Phorpiex-Powered BitRansomware Targets APAC Universities
By: Jason Zhang, Stefano Ortolani – VMware Threat Analysis Unit
BitRansomware (also known as DCryptSoft or Readme) is a — you guessed it — ransomware program that first surfaced in July 2020. Initially targeting English-speaking users1 this threat actor recently expanded its attack to the APAC region, focusing in particular on universities in Japan and Hong Kong.
The BitRansomware malware encrypts victims’ files and then appends the suffix .ReadMe to each filename. Like the Nemty ransomware attack we reported on earlier this year2, the BitRansomware attack was delivered via a massive email campaign carried out again by the Phorpiex botnet3,4. The malspam campaign distributed a swarm of ZIP archive files containing ransomware downloaders in malicious executables.
In this blog post, we detail some of VMware NSX’s telemetry around the magnitude of the BitRansomware campaign, and we then provide a brief overview of the most distinctive aspects of the attack.
The Spam Campaign
The chart below shows the detection timeline of the campaign as it affected some of our customers in the APAC region. As we can see, the campaign started on November 3, and peaked at over 28,000 email instances on November 4 before Continue reading
FRR
FRRouting (FRR) is an IP routing protocol suite for Linux and Unix platforms which includes protocol daemons for BGP, IS-IS, LDP, OSPF, PIM, and RIP.docker run --rm -d --privileged --name frr sflow/frrRun the following command to show the router configuration:
docker exec frr vtysh -c "show running-config"The results will be displayed:
Building configuration...
Current configuration:
!
frr version 7.5_git
frr defaults traditional
hostname ed9e435c6f3d
no ipv6 forwarding
log stdout
!
router bgp 65000
bgp router-id 0.0.0.1
neighbor 192.168.65.2 remote-as 65001
neighbor 192.168.65.2 port 1179
neighbor 192.168.65.2 ebgp-multihop 255
neighbor 192.168.65.2 timers connect 10
!
address-family ipv4 unicast
neighbor 192.168.65.2 route-map ALLOW-ALL in
neighbor 192.168.65.2 route-map ALLOW-ALL out
exit-address-family
!
address-family ipv4 flowspec
neighbor 192.168.65.2 activate
neighbor 192.168.65.2 route-map ALLOW-ALL in
neighbor 192.168.65.2 route-map ALLOW-ALL out
exit-address-family
!
address-family ipv6 unicast
neighbor 192.168.65. Continue reading
Connecting Indigenous Communities: An Urgent Call for Inclusivity, Ownership, and Affordability

In October, we held the 2020 edition of Indigenous Connectivity Summit (ICS). Over the last four years, this summit has become a hallmark event for Indigenous network operators, leaders, community members, and others to come together to discuss the unique opportunities and challenges Indigenous communities face when campaigning for quality and affordable Internet access, and to build relationships with like-minded communities across North America.
In addition to the summit itself, for six weeks prior to the event participants in the ICS Policy and Advocacy training program led the development of a set of policy recommendations. These were then elaborated on, reviewed, and endorsed by summit participants, and they will now help both the Internet Society and the Indigenous communities who created them to advocate for policies that will help the United States and Canada move closer to digital equity.
We know that these recommendations really do make a difference. In 2019, our policy recommendations and organized advocacy efforts affected real change. The Federal Communications Commission in the U.S. was about to launch a spectrum auction and include a Tribal Priority Window so Indigenous communities could apply for the rights to the airwaves over their lands. The Tribal Priority Window Continue reading
Pluribus Rings Out 2020 on a High Note: DCS Awards’ ‘Edge Computing Innovation of the Year’
The annual Data Centre Solutions Awards have just been announced and Pluribus Networks was named the winner of the ‘Edge Computing Innovation of the Year’ Award.Announcing Workplace Records for Cloudflare for Teams
We wanted to close out Privacy & Compliance Week by talking about something universal and certain: taxes. Businesses worldwide pay employment taxes based on where their employees do work. For most businesses and in normal times, where employees do work has been relatively easy to determine: it's where they come into the office. But 2020 has made everything more complicated, even taxes.
As businesses worldwide have shifted to remote work, employees have been working from "home" — wherever that may be. Some employees have taken this opportunity to venture further from where they usually are, sometimes crossing state and national borders.
In a lot of ways, it's gone better than expected. We're proud of helping provide technology solutions like Cloudflare for Teams that allow employees to work from anywhere and ensure they still have a fast, secure connection to their corporate resources. But increasingly we've been hearing from the heads of the finance, legal, and HR departments of our customers with a concern: "If I don't know where my employees are, I have no idea where I need to pay taxes."
