The dark side of BGP community attributes
The post The dark side of BGP community attributes appeared first on Noction.
Worth Exploring: Pluginized Protocols
Remember my BGP route selection rules are a clear failure of intent-based networking paradigm blog post? I wrote it almost three years ago, so maybe you want to start by rereading it…
Making long story short: every large network is a unique snowflake, and every sufficiently convoluted network architect has unique ideas of how BGP route selection should work, resulting in all sorts of crazy extended BGP communities, dozens if not hundreds of nerd knobs, and 2000+ pages of BGP documentation for a recent network operating system (no, unfortunately I’m not joking).
Worth Exploring: Pluginized Protocols
Remember my BGP route selection rules are a clear failure of intent-based networking paradigm blog post? I wrote it almost three years ago, so maybe you want to start by rereading it…
Making long story short: every large network is a unique snowflake, and every sufficiently convoluted network architect has unique ideas of how BGP route selection should work, resulting in all sorts of crazy extended BGP communities, dozens if not hundreds of nerd knobs, and 2000+ pages of BGP documentation for a recent network operating system (no, unfortunately I’m not joking).
The New Normal Requires a New Enterprise Security Framework
Managing network architecture while moving to SASE requires pragmatic, secure access solutions for existing hybrid infrastructures that are future-compatible.2020….A Year of So Much Change
In some ways it feels like just yesterday I was in Barcelona for CiscoLive. The convention center filled with people and energy… and all of that energy and life spilling out into everything around it…. from La Rambla to the... Read More ›
The post 2020….A Year of So Much Change appeared first on Networking with FISH.
A Thanksgiving 2020 Reading List

While our colleagues in the US are celebrating Thanksgiving this week and taking a long weekend off, there is a lot going on at Cloudflare. The EMEA team is having a full day on CloudflareTV with a series of live shows celebrating #CloudflareCareersDay.
So if you want to relax in an active and learning way this weekend, here are some of the topics we’ve covered on the Cloudflare blog this past week that you may find interesting.
Improving Performance and Search Rankings with Cloudflare for Fun and Profit
Making things fast is one of the things we do at Cloudflare. More responsive websites, apps, APIs, and networks directly translate into improved conversion and user experience. On November 10, Google announced that Google Search will directly take web performance and page experience data into account when ranking results on their search engine results pages (SERPs), beginning in May 2021.
Rustam Lalkaka and Rita Kozlov explain in this blog post how Google Search will prioritize results based on how pages score on Core Web Vitals, a measurement methodology Cloudflare has worked closely with Google to establish, and we have implemented support for in our analytics tools. Read the full blog post.
Getting Continue reading
Fun Times: Another Broken Linux ALG
Dealing with protocols that embed network-layer addresses into application-layer messages (like FTP or SIP) is great fun, more so if the said protocol traverses a NAT device that has to find the IP addresses embedded in application messages while translating the addresses in IP headers. For whatever reason, the content rewriting functionality is called application-level gateway (ALG).
Even when we’re faced with a monstrosity like FTP or SIP that should have been killed with napalm a microsecond after it was created, there’s a proper way of doing things and a fast way of doing things. You could implement a protocol-level proxy that would intercept control-plane sessions… or you could implement a hack that tries to snoop TCP payload without tracking TCP session state.
Not surprisingly, the fast way of doing things usually results in a wonderful attack surface, more so if the attacker is smart enough to construct HTTP requests that look like SIP messages. Enjoy ;)
Fun Times: Another Broken Linux ALG
Dealing with protocols that embed network-layer addresses into application-layer messages (like FTP or SIP) is great fun, more so if the said protocol traverses a NAT device that has to find the IP addresses embedded in application messages while translating the addresses in IP headers. For whatever reason, the content rewriting functionality is called application-level gateway (ALG).
Even when we’re faced with a monstrosity like FTP or SIP that should have been killed with napalm a microsecond after it was created, there’s a proper way of doing things and a fast way of doing things. You could implement a protocol-level proxy that would intercept control-plane sessions… or you could implement a hack that tries to snoop TCP payload without tracking TCP session state.
Not surprisingly, the fast way of doing things usually results in a wonderful attack surface, more so if the attacker is smart enough to construct HTTP requests that look like SIP messages. Enjoy ;)
What’s Your Work From Home DR Plan?

It’s almost December and the signs are pointing to a continuation of the current state of working from home for a lot of people out there. Whether it’s a surge in cases that is causing businesses to close again or a change in the way your company looks at offices and remote work, you’re likely going to ring in the new year at your home keyboard in your pajamas with a cup of something steaming next to your desk.
