Daily Roundup: Cisco Patches Firewall Bugs
Cisco patched firewall bugs; Amazon threw another JEDI tantrum fit ; and Dish fought off critics,...
Heavy Networking 516: Is LISP The Overlay Of The Future?
On today's Heavy Networking podcast, guest Cory Steele visits the podcast to make the case that overlays such as LISP offer unique benefits for the network. Greg Ferro disagrees, and makes the case for protocols like QUIC, TLS, and IPSec, and argues for the concept of end-to-end connectivity as the IP network was intended.
The post Heavy Networking 516: Is LISP The Overlay Of The Future? appeared first on Packet Pushers.
Heavy Networking 516: Is LISP The Overlay Of The Future?
On today's Heavy Networking podcast, guest Cory Steele visits the podcast to make the case that overlays such as LISP offer unique benefits for the network. Greg Ferro disagrees, and makes the case for protocols like QUIC, TLS, and IPSec, and argues for the concept of end-to-end connectivity as the IP network was intended.Getting Started with pyATS (and Genie)
What is Python Automated Test System (pyATS)? None of the answers I found to this question really made much sense to me initially. A Python3 based Test Automation and Validation Framework developed by Cisco (but open and extensible to any vendor) is probably the best short answer but still too vague. Add in Genie because, READ MORE
The post Getting Started with pyATS (and Genie) appeared first on The Gratuitous Arp.
Internet During Shutdown: Do We Need More Internet?

The Internet Society India Chennai Chapter organized a virtual roundtable in March, a few days after the Indian government announced a three-week nationwide lockdown. The virtual roundtable was a conversation on the importance of keeping the Internet open, and on the ways in which the Internet community could contribute to COVID-19 response and recovery in India and around the globe.
The virtual roundtable brought together a wide range of Internet stakeholders, including Andrew Sullivan, Jane Coffin, Mike Godwin, Yrjö Länsipuro, Wolfgang Kleinwächter, Olivier Crepin-Leblond, Sébastien Bachollet, Samiran Gupta, and Glen McKnight, as well as members of the Chapter from civil society and the private sector.
Some key highlights and takeaways from the virtual roundtable include the following:
The COVID-19 pandemic underscores the importance of the Internet. Without access, people are unable to communicate with family members and health workers, and participate in online learning and remote work.
The pandemic has clearly exposed the inequalities in Internet access and affordability – the digital divide across the region. Connecting the billions of people who are not yet connected must be a priority. At the same time, their privacy and autonomy must be protected.
Internet technologies can help us fight against the pandemic. Continue reading
Dish Fights Off Critics, Claims 5G Efforts on Track
Despite the calamity brought on by COVID-19, Dish still plans to launch 5G service in a single...
Weekly Wrap: Nutanix Furloughs 25% of Workforce Citing COVID-19
SDxCentral Weekly Wrap for May 8, 2020: Nutanix to furlough 25% of its workforce; IBM wears Red Hat...
‘SD-WAN Has to Evolve,’ Says Cisco Exec
Steven Wood, Cisco’s principal engineer of enterprise architectures and SD-WAN, made the...
Amazon Files Another JEDI Protest, Microsoft Says ‘Stop Asking for Do-Over’
Microsoft called Amazon’s latest JEDI protest “yet another attempt to force a re-do because...
The Devil Is In The Licensing