Today we're announcing the beta of a new feature for Cloudflare for Teams to help solve this problem: Continue reading
2021 Will Be the Year of Data Center Resiliency: Plan Now
IT leaders should plan now for worst-case disruption scenarios to improve their ability to execute best-case responses.IPv6 Buzz 066: Is IPv6 Baked Enough?
Today's IPv6 Buzz podcast tackles the question of IPv6 maturity, how much change we might expect to the protocol going forward, the standards process, and more. Our guest is Russ White, Infrastructure Architect at Juniper Networks. Russ is an author, speaker, and chairs two IETF working groups.
The post IPv6 Buzz 066: Is IPv6 Baked Enough? appeared first on Packet Pushers.
IPv6 Buzz 066: Is IPv6 Baked Enough?
Today's IPv6 Buzz podcast tackles the question of IPv6 maturity, how much change we might expect to the protocol going forward, the standards process, and more. Our guest is Russ White, Infrastructure Architect at Juniper Networks. Russ is an author, speaker, and chairs two IETF working groups.Cloudflare Certifications
At Cloudflare, we prioritize initiatives that improve the security and privacy of our products and services. The security organization believes trust and transparency are foundational principles that are ingrained in what we build, the policies we set, and the data we protect. Many of our enterprise customers have stringent regulatory compliance obligations and require their cloud service providers like ourselves to provide assurance that we meet and exceed industry security standards. In the last couple of years, we’ve decided to invest in ways to make the evaluation of our security posture easier. We did so not only by obtaining recognized security certifications and reports in an aggressive timeline, but we also built a team that partners with our customers to provide transparency into our security and privacy practices.
Security Certifications & Reports
We understand the importance of providing transparency into our security processes, controls, and how our customers can continuously rely on them to operate effectively. Cloudflare complies with and supports the following standards:
SOC-2 Type II / SOC 3 (Service Organizations Controls) - Cloudflare maintains SOC reports that include the security, confidentiality, and availability trust principles. The SOC-2 report provides assurance that our products and underlying infrastructure are secure Continue reading
Learning Networking Fundamentals at University?
One of my readers sent me this interesting question:
It begs the question in how far graduated students with a degree in computer science or applied IT infrastructure courses (on university or college level or equivalent) are actually aware of networking fundamentals. I work for a vendor independent networking firm and a lot of my new colleagues are college graduates. Positively, they are very well versed in automation, scripting and other programming skills, but I never asked them what actually happens when a packet traverses a network. I wonder what the result would be…
I can tell you what the result would be in my days: blank stares and confusion. I “enjoyed” a half-year course in computer networking that focused exclusively on history of networking and academic view of layering, and whatever I know about networking I learned after finishing my studies.
Learning Networking Fundamentals at University?
One of my readers sent me this interesting question:
It begs the question in how far graduated students with a degree in computer science or applied IT infrastructure courses (on university or college level or equivalent) are actually aware of networking fundamentals. I work for a vendor independent networking firm and a lot of my new colleagues are college graduates. Positively, they are very well versed in automation, scripting and other programming skills, but I never asked them what actually happens when a packet traverses a network. I wonder what the result would be…
I can tell you what the result would be in my days: blank stares and confusion. I “enjoyed” a half-year course in computer networking that focused exclusively on history of networking and academic view of layering, and whatever I know about networking I learned after finishing my studies.
Docker CLI Cheat Sheet
Docker CLI commands cheat sheet.How Social Networking Has Changed in the Past Year Due to COVID-19
From the beginning of this year, people started working from home to reduce the spread of COVID-19. The routines of practically everyone changed one afternoon. More and more people’s work and daily lives have changed to working online and working from home.
How Social Networking Changed Since COVID-19 Began
In the beginning, resources helped social managers and teams navigate their responses to handle COVID-19. After posts were uploaded at the beginning of the year, using different social media platforms, we were able to get more information about the spread of the virus. For people and users of social media platforms like Facebook, Twitter, Instagram, and others, optimal send times were used.
Facebook, Twitter, Instagram, and LinkedIn had a lot more users because of the pandemic. Lots of them made use of these platforms to handle their jobs and to send them to appropriate individuals all around the world.
COVID-19 Changed the Prime Posting Times for Social Media Sites
The data that got pulled for the yearly review showed the best times to upload necessary data. From the middle of April 2020, the most important times to upload different things on social media and to go online first changed. In different Continue reading
Why We’re Helping to Measure the Internet

Here at the Internet Society, we’ve always known that the Internet can be an integral part of our existence. 2020 has shown us that we need stable, reliable, and available Internet for everyone, everywhere.
Much of our work – and the work of the organizations that facilitate the smooth functioning of the Internet – is focused on helping to increase the Internet’s reach, reliability, resilience, availability and security. One of the ways we can track whether these efforts are working is to collect and measure data on various facets of the Internet. This helps to build up a bigger picture of the Internet’s development over time and the resulting data can be used to inform and support policy, investment, and education.
