The First Ethiopia Internet Development Conference: Meeting Challenge and Opportunity Head On

When it comes to Ethiopia’s future online, there are many reasons to feel optimistic.
The country has one of the fastest-growing economies in the region, is strategically placed, and has a population of over 105 million, 60% of whom are under the age of 30. All of these are assets to make it a regional digital giant.
But this won’t happen unless Ethiopia takes some strategic moves. Internet penetration is still very low compared to its peers in Africa. The rural areas are still largely unconnected to the Internet. Only cities enjoy 3G access and 4G is only available in the capital. In spite of successive price cuts by Ethio telecom in the last year, the Internet is not affordable for the majority of Ethiopians.
It’s not that the government has not wanted to connect the rural areas. In fact, the rationale that the Ethiopian government had to keep the monopoly was to use the money generated from cities to invest in the rural areas. However, this strategy has clearly not worked since Ethiopia’s rural areas are not better connected than those in countries that have not had a government monopoly on the sector, such as Kenya.
It is Continue reading
Daily Roundup: Nokia CEO Walks the Plank
Nokia CEO walked the plank; VMware's winning streak came to a screeching halt; and Marvell injected...
Internet Society Ethiopia Chapter Launched Today!

We are excited about the momentum behind Ethiopia.
It is a rare moment in any country’s history to undergo such a positive transformation. It’s a time of immense optimism and investment potential. It’s not a surprise as the country also has one of the fastest-growing economies in the region, is strategically placed, and has a young population of over 105 million – half of whom are under the age of 18.
While we’ve been active in the Internet world for many years, the time to start a Chapter in Ethiopia is absolutely now. With that, let me share our “why” and introduce ourselves.
We are the Internet Society Ethiopia Chapter.
The idea of starting an Internet Society Chapter came to us during a workshop in the city of Bahir Dar, where we became conscious of the fact that more than 85% of the Ethiopia population is losing countless opportunities every day because they don’t have access to the Internet. We believe the Internet is for everyone and we are here to work with all people – from communities to businesses to governments and ordinary people to connect the unconnected and create a bigger and stronger Internet in Ethiopia. What drives Continue reading
Infor, Snowflake Unite to Birst Open BI Analytics
Joint customers will be able utilize Birst's integrated end-to-end platform for building automated...
Network Break 273: Fortinet Pits Deep Learning Appliance Against Malware; Nokia ‘Reviews Options’ As Earnings Struggle
Take a Network Break. This week's IT news analysis covers a new anti-malware appliance from Fortinet, VMware security software for data centers and clouds, Nokia's efforts to buy time as it gets its 5G house in order, and financial results from multiple vendors.Network Break 273: Fortinet Pits Deep Learning Appliance Against Malware; Nokia ‘Reviews Options’ As Earnings Struggle
Take a Network Break. This week's IT news analysis covers a new anti-malware appliance from Fortinet, VMware security software for data centers and clouds, Nokia's efforts to buy time as it gets its 5G house in order, and financial results from multiple vendors.
The post Network Break 273: Fortinet Pits Deep Learning Appliance Against Malware; Nokia ‘Reviews Options’ As Earnings Struggle appeared first on Packet Pushers.
Similarities Between AWS VPC and Cisco SDA – Intra-Subnet Communication
Update March 6, 2020: This post will be obsolete soon by a new version
Forewords
There are two main reasons for writing this document:
First, Cisco SDA is an on-prem LAN model while the AWS VPC is an off-prem DC solution. I wanted to point out that these two solutions, even though used for very different purposes, use the same kind of Control-Plane operation and Data-Plane encapsulation and are managed via QUI. This is kind of my answer to ever going discussion about is there DC-networks, Campus-networks and so on, or is there just networks.
Second, my own curiosity to understand the operation of AWS VPC.
I usually start by introducing the example environment and then explaining the configuration, moving to Control-Plane operation and then to Data-Plane operation. However, this time I take a different approach. This article first introduces the example environment but then the Data-Plane operation is discussed before Control-Plane operation. This way it is easier to understand what information is needed and how that information is gathered.
Continue reading
Cisco’s Wendy Nather: Never Say This to a CISO
When Cisco acquired Duo Security, Nather’s was the only CISO advisory team. Cisco quickly saw the...
Marvell Injects New Life Into Infrastructure Chips
The chips are designed to power networking equipment like switches, routers, secure gateways,...
Nokia Taps New Captain After Missing 5G Boat
Pekka Lundmark, who currently serves as president and CEO of Fortum, an energy company also...
