Juniper Apstra Part I – Introducing a true IBNS
With this post, we kick off a new series based on Juniper Apstra. This post serves as an introduction to Apstra - we’ll look at what a true IBN system is, how relational and graph databases are different (and why graph databases are ideal for network infrastructure), concluding with some general workflows in Apstra.
Cloud Notes: AWS IAM
AWS Identity and Access Management (IAM) provides access control for AWS users/applications to the various AWS services and resources. Features Available only in the Global region Globally resiliant service Always free service Account Types There are a number of account...continue reading
Telecom Industry Takes the Workforce Challenge to Staff Internet-for-All Broadband Rollout
Demand for skilled staff is sky high, but not supply, for the largest-ever U.S. infrastructure effort. Associations, carriers, and vendors look to fill the staffing gap as spending on fiber broadband climbs.Hedge 136: The IPv6 ULA Mess
IPv6’s designers built the concept of Unique Local Addresses, or ULAs, into the addressing architecture to make network address translation unnecessary for IPv6 deployments. As with many other plans of mice and men, however, the unintended consequences of what is a good idea tend to get in the way. Nick Buraglio joing Eyvonne Sharp, Tom Ammon, and Russ White to discuss the many problems of IPv6 ULA, why it isn’t practical in most network deployments, and the larger question of how standards bodies sometimes fail to consider the unintended consequences of a good idea.
GreenLake: Finally, A Platform That HPE Utterly Controls
Both Hewlett-Packard and Compaq, which also included parallel database system maker Tandem and minicomputer innovator Digital Equipment Corp when HP bought Compaq for $25 billion back in September 2001, had histories as platform providers but the combined companies were not able to create on the X86 platform the kinds of venerable platforms such as the HP 3000 and DEC VAX and AlphaServer minicomputers, the HP 9000 Unix systems, or the Tandem NonStop systems. …
GreenLake: Finally, A Platform That HPE Utterly Controls was written by Timothy Prickett Morgan at The Next Platform.
Day Two Cloud 153: IaC With GPPL Or DSL? IDK
On Day Two Cloud we’ve had a lot of conversations about using infrastructure as code. We’ve looked at solutions like Ansible, Terraform, the AWS CDK, and Pulumi. Which begs the question, which IaC solution should you learn? A Domain Specific Language (DSL)? A General Purpose Programming Language (GPPL)? Something else? We discuss.Internet Explorer, we hardly knew ye
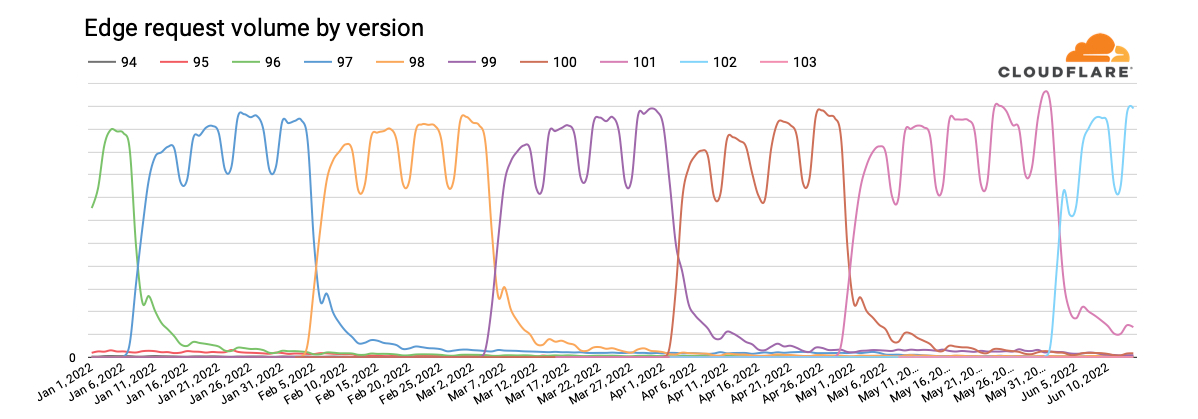
On May 19, 2021, a Microsoft blog post announced that “The future of Internet Explorer on Windows 10 is in Microsoft Edge” and that “the Internet Explorer 11 desktop application will be retired and go out of support on June 15, 2022, for certain versions of Windows 10.” According to an associated FAQ page, those “certain versions” include Windows 10 client SKUs and Windows 10 IoT. According to data from Statcounter, Windows 10 currently accounts for over 70% of desktop Windows market share on a global basis, so this “retirement” impacts a significant number of Windows systems around the world.
