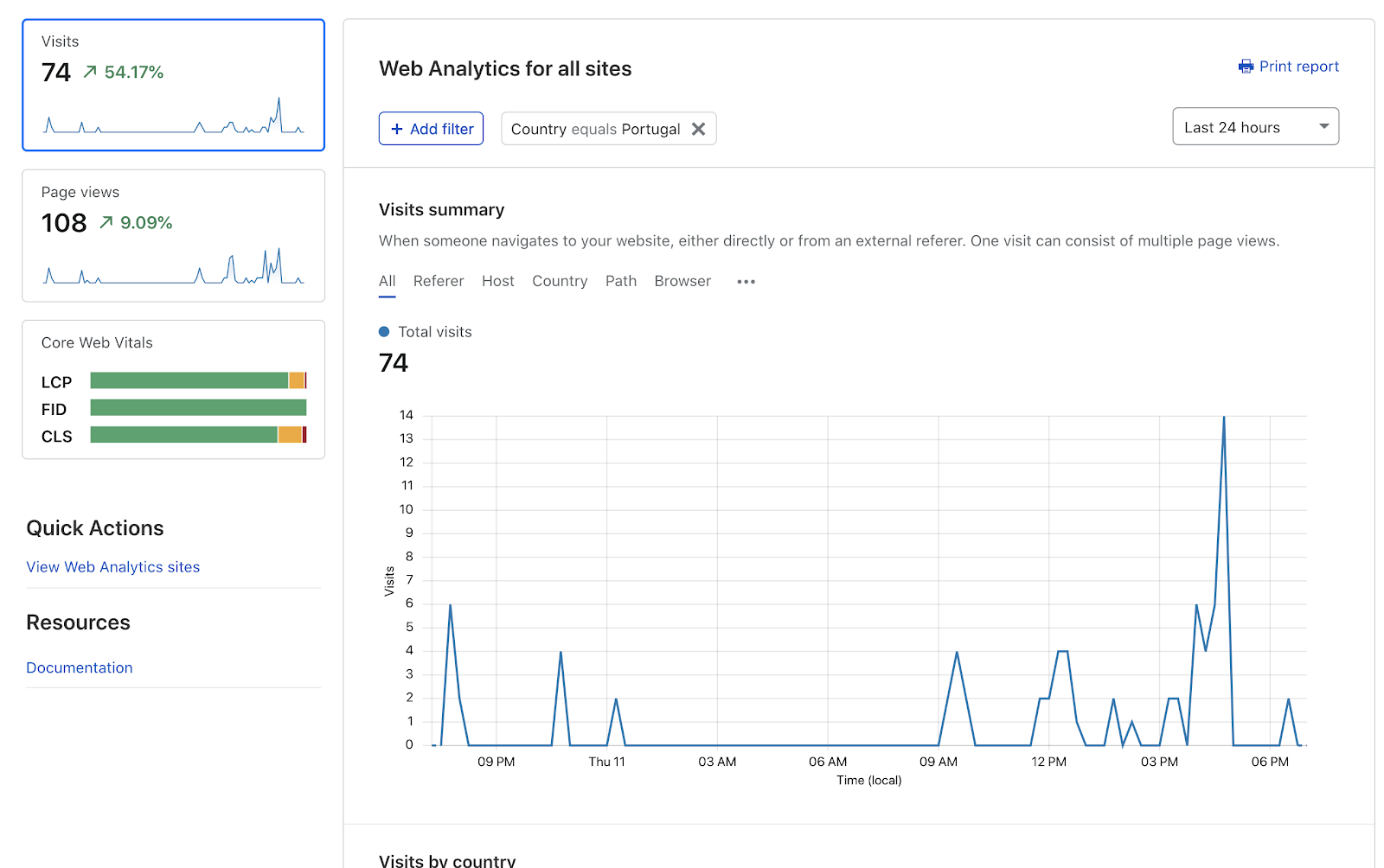
Privacy First Web Analytics
When we started brainstorming ways to combine our impact, one shared value stood out: privacy. We both share a vision for a more private Internet. Today we’re excited to announce a number of initiatives, starting with the integration of Cloudflare’s privacy-first web analytics into WordPress.com. This integration gives WordPress.com publishers choice in how they collect usage data and derive insights about their visitors.
Automatic Platform Optimization for WordPress
This is not the first time Continue reading
Third Time’s the Cache, No More
Caching is a big part of how Cloudflare CDN makes the Internet faster and more reliable. When a visitor to a customer’s website requests an asset, we retrieve it from the customer’s origin server. After that first request, in many cases we cache that asset. Whenever anyone requests it again, we can serve it from one of our data centers close to them, dramatically speeding up load times.
Did you notice the small caveat? We cache after the first request in many cases, not all. One notable exception since 2010 up until now: requests with query strings. When a request came with a query string (think https://example.com/image.jpg?width=500; the ?width=500 is the query string), we needed to see it a whole three times before we would cache it on our default cache level. Weird!
This is a short tale of that strange exception, why we thought we needed it, and how, more than ten years later, we showed ourselves that we didn’t.
Two MISSes too many
To see the exception in action, here’s a command we ran a couple weeks ago. It requests an image hosted on example.com five times and prints each response’s CF-Cache-Status header. Continue reading
Interview: Is Networking Dead?
A few weeks ago I enjoyed a long-overdue chat with David Bombal. David published the first part of it under the click-bait headline Is Networking Dead (he renamed it Is There any Future for Networking Engineers in the meantime).
According to Betteridge’s law of headlines the answer to his original headline is NO (and the second headline violates that law – there you go ?♂️). If you’re still interested in the details, watch the interview.
Interview: Is Networking Dead?
A few weeks ago I enjoyed a long-overdue chat with David Bombal. David published the first part of it under the click-bait headline Is Networking Dead (he renamed it Is There any Future for Networking Engineers in the meantime).
According to Betteridge’s law of headlines the answer to his original headline is NO (and the second headline violates that law – there you go 🤷♂️). If you’re still interested in the details, watch the interview.
CIO Agenda for Right Now: Priorities a Year Into the Pandemic
The COVID-19 pandemic has changed how we do everything. Now it's time to assess the changes and refactor your operations and digital transformation plan.The Importance of Computer Network Security for Your Home
There is a computer in every home. Let that be your personal computer, your laptop or a family computer that everyone uses. The fact is that most of your information is on your computer and you carry it around without fear in the world, knowing that all your data is safe.
The fact is that most of your information, that is stored inside your computer at home is not protected. It is easy to get into and easy to use against you. So, what can you do? At our company, we ensure that we provide you with the right network security to protect your computer against any virus.
So, before you are told about the importance of computer network security for your home, you must first understand how you can make it secure. There are a couple of tips that will help you in the long run.
Make a Difficult Password
Most break-ins to your network happen because the Wi-Fi password that you have is weak. Yes, having a password that you can remember is essential, but having a long and complicated password protects your network system thoroughly, and it is harder to crack through it. By doing so, your Continue reading