Heavy Networking 504: The State Of Optical Networking In 2020
If you're new to DWDM and optical networking, this Heavy Networking episode aims to peel back some of the layers of these technologies to help you understand how they work, and whether you have business applications that could use DWDM. My guest is Chris Tracy, a network and systems engineer at ESnet.Heavy Networking 504: The State Of Optical Networking In 2020
If you're new to DWDM and optical networking, this Heavy Networking episode aims to peel back some of the layers of these technologies to help you understand how they work, and whether you have business applications that could use DWDM. My guest is Chris Tracy, a network and systems engineer at ESnet.
The post Heavy Networking 504: The State Of Optical Networking In 2020 appeared first on Packet Pushers.
Tech Bytes: Is SDN A Revolution Or An Evolution Of Traditional Networks? (Sponsored)
On today's Tech Bytes podast we talk with sponsor CodiLime about the benefits of SDN, how SDN works, and CodiLime's network engineering services that help organizations of all sizes migrate to SDN. Our guest Monika Antoniak, head of R&D at CodiLime.
The post Tech Bytes: Is SDN A Revolution Or An Evolution Of Traditional Networks? (Sponsored) appeared first on Packet Pushers.
Tech Bytes: Is SDN A Revolution Or An Evolution Of Traditional Networks? (Sponsored)
On today's Tech Bytes podast we talk with sponsor CodiLime about the benefits of SDN, how SDN works, and CodiLime's network engineering services that help organizations of all sizes migrate to SDN. Our guest Monika Antoniak, head of R&D at CodiLime.The Week in Internet News: Let’s Encrypt Hits One Billion Certificates

Encryption wave: Let’s Encrypt, the website encryption project supported by the Internet Society, has issued 1 billion web security certificate, ZDNet reports. About 81 percent of the world’s websites now are secured with Transport Layer Security (TLS) encryption, and Let’s Encrypt, which offers free TLS certificates, now serves nearly 200 million websites.
Even more encryption: In other encryption news, the Firefox browser has begun turning on DNS over HTTPS (DoH) by default for users in the U.S., The Verge says. The encryption tool secures Internet traffic, including browsing histories.
