Heavy Networking 523: OneOncology Boosts WAN Security, Availability With Silver Peak Unity EdgeConnect SD-WAN (Sponsored)
Today's Heavy Networking podcast focuses on a real-world SD-WAN deployment with OneOncology. The organization deployed an SD-WAN solution from Silver Peak, our sponsor for today's podcast, to securely segment and prioritize electronic medical records over other WAN traffic, get better service quality for critical voice and video applications, and ensure the WAN was highly available. Our guests are Robert Holloway, Infrastructure Manager at OneOncology; and Damon Ennis, SVP of Products at Silver Peak.
The post Heavy Networking 523: OneOncology Boosts WAN Security, Availability With Silver Peak Unity EdgeConnect SD-WAN (Sponsored) appeared first on Packet Pushers.
Heavy Networking 523: OneOncology Boosts WAN Security, Availability With Silver Peak Unity EdgeConnect SD-WAN (Sponsored)
Today's Heavy Networking podcast focuses on a real-world SD-WAN deployment with OneOncology. The organization deployed an SD-WAN solution from Silver Peak, our sponsor for today's podcast, to securely segment and prioritize electronic medical records over other WAN traffic, get better service quality for critical voice and video applications, and ensure the WAN was highly available. Our guests are Robert Holloway, Infrastructure Manager at OneOncology; and Damon Ennis, SVP of Products at Silver Peak.Amazon’s Custom Graviton2 Chips Arrive in AWS EC2
Plus, AMD’s second-generation EPYC processors are available on Amazon's Elastic Compute Cloud.
Security and Salt

One of the things I picked up during the quarantine is a new-found interest in cooking. I’ve been spending more time researching recipes and trying to understand how my previous efforts to be a four-star chef have fallen flat. Thankfully, practice does indeed make perfect. I’m slowly getting better , which is to say that my family will actually eat my cooking now instead of just deciding that pizza for the fourth night in a row is a good choice.
One of the things I learned as I went on was about salt. Sodium Chloride is a magical substance. Someone once told me that if you taste a dish and you know it needs something but you’re not quite sure what that something is, the answer is probably salt. It does a lot to tie flavors together. But it’s also a fickle substance. It has the power to make or break a dish in very small amounts. It can be the difference between perfection and disaster. As it turns out, it’s a lot like security too.
Too Much is Exactly Enough
Security and salt are alike in the first way because you need the right amount to make things work. Continue reading
Exploding Security Perimeter, Remote Worker Ramp Spotlights SD-WAN Limits
Security perimeters have exploded as more than 100 million Americans found themselves setting up...
Is 5G Really More Secure? It’s Complicated
5G isn’t a cure all, nor does it somehow build a fortress to blunt any nefarious attempts to do...
Top 5 Cloud Security Posture Management Deals
Since humans are prone to making mistakes, cloud security posture management companies have become...
DevAsc – Some Handy Linux Commands
Introduction
Linux is becoming more and more prominent in the networking industry. Many of us come from a mixed background and have varying levels of knowledge of Linux. I’ve been around Linux for a long time but really never got beyond the very most basic stuff. Looking back, I wish I had spent some more time learning Sed, Awk, regex, and Bash etc. I was doing some labs over at NRE Labs (great labs), and wanted to highlight some of the things I learned.
Appending To a File With Cat
Sometimes you want to append something quickly to a file or send several lines of text to a Linux command. That can be done using “here documents“.
First, look at this small configuration:
daniel@devasc:~/DevAsc$ cat config.txt interface GigabitEthernet0/1 switchport mode access switchport access vlan 10 ! interface GigabitEthernet0/2 switchport mode access switchport access vlan 10 ! interface GigabitEthernet0/3 switchport mode access switchport access vlan 10 !
Now we want to append another interface to the end of this file. We can do that using cat:
daniel@devasc:~/DevAsc$ cat <<EOT >> config.txt > interface GigabitEthernet0/4 > switchport mode access > switchport access vlan 10 > ! > EOT
After the cat command, Continue reading
Cloud-Native Security Remains a Complex Organism
“It’s natural that the security factors become critical because now they're suddenly very large...
