Living on the Edge
Having enjoyed the benefits of an increasingly digital existence, most consumers are not only willing but demand to continue living on the edge.Industry-First Pay-as-you-go SaaS Platform for Kubernetes Security and Observability
We are excited to introduce Calico Cloud, a pay-as-you-go SaaS platform for Kubernetes security and observability. With Calico Cloud, users only pay for services consumed and are billed monthly, getting immediate value without upfront investment.
Introduction
Calico Cloud gives DevOps, DevSecOps, and Site Reliability Engineering (SRE) teams a single pane of glass across multi-cluster and multi-cloud Kubernetes environments to deploy a standard set of egress access controls, enforce security policies, ensure compliance, get end-to-end visibility, and troubleshoot applications. Calico Cloud is Kubernetes-native and provides native extensions to enable security and observability as code for easy and consistent enforcement across Kubernetes distributions, multi-cloud and hybrid environments. It scales automatically with the managed clusters according to the user requirements to ensure uninterrupted real-time visibility at any scale.
Security and Observability Challenges
- North-South Controls: Often microservices need to communicate with services or API endpoints running outside the Kubernetes cluster. Implementing access control from Kubernetes pods to external endpoints is hard. Most traditional or cloud provider’s firewalls do not understand the Kubernetes context which forces the ops team to allow traffic from the entire cluster or a set of worker nodes.
- East-West Controls: Even after effective perimeter-based north-south controls, the organizations face challenges to Continue reading
Network Break 320: Juniper Rebrands Service Provider Automation Offerings; Fortinet Gets SASE With Latest OS
This week's Network Break dives into Juniper reorganizing and rebranding automation products as the Paragon portfolio, new SASE and ZTNA capabilities from Fortinet, the rise of cyber-insurance premiums, an HPE server getting launched into space, and more tech news.
The post Network Break 320: Juniper Rebrands Service Provider Automation Offerings; Fortinet Gets SASE With Latest OS appeared first on Packet Pushers.
Network Break 320: Juniper Rebrands Service Provider Automation Offerings; Fortinet Gets SASE With Latest OS
This week's Network Break dives into Juniper reorganizing and rebranding automation products as the Paragon portfolio, new SASE and ZTNA capabilities from Fortinet, the rise of cyber-insurance premiums, an HPE server getting launched into space, and more tech news.Anthos developer sandbox demo
Anthos developer sandbox is pretty cool as it allows developers to experience Kubernetes/GKE/Anthos from right inside their favorite IDE. I made the following demo to showcase how you can use Anthos developer sandbox.Availability Zones and Regions in AWS, Azure and GCP
My friend Daniel Dib sent me this interesting question:
As I understand it, subnets in Azure span availability zones. Do you see any drawback to this? Does subnet matter if your VMs are in different AZs?
I’m positive I don’t have to tell you what networks, subnets, and VRFs are, but you might not have worked with public cloud availability zones before. Before going into the details of Daniel’s question (and it will take us three blog posts to get to the end), let’s introduce regions and availability zones (you’ll find more details in AWS Networking and Azure Networking webinars).
Availability Zones and Regions in AWS, Azure and GCP
My friend Daniel Dib sent me this interesting question:
As I understand it, subnets in Azure span availability zones. Do you see any drawback to this? Does subnet matter if your VMs are in different AZs?
I’m positive I don’t have to tell you what networks, subnets, and VRFs are, but you might not have worked with public cloud availability zones before. Before going into the details of Daniel’s question (and it will take us three blog posts to get to the end), let’s introduce regions and availability zones (you’ll find more details in AWS Networking and Azure Networking webinars).
Farewell to Northbound Networks
Digging through my office looking for some other technology which I had misplaced, I stumbled across a small box containing a Northbound Networks Zodiac-FX, a small 4-port FastEthernet OpenFlow SDN switch which I had picked up after backing a 2015 kickstarter campaign.
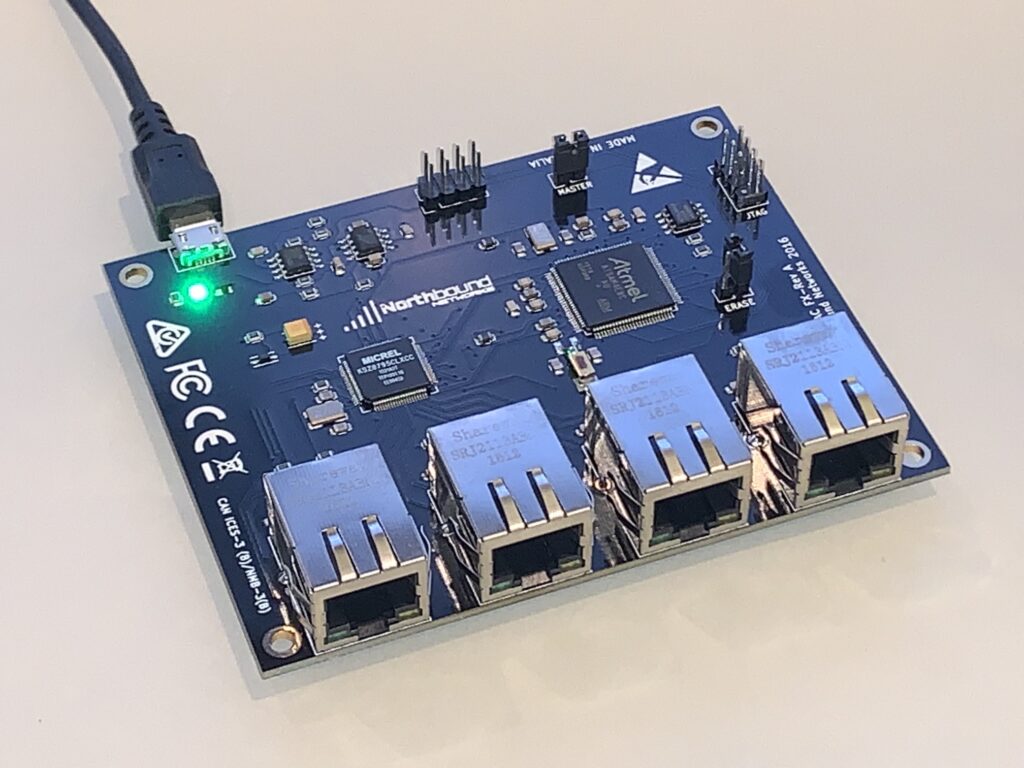
These were a pretty cool idea, and at the time OpenFlow (OF) was the hottest thing around, everything was being SDN-washed, and the idea that a regular user like myself could afford actual hardware with OF capabilities to toy with in the home lab was beyond belief. Of course, it was possible to virtualize OF with Mininet, but there’s something about using a real switch that goes beyond that. Even though, as you’ll in a future post, I ended up wasting that opportunity, I am still honored to have backed it, and my hat is off to Northbound Networks’ founder Paul Zanna for what he has accomplished.