No more WiFi: Google is shutting down a free Wi-Fi service called Station that has served parts of India, Indonesia, South Africa, Mexico, Thailand, Nigeria, Philippines, Brazil and Vietnam. TechCrunch reports. Google says the service is no longer needed because of falling prices for mobile broadband service. Google also struggled to find a business model.
Keep your hands off the network: Employees are increasingly connecting their personal Internet of Things devices, like smart watches and fitness trackers, to corporate networks, according to research by Zscaler, detailed at ZDNet. These unauthorized connections undermine network security. The most connected personal devices included digital home assistants, TV set-top boxes, video cameras, smart-home Continue reading
When Bloom filters don’t bloom
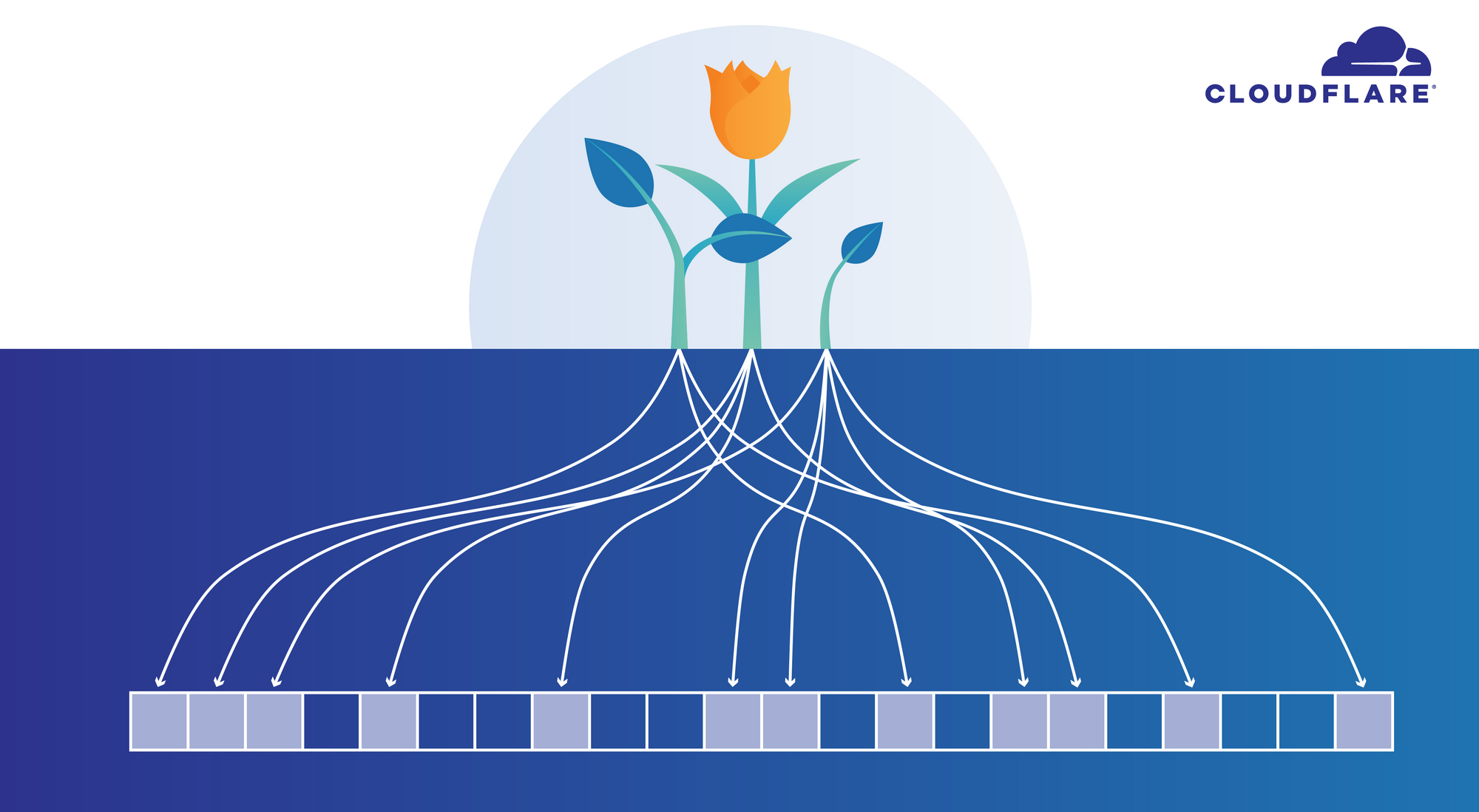
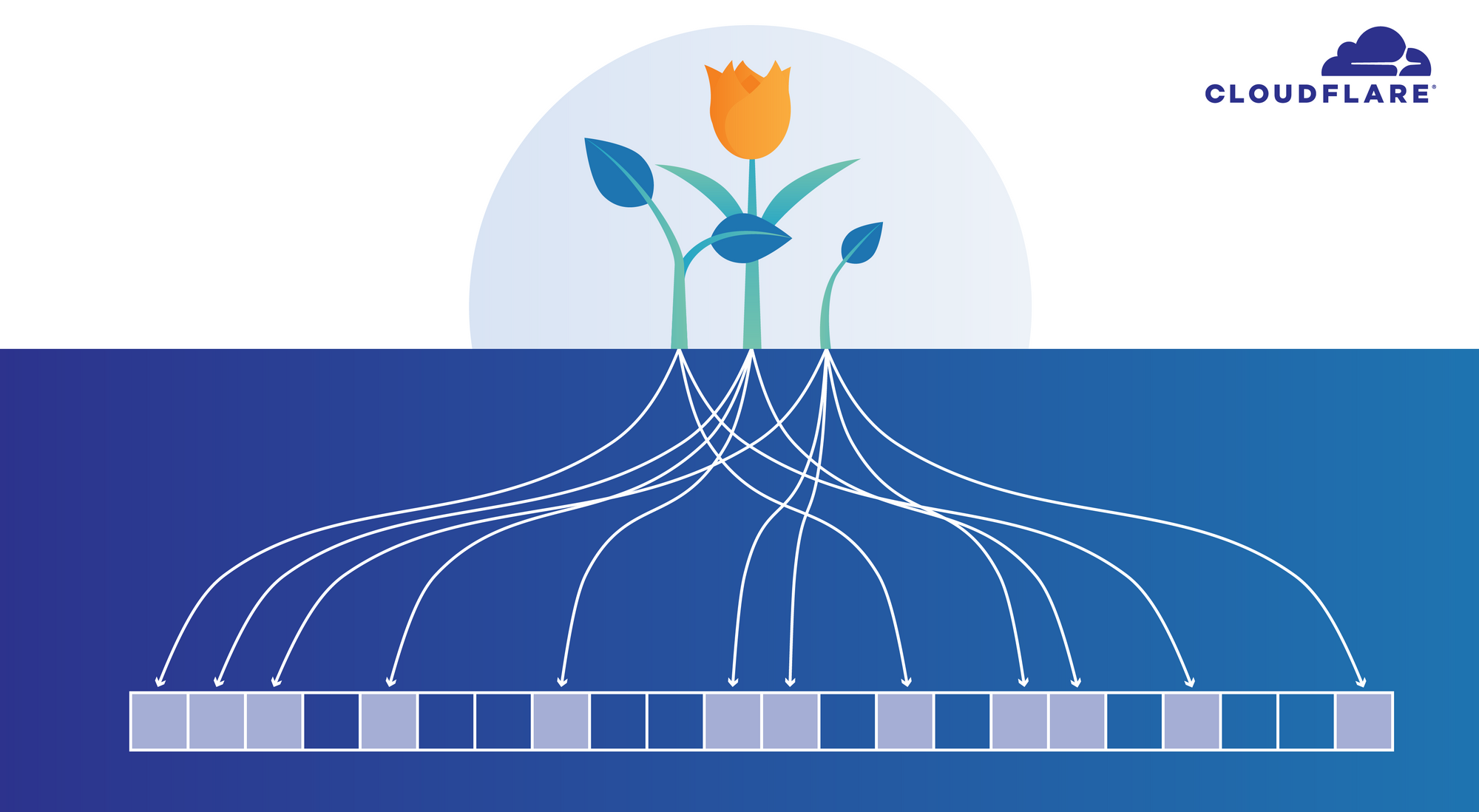
I've known about Bloom filters (named after Burton Bloom) since university, but I haven't had an opportunity to use them in anger. Last month this changed - I became fascinated with the promise of this data structure, but I quickly realized it had some drawbacks. This blog post is the tale of my brief love affair with Bloom filters.
While doing research about IP spoofing, I needed to examine whether the source IP addresses extracted from packets reaching our servers were legitimate, depending on the geographical location of our data centers. For example, source IPs belonging to a legitimate Italian ISP should not arrive in a Brazilian datacenter. This problem might sound simple, but in the ever-evolving landscape of the internet this is far from easy. Suffice it to say I ended up with many large text files with data like this:

This reads as: the IP 192.0.2.1 was recorded reaching Cloudflare data center number 107 with a legitimate request. This data came from many sources, including our active and passive probes, logs of certain domains we own (like cloudflare.com), public sources (like BGP table), etc. The same line would usually be repeated across multiple Continue reading
My Cisco Certified DevNet Associate Journey by Nick Russo