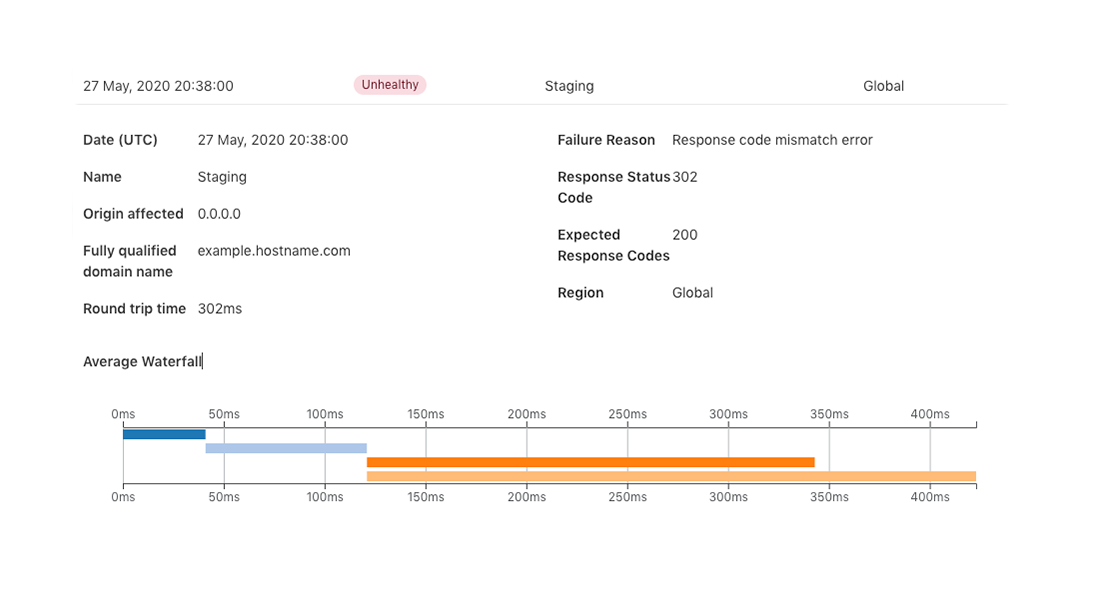
Health Check Analytics and how you can use it
At the end of last year, we introduced Standalone Health Checks - a service that lets you monitor the health of your origin servers and avoid the need to purchase additional third party services. The more that can be controlled from Cloudflare decreases maintenance cost, vendor management, and infrastructure complexity. This is important as it ensures you are able to scale your infrastructure seamlessly as your company grows. Today, we are introducing Standalone Health Check Analytics to help decrease your time to resolution for any potential issues. You can find Health Check Analytics in the sub-menu under the Traffic tab in your Cloudflare Dashboard.
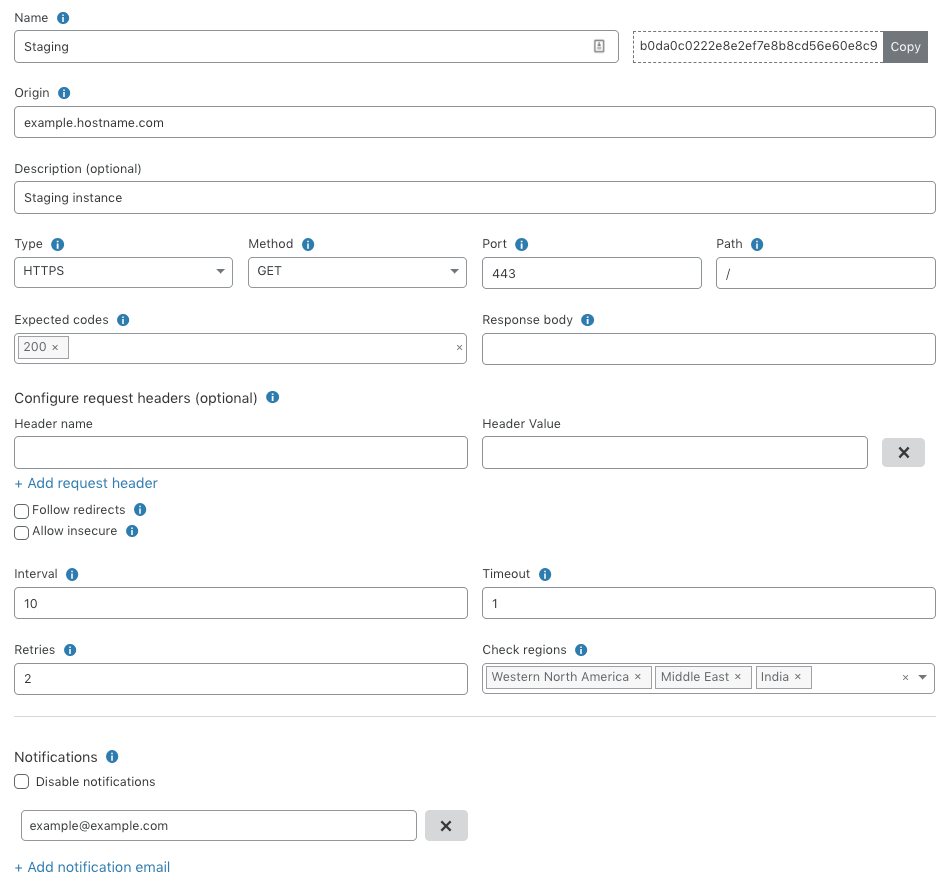
As a refresher, Standalone Health Checks is a service that monitors an IP address or hostname for your origin servers or application and notifies you in near real-time if there happens to be a problem. These Health Checks support fine-tuned configurations based on expected codes, interval, protocols, timeout and more. These configurations enable you to properly target your checks based on the unique setup of your infrastructure. An example of a Health Check can be seen below which is monitoring an origin server in a staging environment with a notification set via email.
Once you set Continue reading
Field Engineering and COVID19

First posted in Human Infrastructure Magazine in April 2020 – a free email newsletter from the Packet Pushers. Subscribe here. How does business operate when the pandemic lockdown ‘ends’ and how does it impact you ? COVID19 won’t be gone, its gonna be months before a new ‘normal’ emerges. Getting back to work means close […]
The post Field Engineering and COVID19 appeared first on EtherealMind.
SuzieQ with Dinesh Dutt and Justin Pietsch on Software Gone Wild
In early May 2020 I wrote a blog post introducing SuzieQ, a network observability platform Dinesh Dutt worked on for the last few years. If that blog post made you look for more details, you might like the Episode 111 of Software Gone Wild in which we went deeper and covered these topics:
- How does SuzieQ collect data
- What data is it collecting from network devices
- What can you do with that data