Paying My Respects
With that in mind, I’m sad to note that when I went to the Northbound Networks website, I discovered that some time around August 2020 the company stopped manufacturing SDN hardware.
Since the original Zodiac FX campaign, Paul had expanded the available products to include an 802. Continue reading
Rethinking BGP on the DC Fabric (part 3)
The fist post on this topic considered some basic definitions and the reasons why I am writing this series of posts. The second considered the convergence speed of BGP on a dense topology such as a DC fabric, and what mechanisms we normally use to improve BGP’s convergence speed. This post considers some of the objections to slow convergence speed—convergence speed is not important, and ECMP with high fanouts will take care of any convergence speed issues. The network below will be used for this discussion.

Two servers are connected to this five-stage butterfly: S1 and S2 Assume, for a moment, that some service is running on both S1 and S2. This service is configured in active-active mode, with all data synchronized between the servers. If some fabric device, such as C7, fails, traffic destined to either S1 or S2 across that device will be very quickly (within tens of milliseconds) rerouted through some other device, probably C6, to reach the same destination. This will happen no matter what routing protocol is being used in the underlay control plane—so why does BGP’s convergence speed matter? Further, if these services are running in the overlay, or they are designed to discover Continue reading
Negotiating your maximum salary
If you are not negotiating your salary, you are almost certainly leaving money on the table. Negotiation is an important career skill and activity because it provides a very nice upside in overall career earnings. Preparation is important because the person you are negotiating with probably has a lot more experience in salary negotiations than […]
The post Negotiating your maximum salary appeared first on Packet Pushers.
How CFOs Accelerate Modernization with Cloud Economics
It's important to choose a cloud infrastructure that can evolve to support the workloads and the associated SLAs while at a price point that resonates with CFOs.The Week in Internet News: No Internet, No Vaccine

Unhealthy access: People lacking Internet access in the U.S., including some racial minorities, may be missing out on COVID-19 vaccines, The Conversation suggests. Signing up for the vaccine in the U.S. has largely happened online, meaning fewer seniors from underserved minority communities have been able to make appointments. In addition, people without Internet access have missed out on other health resources during the pandemic, as the use of telehealth services has skyrocketed during the pandemic.
Permission to be social: Mexican Senator Ricardo Monreal has proposed regulations for social media companies that would require them to “request authorization” from the country’s telecom regulator in order to continue operating in the country, Reuters reports. The Latin American Internet Association is protesting against the proposal, saying it would violate the United States-Mexico-Canada Agreement and create unjustified trade barriers.
No sale: U.S. President Joe Biden has paused the proposed sale of TikTok from Chinese owner ByteDance to Oracle and Walmart after former President Donald Trump raised security concerns about the app, NPR reports. Trump had threated to ban the video sharing app unless it was sold, but the Biden administration will undertake “a wide-ranging probe into how Chinese-owned technology companies could Continue reading
Tech Bytes: MSSP Partners With Fortinet To Deliver Secure SD-WAN (Sponsored)
Today's Tech Bytes podcast from the Packet Pushers is a conversation with Node4, a managed security service provider that's deploying and operating Fortinet’s Secure SD-WAN for its customers. Fortinet is our sponsor. Our guest from Node4 is Glenn Akester, Lead Network Services Architect.Tech Bytes: MSSP Partners With Fortinet To Deliver Secure SD-WAN (Sponsored)
Today's Tech Bytes podcast from the Packet Pushers is a conversation with Node4, a managed security service provider that's deploying and operating Fortinet’s Secure SD-WAN for its customers. Fortinet is our sponsor. Our guest from Node4 is Glenn Akester, Lead Network Services Architect.
The post Tech Bytes: MSSP Partners With Fortinet To Deliver Secure SD-WAN (Sponsored) appeared first on Packet Pushers.
Rant: Don’t Ever Compare Enterprise IT Shenanigans with Apollo 13
Here’s a recent tweet by my friend Joe Onisick that triggered this blog post:
My favorite people are the ones that start with “how could we make that work?” Before jumping into all of their preconceived bs on why it won’t work.
I couldn’t agree more with that sentiment. The number of people who would invent all sorts of excuses just to avoid turning on their brains and keep to their cozy old methods is staggering. Unfortunately, someone immediately had the urge to switch into what I understood to be a heroic MacGyver mode (or maybe it was just my lack of caffeine, in which case I apologize for the misquote… but you might still like the rest of the rant):