Cloudflare thwarts 17.2M rps DDoS attack — the largest ever reported
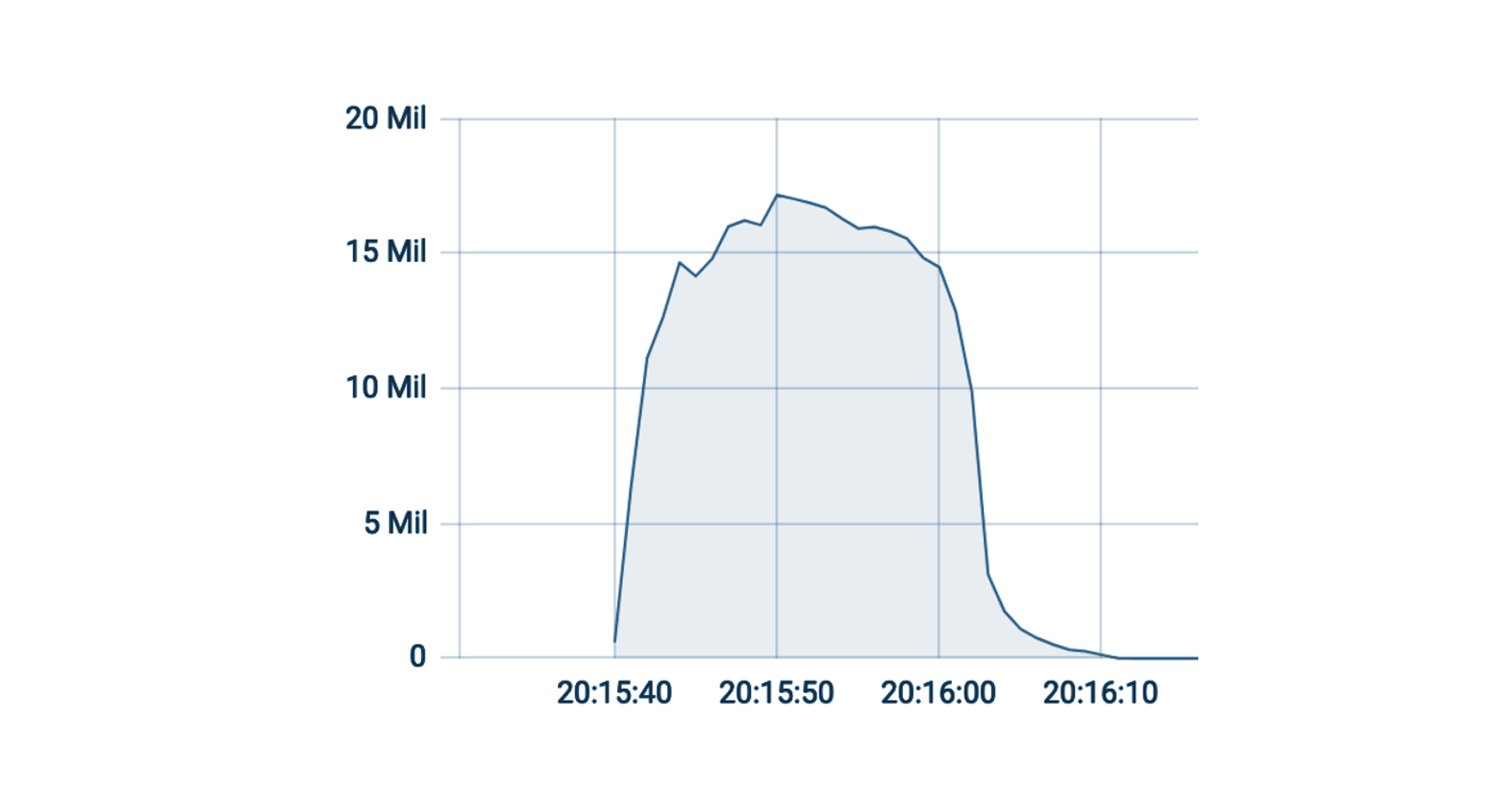
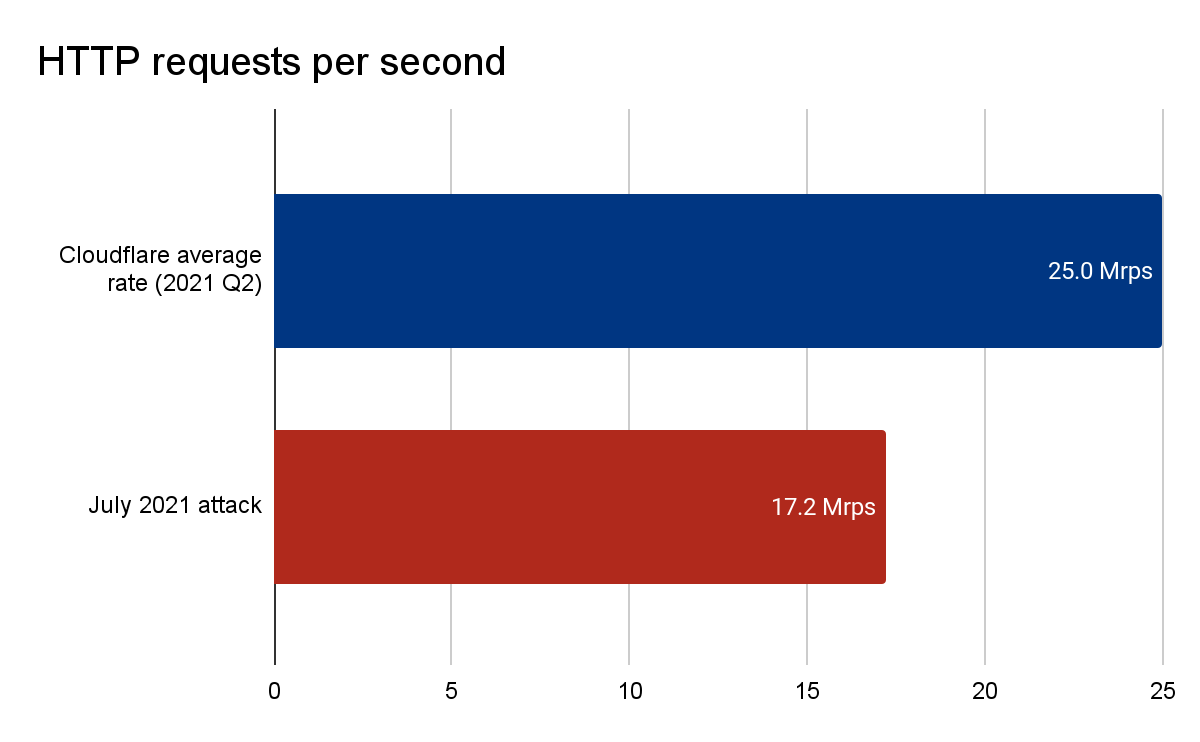
Earlier this summer, Cloudflare’s autonomous edge DDoS protection systems automatically detected and mitigated a 17.2 million request-per-second (rps) DDoS attack, an attack almost three times larger than any previous one that we're aware of. For perspective on how large this attack was: Cloudflare serves over 25 million HTTP requests per second on average. This refers to the average rate of legitimate traffic in 2021 Q2. So peaking at 17.2 million rps, this attack reached 68% of our Q2 average rps rate of legitimate HTTP traffic.
Automated DDoS mitigation with Cloudflare’s autonomous edge
This attack, along with the additional attacks provided in the next sections, were automatically detected and mitigated by our autonomous edge DDoS protection systems. The system is powered by our very own denial of service daemon (dosd). Dosd is a home-grown software-defined daemon. A unique dosd instance runs in every server in each one of our data centers around the world. Each dosd instance independently analyzes traffic samples out-of-path. Analyzing traffic out-of-path allows us to scan asynchronously for DDoS attacks without causing latency and impacting performance. DDoS findings are also shared between the Continue reading
3 Common Network Visibility Mistakes Security Managers Make
To maximize network visibility, an enterprise has to think beyond its own pipes and think about all the networks it does business on.Hedge 96: Mark Nottingham and the Future of Standardization