We have all spent a lot of time and money investing in better conditions for ourselves at home. Perhaps it was a fancy new mesh chair or a more ergonomic keyboard. It could have been a bigger monitor with a resolution increase or a better webcam for the dozen or so Zoom meetings that have replaced the water cooler. There may even be more equipment in store, such as a better home wireless setup or even a corporate SD-WAN solution to help with network latency. However, have you considered what might happen if it all goes wrong and you need to be online?
In and Outage
Outages happen more often than we realize. That’s never been more evident than the situation Continue reading
Networking and Infrastructure News Roundup: November 27 Edition
In the news this week: New managed services for improving workflows in multi-clouds and for administering storage in and across hybrid environments.Securing Modern Applications
Modern applications are changing enterprise security. Apps today are comprised of dozens, or even hundreds, of microservices. They can be spun up and down in real time and may span multiple clouds (on–premises, private cloud, and public cloud). Traditional security stacks just aren’t suited to protecting these applications consistently.
To effectively secure modern apps, we start by identifying unique application assets across clouds—such as users, services, and data. We then continuously evaluate their risk and automatically make authorization decisions to adjust our application security and compliance posture based on asset identity—regardless of where they are or where they have moved.
Security professionals can learn how to use VMware network and security solutions to secure modern applications in the following VMworld sessions:
Security Policies for Modern Applications: An Evolution from Micro-segmentation (ISCS2240)
Enterprises are embracing cloud native transformation and modernizing traditional applications, from monolithic to microservices architectures. As applications transform and span multiple clouds (on–premises, private cloud, and public cloud), it’s essential to Continue reading
Get Off Social Media! Things to Spend Your Time on Instead
Social media can be hard to navigate especially now that there are so many platforms available at the touch of a button. Humans haven’t had enough time to evolve to social media and the vast technological innovations we’ve made. Twenty years ago, humans spent an average of 2-4 hours on their phones and the internet and now that number has grown to 10-14 hours.
This is a massive change over a very short amount of time. This, in conjunction with the effects of the coronavirus pandemic on society, has had a rather large impact on frequent users of the internet. Despite the surplus of internet websites and platforms, people are feeling more lonely and detached than ever.
If you’re struggling with these feelings and other negative feelings as a result of the echo that is social media, here are 5 things you can do instead:
Go Outside!
Depending on the lockdown rules in your state or country, you should consider going outside. It is important that you experience nature, see other human beings, and remind yourself that you are not alone in the world. You can take a walk, go on a run or just sit on your balcony and Continue reading
Heavy Networking 552: How Fortinet Enables Multi-Vendor Security Integration (Sponsored)
On today's Heavy Networking, sponsored by Fortinet, we dive into a variety of topics including a multiplicity of edges that require connectivity and security (WAN edge, LAN edge, cloud edge, remote edge, etc.), the convergence of infrastructure and security, the need for interoperability among security vendors, implementing Zero Trust Access (ZTA), and the current and future roles for machine learning and AI. Our guest is John Maddison, EVP of Products.
The post Heavy Networking 552: How Fortinet Enables Multi-Vendor Security Integration (Sponsored) appeared first on Packet Pushers.
Heavy Networking 552: How Fortinet Enables Multi-Vendor Security Integration (Sponsored)
On today's Heavy Networking, sponsored by Fortinet, we dive into a variety of topics including a multiplicity of edges that require connectivity and security (WAN edge, LAN edge, cloud edge, remote edge, etc.), the convergence of infrastructure and security, the need for interoperability among security vendors, implementing Zero Trust Access (ZTA), and the current and future roles for machine learning and AI. Our guest is John Maddison, EVP of Products.ASICs at the Edge
At Cloudflare we pride ourselves in our global network that spans more than 200 cities in over 100 countries. To handle all the traffic passing through our network, there are multiple technologies at play. So let’s have a look at one of the cornerstones that makes all of this work… ASICs. No, not the running shoes.
What's an ASIC?
ASIC stands for Application Specific Integrated Circuit. The name already says it, it's a chip with a very narrow use case, geared towards a single application. This is in stark contrast to a CPU (Central Processing Unit), or even a GPU (Graphics Processing Unit). A CPU is designed and built for general purpose computation, and does a lot of things reasonably well. A GPU is more geared towards graphics (it's in the name), but in the last 15 years, there's been a drastic shift towards GPGPU (General Purpose GPU), in which technologies such as CUDA or OpenCL allow you to use the highly parallel nature of the GPU to do general purpose computing. A good example of GPU use is video encoding, or more recently, computer vision, used in applications such as self-driving cars.