Internet Insights
The Internet Society Insights platform was launched in December 2020 to provide a curated set of insights to help everyone gain deeper, data-driven insight into the Internet. We’re collating data from several trusted organizations – data partners – and will examine Internet trends, generate reports, and tell data-driven stories on how the Internet is evolving.
In this blog, we catch up with some of our data partners and prominent members of the Internet measurement community to find out more about why Continue reading
Freeze Your Credit Reports Before Identity Thieves Open Credit In Your Name
I found out today that I’m a victim of identify theft. Specifically, the bad guys have gotten a hold of my name, SSN, and probably other fun tidbits of my personal information. My best guess is that this is a result of the Equifax breach, not that it matters.
How Did I Notice The Identity Theft?
I am enrolled in a free credit monitoring service that notifies me when things happen on my credit report. (I’m not recommending a particular monitoring service. The one I’m using is tied to a bank where I’m a customer, and it’s good enough.) There were two “hard inquiries” listed within a few days of each other.
There are hard and soft inquiries. As I understand it, a hard inquiry means you’ve applied for credit, and the lending institution is trying to figure out whether or not they’ll extend you the money. If you see a hard inquiry and you’re not applying for credit, that’s a red flag. Soft inquiries are for things like pre-approved credit card offers that you didn’t ask for but receive in the mail anyway.
One of the hard inquiries was from the Small Business Association government agency. The thief Continue reading
New Report Explores COVID-19’s Impact on the Internet in Afghanistan, Nepal, and Sri Lanka
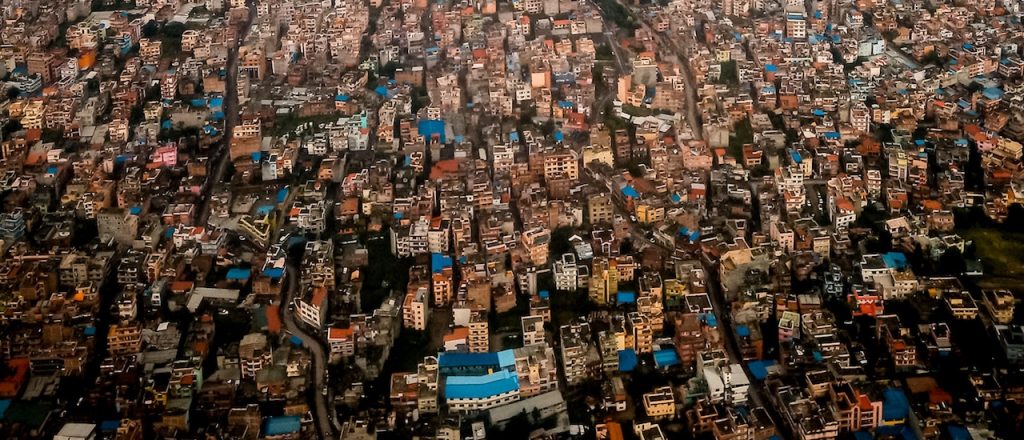
During the COVID-19 pandemic, many have shifted their day-to-day activities to online. To sustain the spike in Internet traffic, fast and affordable Internet service are now more critical than ever.
Yet, Ookla Insights shows that Internet speed in Afghanistan, Nepal, and Sri Lanka has declined since the pandemic. A new Internet Society report, The Impact of the COVID-19 Pandemic on Internet Performance in Afghanistan, Nepal and Sri Lanka, examines the impact of this fall in the performance and quality of Internet services in these countries on online users.
Informed by an online survey, taken by two hundred Internet users – predominantly tech-savvy city dwellers with access to the Internet – the report reveals there is a decline in Internet performance in the three countries. It shows that though the performance decline frustrated online users, more are increasingly spending on high-speed Internet.
The research advocates for governments and Internet Service Providers (ISPs) to take advantage of the situation and accelerate efforts to increase network capacity and reliability to address the performance gaps.
Here are some highlights from The Impact of the COVID-19 Pandemic on Internet Performance in Afghanistan, Nepal and Sri Lanka.
Fall in Internet Performance
Around 50-80% of Continue reading
Day Two Cloud 078: Cloud Economics Are Ridiculous
Corey Quinn stops by the Day Two Cloud podcast to explore the complicated world of understanding and managing cloud costs, CapEx vs OpEx, cloud lock-in, and other tricky issues. Corey is Chief Cloud Economist at Duckbill Group. He also publishes the Last Week In AWS newsletter.
The post Day Two Cloud 078: Cloud Economics Are Ridiculous appeared first on Packet Pushers.