It often seems like the IETF is losing steam—building standards, particularly as large cloud-scale companies a reducing their participation in standards bodies and deploying whatever works for them. Given these changes, what is the future of standards bodies like the IETF? Mark Nottingham joins Tom Ammon and Russ White in a broad-ranging discussion around this topic.
Nokia Service Router Linux
Nokia Service Router Linux (SR-Linux) is an open source network operating system running on Nokia's merchant silicon based data center switches.
The following commands configure SR-Linux to sample packets at 1-in-10000, poll counters every 20 seconds and stream standard sFlow telemetry to an analyzer (192.168.10.20) using the default sFlow port 6343:
system {
sflow {
admin-state enable
sample-rate 10000
collector 1 {
collector-address 192.168.10.20
network-instance default
source-address 192.168.1.1
port 6343
}
}
}For each interface:
interface ethernet-1/1 {
admin-state enable
sflow {
admin-state enable
}
}Enable sFlow on all switches and ports in the data center fabric for comprehensive visibility.
An instance of the sFlow-RT real-time analytics software converts the raw sFlow telemetry into actionable measurements to drive operational dashboards and automation (e.g. DDoS mitigation, traffic engineering, etc.).docker run --name sflow-rt -p 8008:8008 -p 6343:6343/udp -d sflow/prometheusA simple way to get started is to run the Docker sflow/prometheus image on the sFlow analyzer host (192.168.10.20 in the example config) to run sFlow-RT with useful applications to explore the telemetry. Access the web interface at http://192.168.10.20:8008.