As the retirement date for Internet Explorer 11 has recently passed, we wanted to explore several related usage trends:
- Is there a visible indication that use is declining in preparation for its retirement?
- Where is Internet Explorer 11 still in the heaviest use?
- How does the use of Internet Explorer 11 compare to previous versions?
- How much Internet Explorer traffic is “likely human” vs. “likely automated”?
- How do Internet Explorer usage patterns compare with those of Microsoft Edge, its replacement?
The long goodbye
Publicly released in January 2020, and automatically rolled out to Windows users starting Continue reading
Live-patching security vulnerabilities inside the Linux kernel with eBPF Linux Security Module


Linux Security Modules (LSM) is a hook-based framework for implementing security policies and Mandatory Access Control in the Linux kernel. Until recently users looking to implement a security policy had just two options. Configure an existing LSM module such as AppArmor or SELinux, or write a custom kernel module.
Linux 5.7 introduced a third way: LSM extended Berkeley Packet Filters (eBPF) (LSM BPF for short). LSM BPF allows developers to write granular policies without configuration or loading a kernel module. LSM BPF programs are verified on load, and then executed when an LSM hook is reached in a call path.
Let’s solve a real-world problem
Modern operating systems provide facilities allowing "partitioning" of kernel resources. For example FreeBSD has "jails", Solaris has "zones". Linux is different - it provides a set of seemingly independent facilities each allowing isolation of a specific resource. These are called "namespaces" and have been growing in the kernel for years. They are the base of popular tools like Docker, lxc or firejail. Many of the namespaces are uncontroversial, like the UTS namespace which allows the host system to hide its hostname and time. Others are complex but straightforward - NET and NS (mount) namespaces Continue reading
HPE Is The First Big OEM To Adopt Ampere Computing Arm Chips
Hewlett Packard Enterprise has been an early and enthusiastic supporter of alternate processor architectures outside of the standard Xeon X86 CPUs that comprise the vast majority of its revenues and shipments, particularly with Arm server chips starting in 2011. …
HPE Is The First Big OEM To Adopt Ampere Computing Arm Chips was written by Timothy Prickett Morgan at The Next Platform.
Tigera has been awarded Microsoft’s 2022 Partner of the Year award for OSS on Azure
We are proud to announce that we have won the 2022 Microsoft OSS on Azure Partner of the Year award! The Microsoft Partner of the Year Awards recognize Microsoft partners that have developed and delivered outstanding Microsoft-based applications, services, and devices during the past year. Awards were classified in various categories, with honorees chosen from a set of more than 3,900 submitted nominations from more than 100 countries worldwide. Tigera was recognized for providing outstanding solutions and services for open source on Azure.
Since June 2021, Tigera and Microsoft Azure together provide users with active build, deploy, and runtime security with full-stack observability for securing, monitoring, and troubleshooting containers on Azure and AKS. Tigera works closely with Microsoft to offer networking, security, and observability for containerized workloads running in Microsoft Azure.
We are very proud to be recognized as Microsoft’s Partner of the Year for OSS on Azure as it re-affirms the reach and pervasiveness of Tigera’s Calico Open Source solution for container networking and security on Azure and AKS. As enterprises standardize across Microsoft Azure, customers require a resource-efficient and scalable networking and security solution that protects the workloads in a hybrid environment extending from the cloud (Azure and Continue reading
NOAA Gets 3X More Oomph For Weather Forecasting; It Needs 3,300X
Until exascale supercomputers get a lot cheaper, which will allow weather forecasting models to run at a much smaller resolution – and more frequently – to deliver hyper-local weather forecasts, the actual weather forecasting is still going to be done by people. …
NOAA Gets 3X More Oomph For Weather Forecasting; It Needs 3,300X was written by Timothy Prickett Morgan at The Next Platform.
Project Arctic Means VMware Doesn’t Get Left Out In the Hybrid Cold
Enterprises have been shifting many of their workloads into the cloud to take advantage of the scalability, efficiencies, and economics those environments offer. …
Project Arctic Means VMware Doesn’t Get Left Out In the Hybrid Cold was written by Jeffrey Burt at The Next Platform.