If you don’t already know that I’m a co-host of a great podcast we do at Gestalt IT, here’s a great way to jump in. This episode was a fun one to record and talk about licensing:
Sometimes I have to play the role of the genial host and I don’t get to express my true opinion on things. After all, a good podcast host is really just there to keep the peace and ensure the guests get to say their words, right?
Double Feature
I once said that every random feature in a certain network operating system somehow came from a million-dollar PO that needed to be closed. It reflects my personal opinion that sometimes the things we see in code don’t always reflect reality. But how do you decide what to build if you’re not listening to customers?
It’s a tough gamble to take. You can guess at what people are going to want to include and hope that you get it right. Other times you’re going to goof and put something your code that no one uses. It’s a delicate balance. One of the biggest traps that a company can fall into is waiting for their Continue reading
CUBIC and HyStart++ Support in quiche
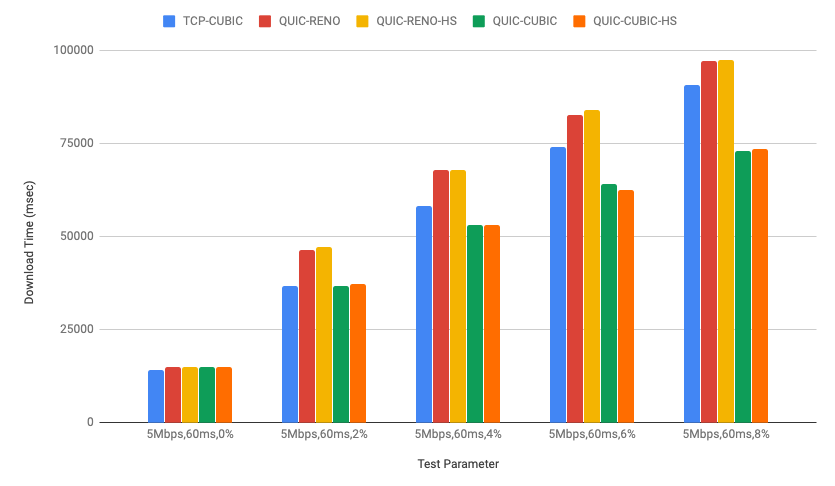
quiche, Cloudflare's IETF QUIC implementation has been running CUBIC congestion control for a while in our production environment as mentioned in Comparing HTTP/3 vs. HTTP/2 Performance). Recently we also added HyStart++ to the congestion control module for further improvements.
In this post, we will talk about QUIC congestion control and loss recovery briefly and CUBIC and HyStart++ in the quiche congestion control module. We will also discuss lab test results and how to visualize those using qlog which was recently added to the quiche library as well.
QUIC Congestion Control and Loss Recovery
In the network transport area, congestion control is how to decide how much data the connection can send into the network. It has an important role in networking so as not to overrun the link but also at the same time it needs to play nice with other connections in the same network to ensure that the overall network, the Internet, doesn’t collapse. Basically congestion control is trying to detect the current capacity of the link and tune itself in real time and it’s one of the core algorithms for running the Internet.
QUIC congestion control has been written based on many years of TCP Continue reading
Video: Internet Has More than One Administrator
It’s amazing how many people assume that The Internet is a thing, whereas in reality it’s a mishmash of interconnected independent operators running mostly on goodwill, misplaced trust in other people’s competence, and (sometimes) pure dumb luck.
I described a few consequences of this sad reality in the Internet Has More than One Administrator video (part of How Networks Really Work webinar), and Nick Buraglio and Elisa Jasinska provided even more details in their Surviving the Internet Default-Free Zone webinar.
Cisco Firewall Bugs Leave Networks Vulnerable to Attacks
The Cisco Adaptive Security Appliance alone has more than 1 million deployments globally, according...
Linux Foundation, ToIP Foundation Unite to Tackle Digital Trust
The ToIP Foundation aims to establish a common standard for consumers and businesses to ensure data...
Daily Roundup: Fortinet Weathers Pandemic
Fortinet Q1 earnings remained strong amidst pandemic; Microsoft eyed a $170M security buy; and...
This Switcheroo Doesn’t Get Old
Any company that holds more than a quarter of a market – by money or shipments – is doing pretty well. …
This Switcheroo Doesn’t Get Old was written by Timothy Prickett Morgan at The Next Platform.
Calico Enterprise 3.0 – Global Network Security Center for Kubernetes
As our enterprise customers build out large, multi-cluster Kubernetes environments, they are encountering an entirely new set of security challenges, requiring solutions that operate at scale and can be deployed both on-premises and across multiple clouds.
Today we are thrilled to announce the release of Calico Enterprise 3.0 and the availability of our Global Network Security Center, a game-changing solution that provides a central management plane for network security across every Kubernetes cluster in your organization.
Global Network Security Center for Kubernetes
The Calico Enterprise Global Network Security Center for Kubernetes is a centralized management plane and single point of control for multi-cluster and multi-cloud environments. Calico Enterprise’s centralized control simplifies and speeds routine maintenance, leaving more time for your platform team to address other important tasks.
For example, instead of logging in to 50 clusters one-at-a-time to make a policy change, with a single log-in to Calico Enterprise you can apply policy changes consistently across all 50 clusters. You can also automatically apply existing network security controls to new clusters as they are added.

Calico Enterprise also includes centralized log management, troubleshooting with Flow Visualizer, and cluster-wide IDS (intrusion detection). GNSC provides compliance reporting, and alerts on non-compliance Continue reading
T-Mobile US Forecasts $667M COVID-19 Hit
T-Mobile US expanded its 5G network running on 600 MHz spectrum by activating 1,600 sites during...
Fortinet Weathers Pandemic Storm, Posts Robust Q1 Earnings
“Our ability to directly manage our supply chain and shipping logistics allowed us to quickly...