Unlike CPUs or GPUs, ASICs are built Continue reading
A Byzantine failure in the real world
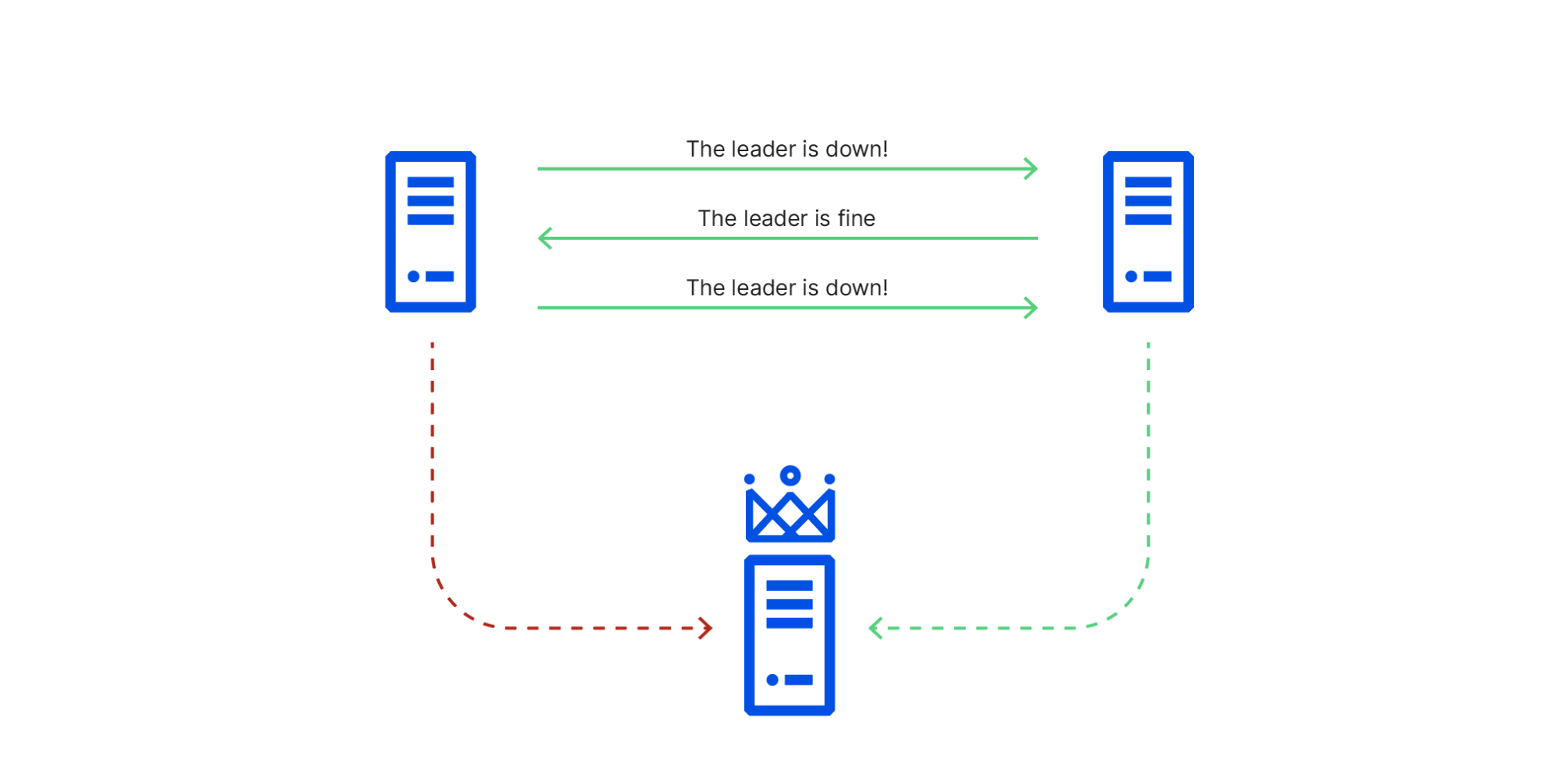
An analysis of the Cloudflare API availability incident on 2020-11-02
When we review design documents at Cloudflare, we are always on the lookout for Single Points of Failure (SPOFs). Eliminating these is a necessary step in architecting a system you can be confident in. Ironically, when you’re designing a system with built-in redundancy, you spend most of your time thinking about how well it functions when that redundancy is lost.
On November 2, 2020, Cloudflare had an incident that impacted the availability of the API and dashboard for six hours and 33 minutes. During this incident, the success rate for queries to our API periodically dipped as low as 75%, and the dashboard experience was as much as 80 times slower than normal. While Cloudflare’s edge is massively distributed across the world (and kept working without a hitch), Cloudflare’s control plane (API & dashboard) is made up of a large number of microservices that are redundant across two regions. For most services, the databases backing those microservices are only writable in one region at a time.
Each of Cloudflare’s control plane data centers has multiple racks of servers. Each of those racks has two switches that operate as a pair—both Continue reading