- How can you customize and extend SuzieQ
Kubernetes Security: Lateral Movement Detection and Defense
What is Lateral Movement?
Lateral movement refers to the techniques that a cyber-attacker uses, after gaining initial access, to move deeper into a network in search of sensitive data and other high-value assets. Lateral movement techniques are widely used in sophisticated cyber-attacks such as advanced persistent threats (APTs). An adversary uses these techniques to access other hosts from a compromised system and get access to sensitive resources, such as mail systems, shared folders, and legitimate credentials, ultimately gaining access to the identified target. Lateral movement techniques enable a threat actor to avoid detection and retain access over an extended dwell time of weeks, or even months, after the initial breach.
What are the Stages of Lateral Movement?
There are three primary stages of lateral movement: reconnaissance, credential/privilege gathering, and gaining access to other resources in the network.
How Does an Adversary Gain Unauthorized Access to a Kubernetes Cluster?
In a Kubernetes cluster, an attacker will gain initial access by compromising a pod. Once the pod is compromised, there are three main areas where the attacker can begin reconnaissance and move through the lateral movement stages to learn more about the cluster: the cloud provider metadata service, the pod networking and Continue reading
GitLab Acquires Peach Tech and Fuzzit to Expand its DevSecOps Offering
GitLab has acquired Peach Tech, a security software firm specializing in protocol fuzz testing and...
SD-WAN an Enterprise Favorite for Securing the Cloud
Of those surveyed, 74% reported had deployed or plan to deploy SD-WAN to secure cloud workloads.
Cradlepoint Partners With Rigado to Deliver a Safe Workplace Solution Using NetCloud Edge Containers and Built on Microsoft Azure
Cradlepoint announced that Rigado joined its Technology Alliance Partner program to build a Safe...
Daily Roundup: Amazon Won’t Sell Facial Recognition to Police
Amazon said it wouldn't sell facial recognition to police; Nokia mellowed its 5G outlook for 2020;...
Microsoft Joins Amazon, IBM With Facial Recognition Ban
Company President Brad Smith said it does not sell that technology today and is in favor of a...