On 27 February 2020, I took and passed the Cisco Certified DevNet Associate (DEVASC) exam on my first attempt. TLDR; it was a well-structured and fair exam. I think it was my favorite Cisco exam of all time. It had clear questions, good depth, no off-blueprint curveballs, and a great measure of candidate skill. The distribution of questions was also in accordance with the blueprint topic weights.
I’m known for being a concise and high signal-to-noise blogger, so I won’t turn this into a blueprint exploration article. You can learn more about the official certification here. Instead, I’ll focus on how I prepared for this exam.
Above all else, you need to sign up for an account at Cisco DevNet. It’s 100% free and contains many excellent resources to help you learn software-related topics. This is more than just “network automation” as you’ll be exposed to software development techniques and strategies, too. While everything on DevNet is useful, I believe the following three resources are the most important for this exam. Learning the content and passing any DevNet exam would be almost impossible without them:
- Sandboxes: These are demo environments that learners can use for testing specific products and Continue reading
Automation Story: Network Diagrams
Anne Baretta got pretty far in his automation story: after starting with configuration templates and storing network inventory into a database, he tackled the web UI. What’s next? How about a few auto-generated network diagrams?
Notes
- We covered the magic behind network diagrams in our network automation course.
- For whatever reason, I see numerous networking engineers focusing on generating useful network diagrams. Wasn’t that problem solved ages ago with miraculous single-pane-of-glass network management software?
Automation Story: Network Diagrams
Anne Baretta got pretty far in his automation story: after starting with configuration templates and storing network inventory into a database, he tackled the web UI. What’s next? How about a few auto-generated network diagrams?
Notes
- We covered the magic behind network diagrams in our network automation course.
- For whatever reason, I see numerous networking engineers focusing on generating useful network diagrams. Wasn’t that problem solved ages ago with miraculous single-pane-of-glass network management software?