Zero Trust controls for your SaaS applications
Most teams start that journey by moving the applications that lived on their private networks into this Zero Trust model. Instead of a private network where any user on the network is assumed to be trusted, the applications that use Cloudflare Access now check every attempt against the rules you create. For your end users, this makes these applications just feel like regular SaaS apps, while your security teams have full control and logs.
However, we kept hearing from teams that wanted to use their Access control plane to apply consistent security controls to their SaaS apps, and consolidate logs from self-hosted and SaaS in one place.
We’re excited to give your team the tools to solve that challenge. With Access in front of your SaaS applications, you can build Zero Trust rules that determine who can reach your SaaS applications in the same place where your rules for self-hosted applications and network access live. To make that easier, we are launching guided integrations with the Amazon Web Services (AWS) management console, Zendesk, and Salesforce. In just a few minutes, your team can apply a Zero Trust layer over every resource you use and ensure your logs Continue reading
The First Three Winners from Cloudflare’s Project Jengo 2 Share $20,000
This past April we announced the revival of Project Jengo in response to a patent troll called Sable Networks that sued Cloudflare even though our technology and products are nothing like what’s described in Sable’s patents. This is only one part of Sable’s larger campaign against innovative technology companies — Sable sued five other technology companies earlier this year, and had sued seven other technology companies under the same patents last year.
Just as we have done in the past, we decided to fight back rather than feed the troll — which would only make it stronger. You see, unlike Cloudflare and other operating companies that were sued, Sable Networks isn’t in the business of providing products and services to the market. Rather, it exists to extract settlements out of productive companies that are creating value to the society.
Project Jengo is a prior art search contest where we ask the Cloudflare community for help in finding evidence (“prior art”) that shows Sable’s patents are invalid because they claim something that was already known at the time the patent application was filed. We committed $100,000 in cash prizes to be shared by the winners who were successful in finding Continue reading
Capturing Purpose Justification in Cloudflare Access
The digital world often takes its cues from the real world. For example, there’s a standard question every guard or agent asks when you cross a border—whether it’s a building, a neighborhood, or a country: “What’s the purpose of your visit?” It’s a logical question: sure, the guard knows some information—like who you are (thanks to your ID) and when you’ve arrived—but the context of “why” is equally important. It can set expectations around behavior during your visit, as well as what spaces you should or should not have access to.
Digital access follows suit. Recent data protection regulations, such as the GDPR, have formalized concepts of purpose limitation and data proportionality: people should only access data necessary for a specific stated reason. System owners know people need access to do their job, but especially for particularly sensitive applications, knowing why a login was needed is just as vital as knowing who, when, and how.
Starting today, Cloudflare for Teams administrators can prompt users to enter a justification for accessing an application prior to login. Administrators can add this Continue reading
Day Two Cloud 111: Infrastructure As Software With Kris Nóva
Kris Nóva, Senior Principal Software Engineer at Twilio, claims that managing infrastructure using tools like Terraform isn't that far away from just writing your own code to do the job yourself. Kris joins co-hosts Ned Bellavance and Ethan Banks to challenge the notion that ops folks can't become developers. Kris says they can.
The post Day Two Cloud 111: Infrastructure As Software With Kris Nóva appeared first on Packet Pushers.
Day Two Cloud 111: Infrastructure As Software With Kris Nóva
Kris Nóva, Senior Principal Software Engineer at Twilio, claims that managing infrastructure using tools like Terraform isn't that far away from just writing your own code to do the job yourself. Kris joins co-hosts Ned Bellavance and Ethan Banks to challenge the notion that ops folks can't become developers. Kris says they can.How To Become A Mentor In Your Career Field
Becoming a mentor doesn’t just help others. It enables you to enhance your professional development too. That is because it is a mutually beneficial partnership that helps both parties involved, i.e., the mentor and mentee.
If you are looking to become a mentor, you are in the right place. Here are the top tips that will help you in how to become a mentor in your career field.
1. Find A Mentee
You can use your organization or professional network to find a mentee. However, many of the best mentoring relationships develop organically without you having to try. If you feel there is a junior in your organization that you offer advice to, you can always become their mentee.
Mentoring programs inside the organization are an excellent way to engage the staff, retain employees, and pass expertise. So, if you have such a program in your organization, you will find a mentee in no time.
2. Set Expectations
Once you have found a mentee in your organization, it is time to set expectations. That is because establishing guidelines help maintain a good working relationship. Your mentee will know what you expect and vice versa. Continue reading
Automation Simplifies Mobile Transport Network Rollouts
Automation to simplify the provisioning and configuration of transport network elements (NEs) will be key to performing much of the arduous tasks required to get equipment up and running.Register for the 5th Annual Indigenous Connectivity Summit

In its second year as a virtual event, the Indigenous Connectivity Summit will take place on 12-15 October 2021. The COVID-19 pandemic showed us that those who lack connectivity face the effects of starker inequalities. Millions of people across Canada and the United States still can’t take advantage of the benefits of a fast, affordable, […]
The post Register for the 5th Annual Indigenous Connectivity Summit appeared first on Internet Society.

